F5 BIG-IP Next WAF Labs > Module 2: Deploy an application using FAST template and assign a WAF policy Source |
Lab 2.1 - Deploy an application using FAST template and the WAF Violation Rating policy template¶
This part of the lab covers how to create and deploy an application and protect it with a WAF policy using the FAST template and the WAF “Rating-Based-Template” with the focus on ease of use and little policy maintenance.
Note: The violation rating based template follows the same concept as you may know already from NGINX App Protect, which is low false positives with little policy maintenance and therefore the Policy Builder is not supported with the violation rating based template.
Backend web apps are available and configured on the internal network running which the Ubuntu Jump Host is on.
- OWASP Juice Shop: 10.1.20.100, 10.1.20.101, 10.1.20.102, 10.1.20.103 on port 3000.
- Simple F5 demo web app 10.1.20.100, 10.1.20.101, 10.1.20.102, 10.1.20.103 on port 8080.
Deploy a HTTPS Load Balancer with a WAF policy¶
1. Start the “Windows Jump Host” and login as explained in module 0 and login to the BIG-IP Next Central Manager from the Windows Jump Host or directly from your local browser as explained in module 0.
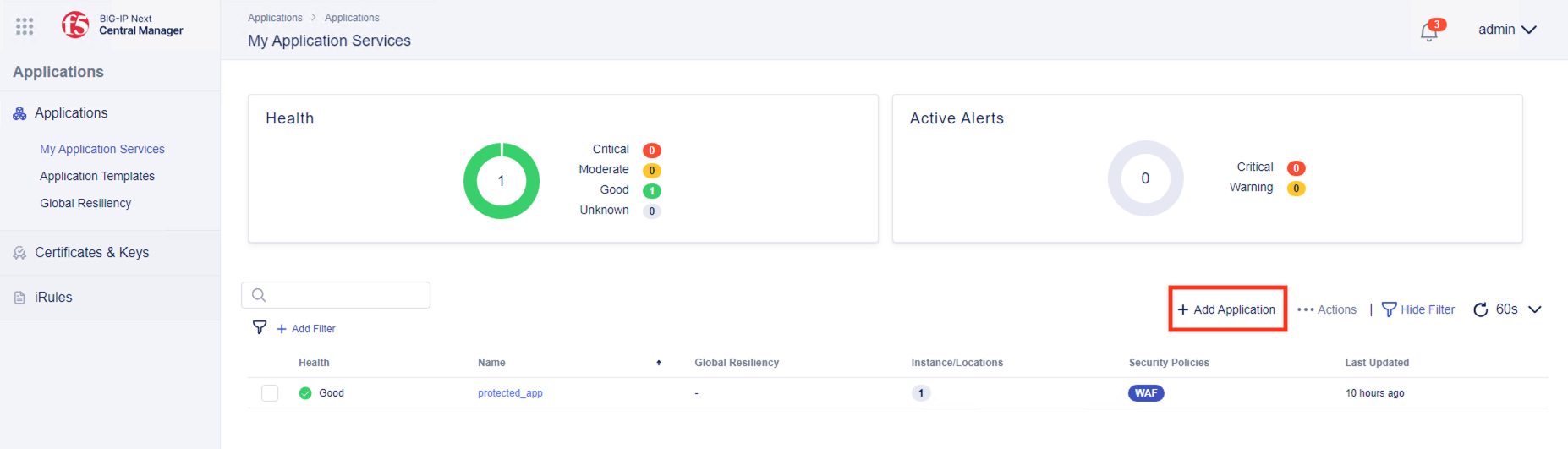
2. From “Applications - My Application Services” click on “+ Add Application”
3. Enter “juice_lab_app” for the “Application Service Name”, select “From Template” and click on “Select Template”
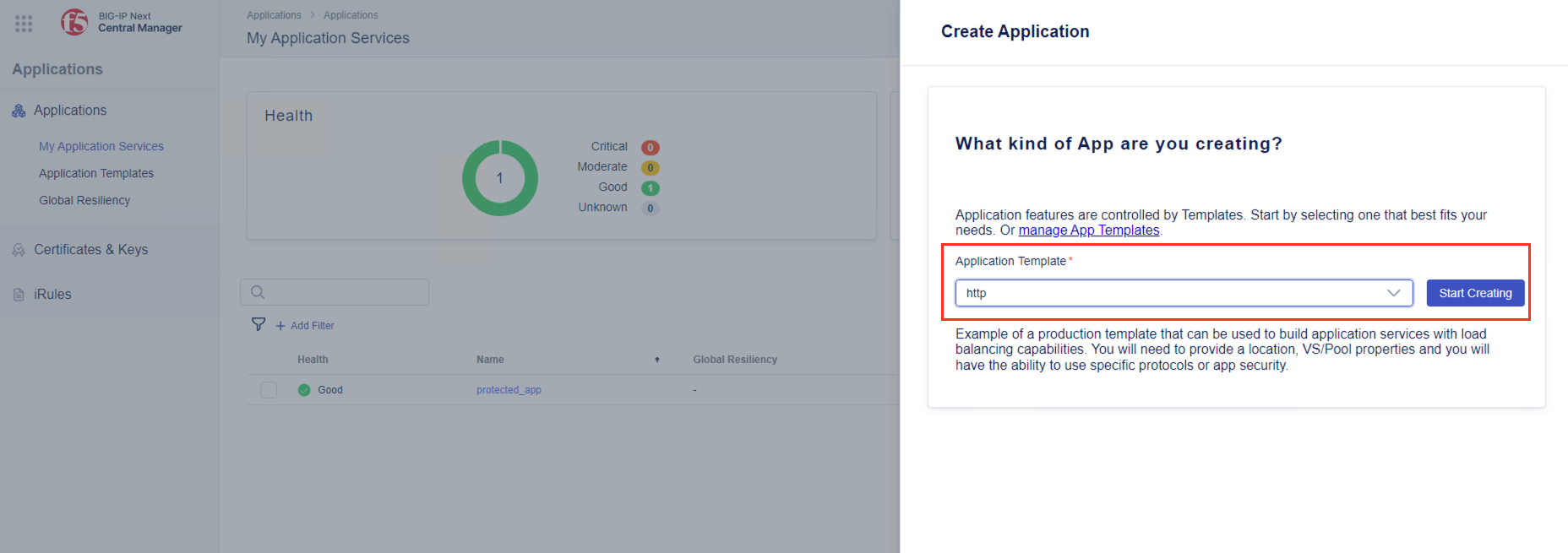
4. Choose the “http” template and click on “Start Creating”
5. Click on “Start Creating” for Virtual Servers again
Note: For the next step, make sure you enter the right port number for the Pool and the Virtual Server. It seems there is an issue currently during entering the port number.
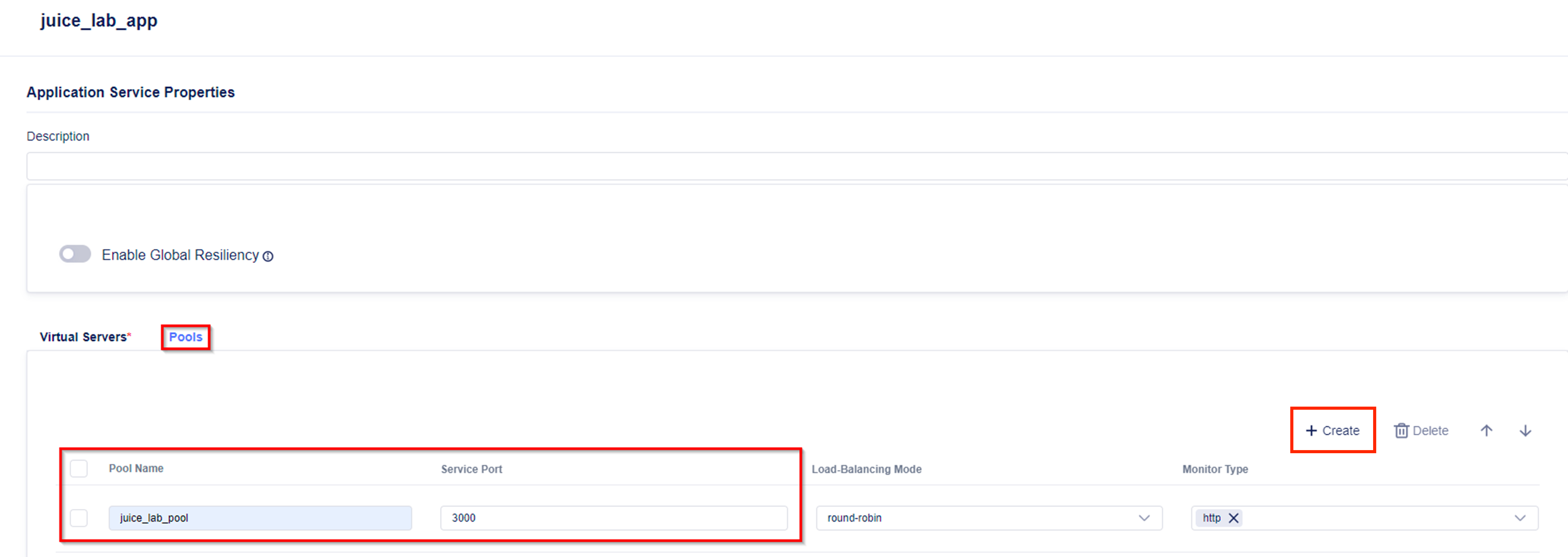
6. Click on “Pools”
- Select “Create”
- Enter the name “juice_lab_pool” and the port number “3000”
7. Click on “Virtual Server”
- Enter the name “juice_lab_vs”
- Select the pool you just created before, “juice_lab_pool” from the drop down menu
- Enter the port 443

8. Click on “Edit” for “Protocols & Profiles”

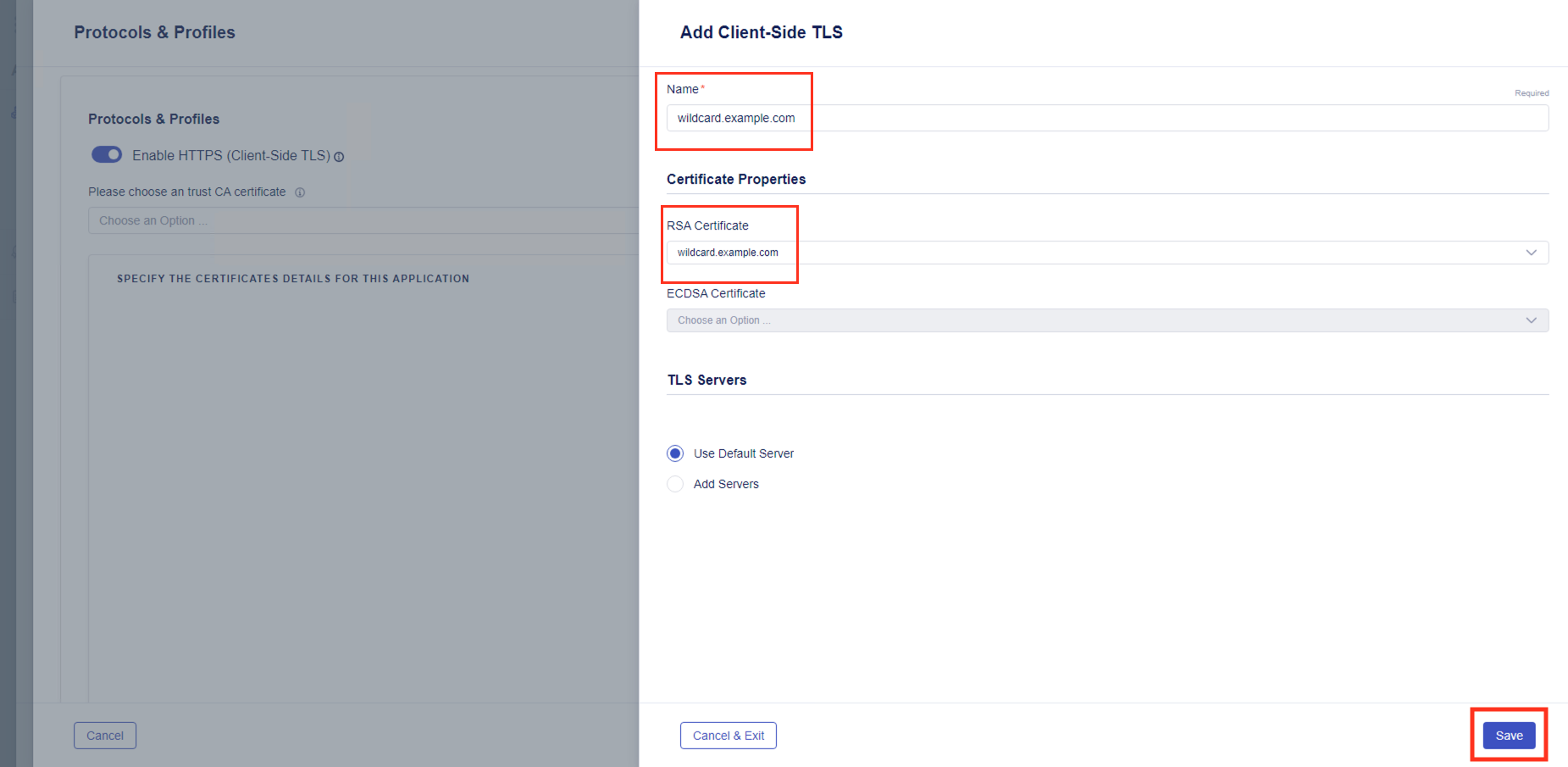
- Enable HTTPS (Client-Side TLS)
- Select “Add”

- Name the cert “wildcard.example.com”
- Under the RSA Certificate drop down, choose the cert “wildcard.example.com”
- Click on “Save” twice to bring you back to the previous screen
9. Click on “Edit” for “Security Policies”
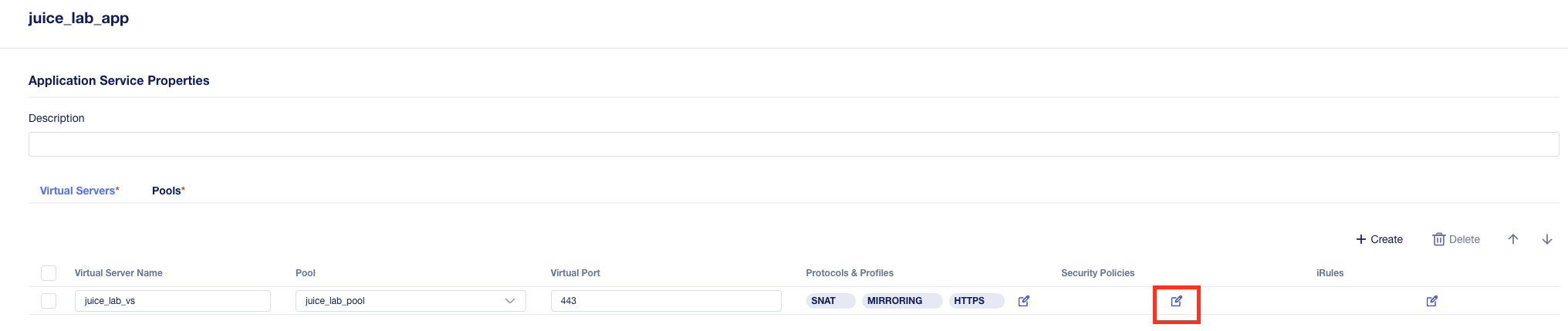
- Enable “Use a WAF Policy”
- Click on “Create” to create a new WAF policy
- Enter the “Name” “juice_lab_policy”
- Enable “Advanced View” to show that by default the Rating-Based-Template and UTF-8 is configured. We leave the default settings and will create another policy with a different template in a later module.
- Note: Bot Defense, Threat Campaigns and IP Intelligence are enabled by default.
- Click “Save” twice to bring you back to the previous screen

- Click “Review & Deploy”
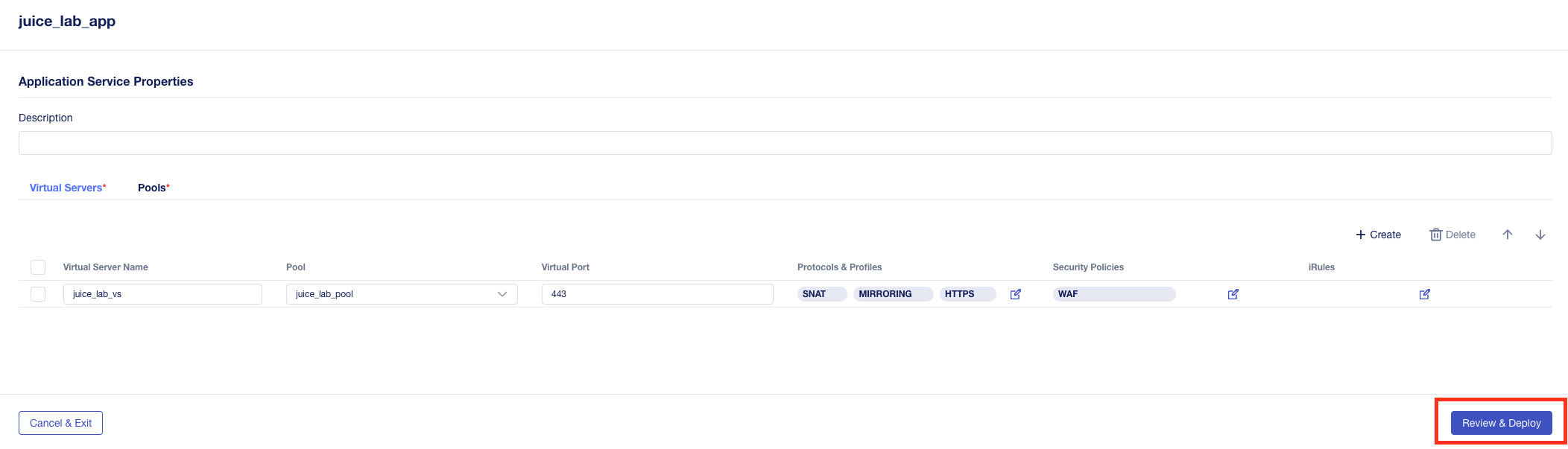
Note: You finished the configuration of the generic part and the instance/locations specific part is configured in the next step. For this example we use only one location.
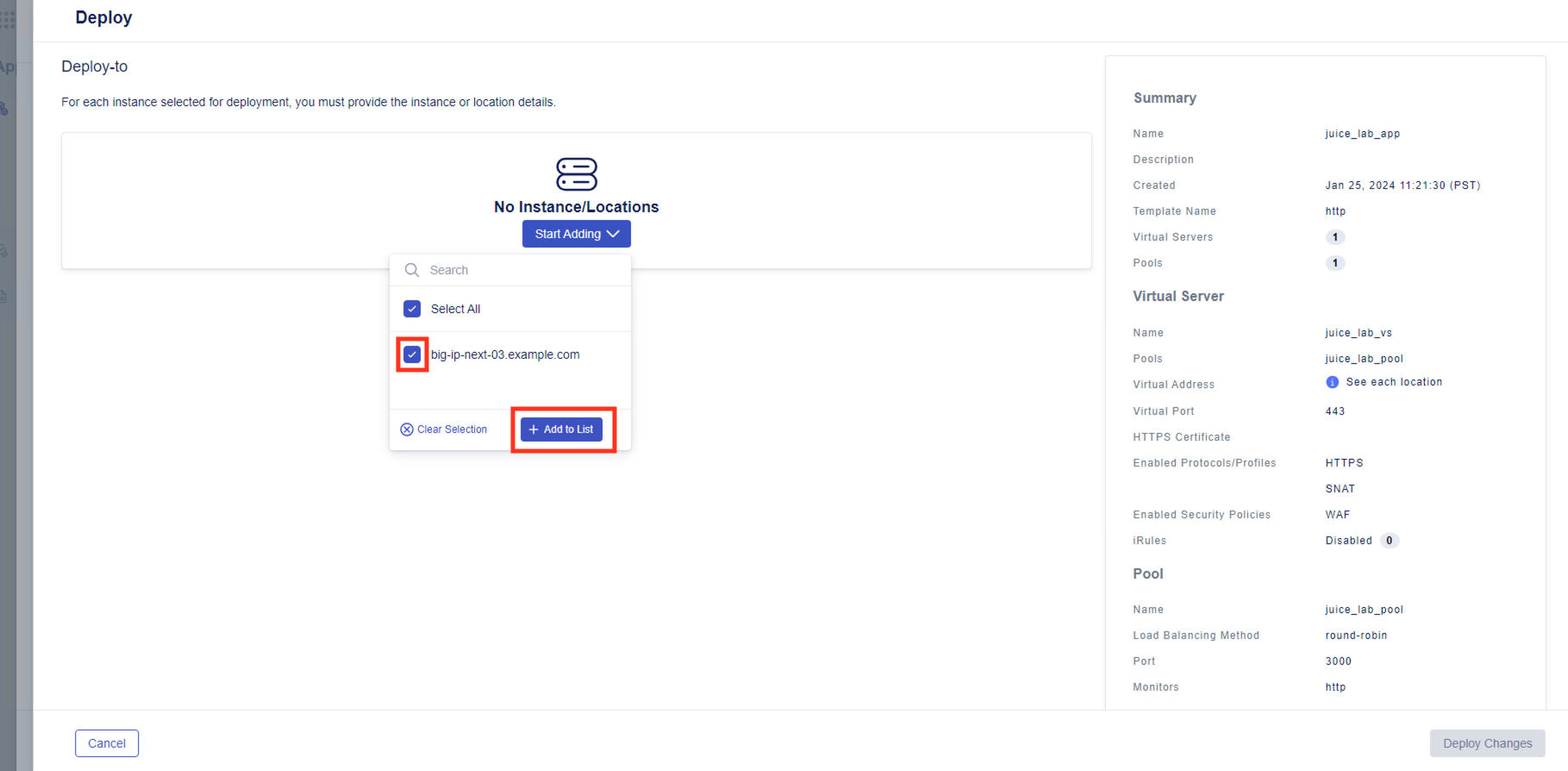
10. Click on “Start Adding” Instance/Locations to start the site specific configuration
- Select “big-ip-next-03.f5demo.com”
- Click on “Add to List”
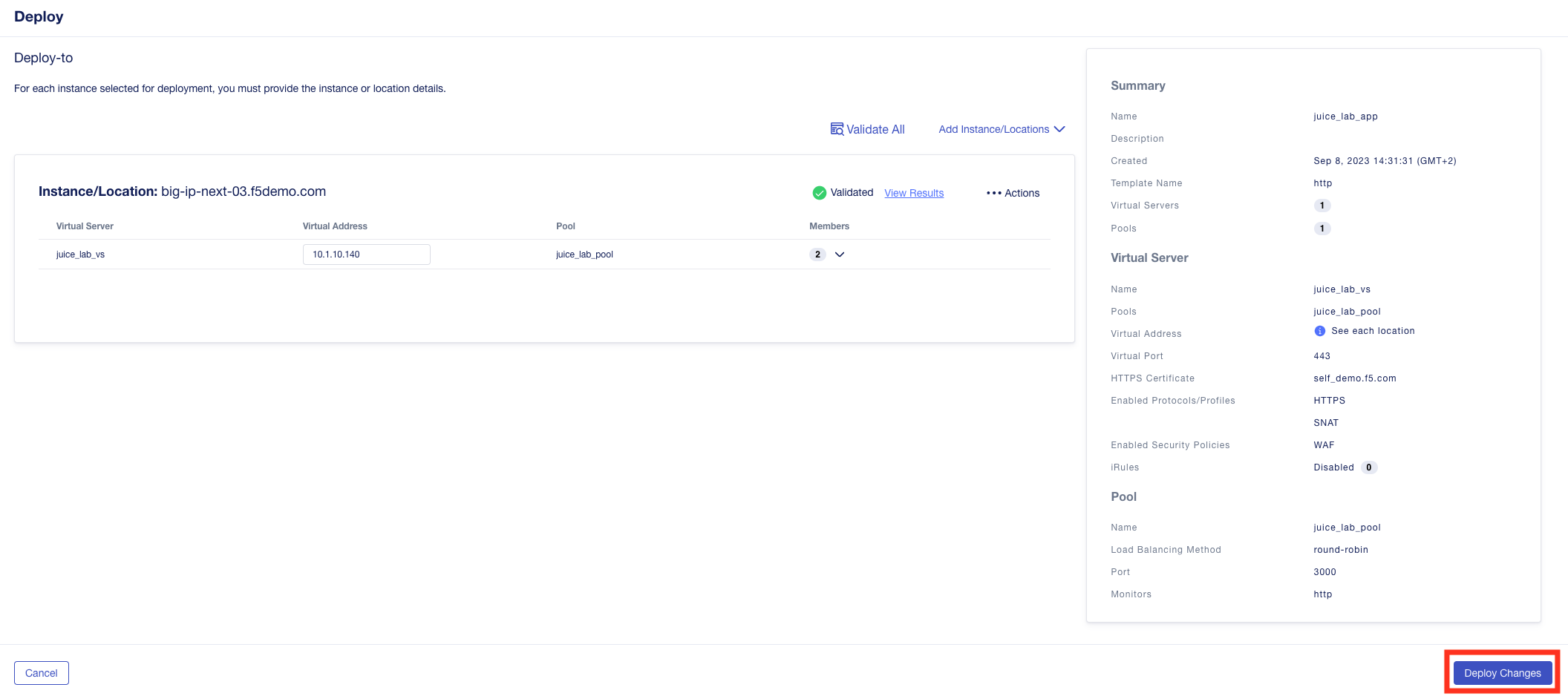
11. Configuration of the instance/location specific parts like the Virtual Address and Pool Members
- Enter the Virtual Address “10.1.10.140”
- Click on “Members” dropdown - then “+ Pool Members”
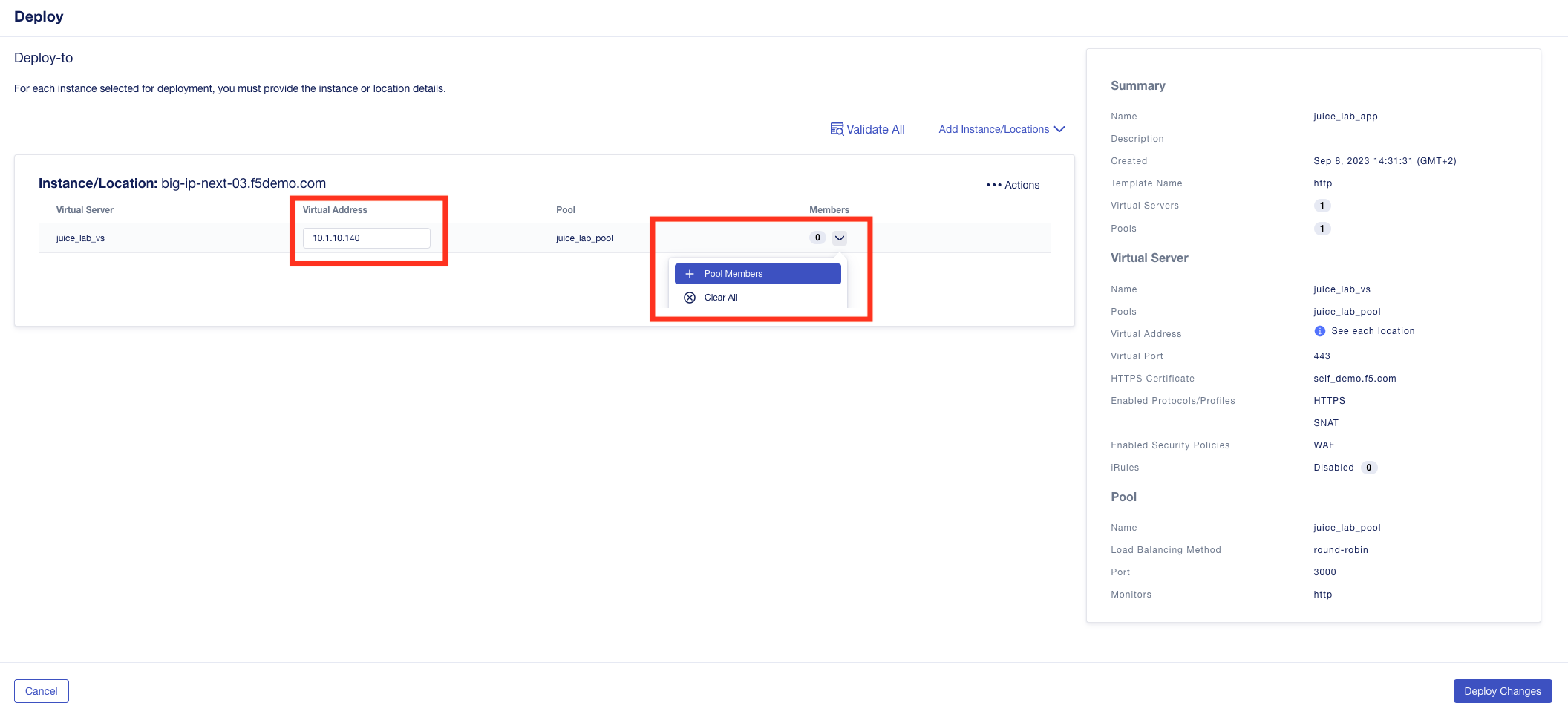
- Click on “Add Row” and add both pool members
- Name: node1 and IP Address: 10.1.20.100
- Name: node2 and IP Address: 10.1.20.101
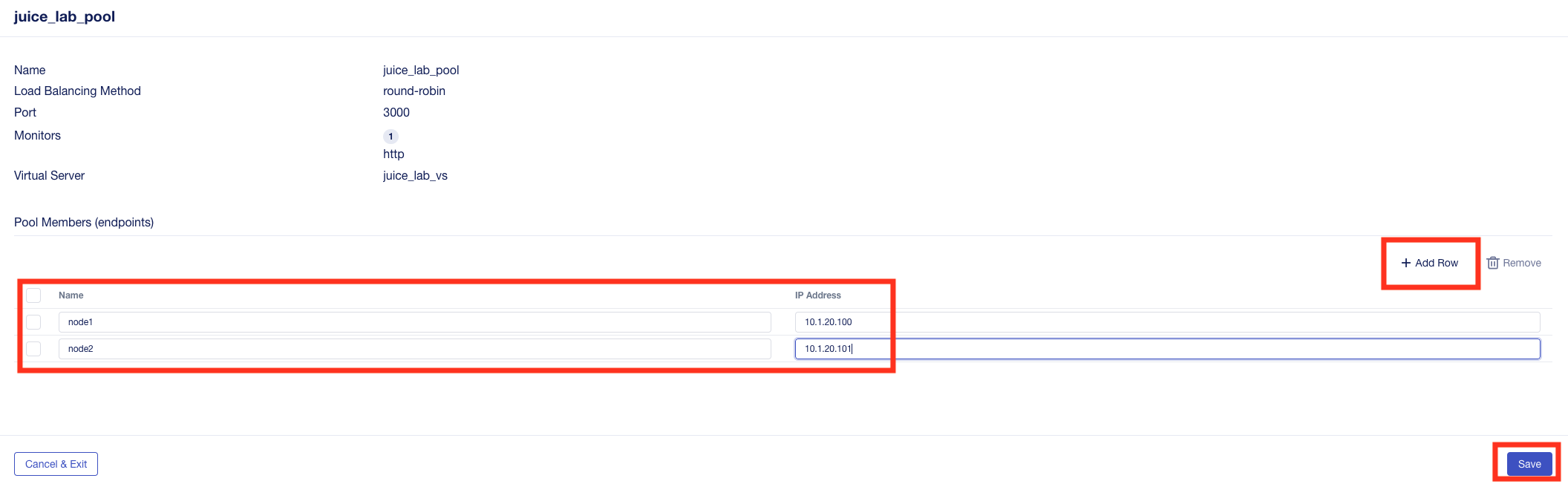
- Click “Save” to return to the previous screen
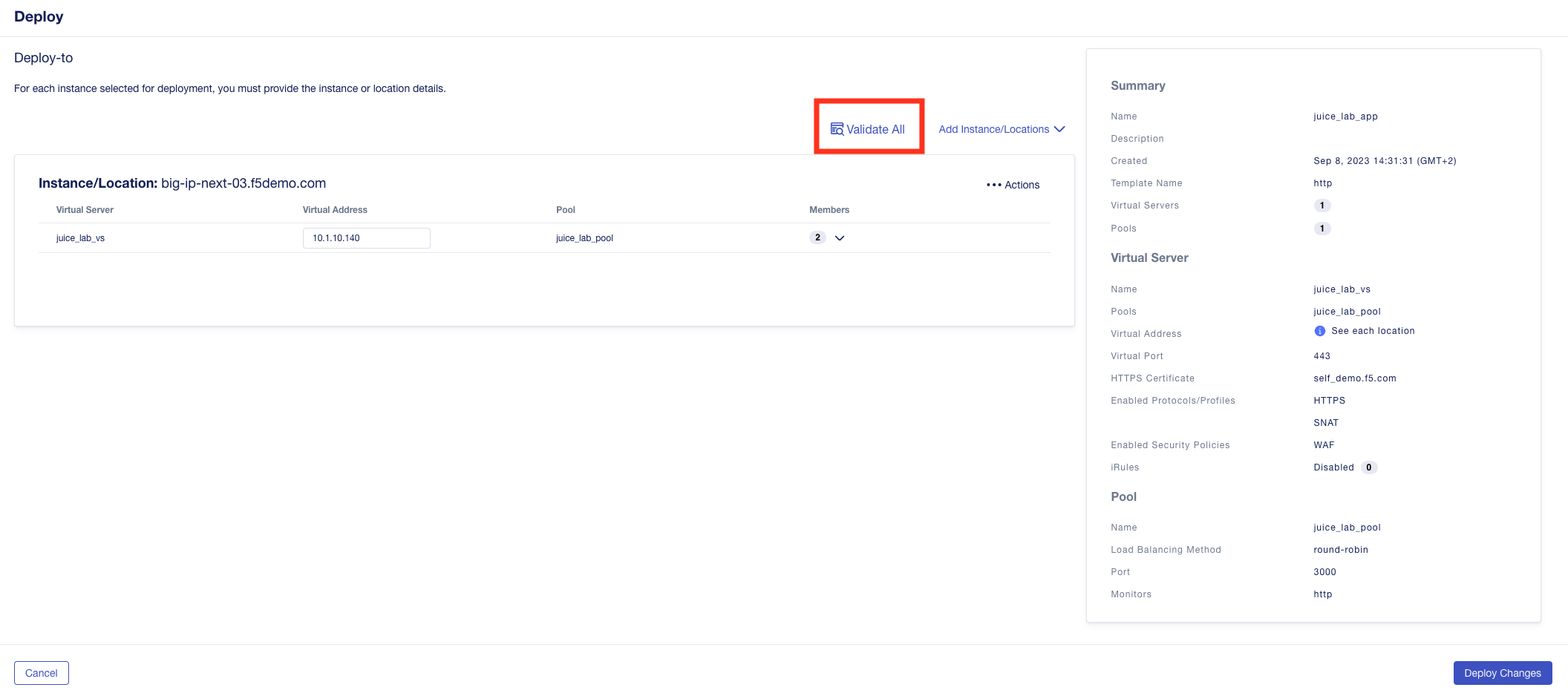
- click “Validate All” to validate the configuration
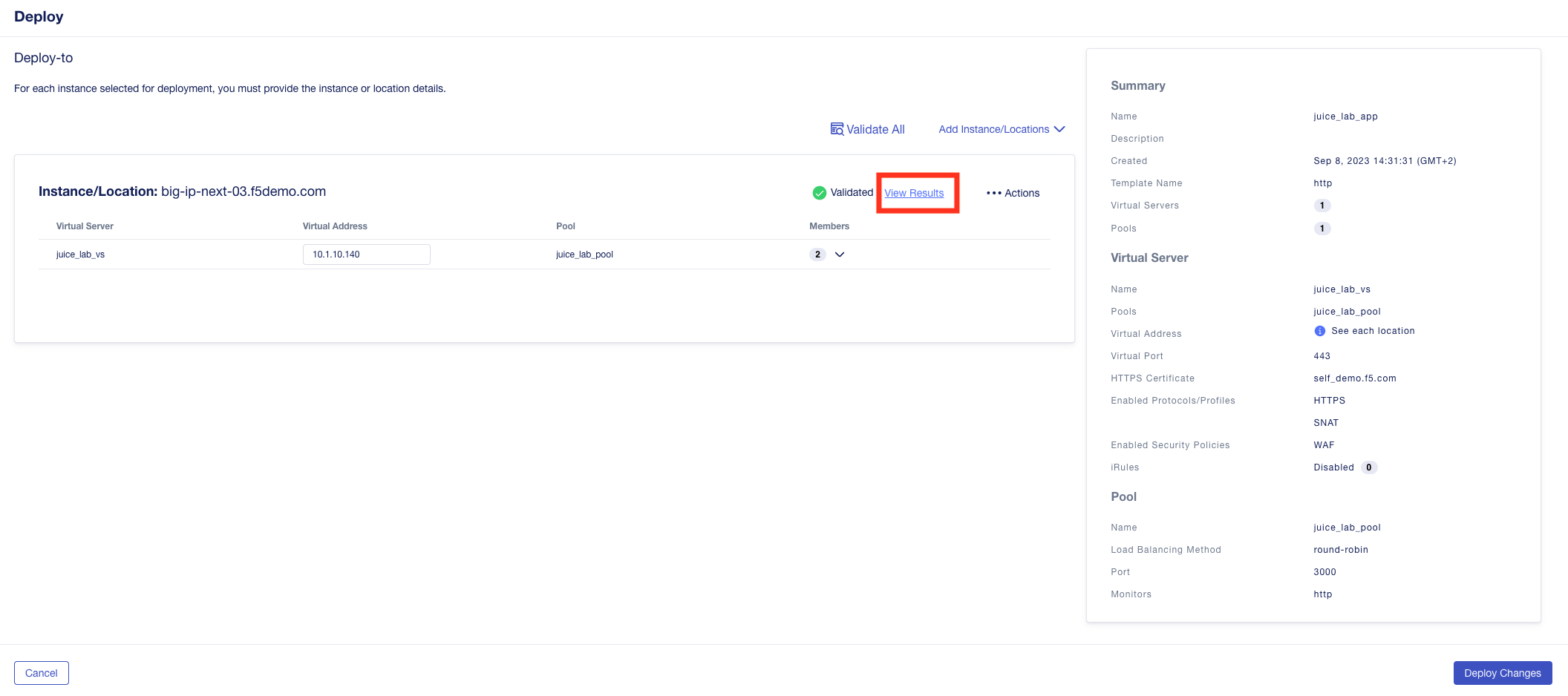
- Click “View Results” to show the declaration
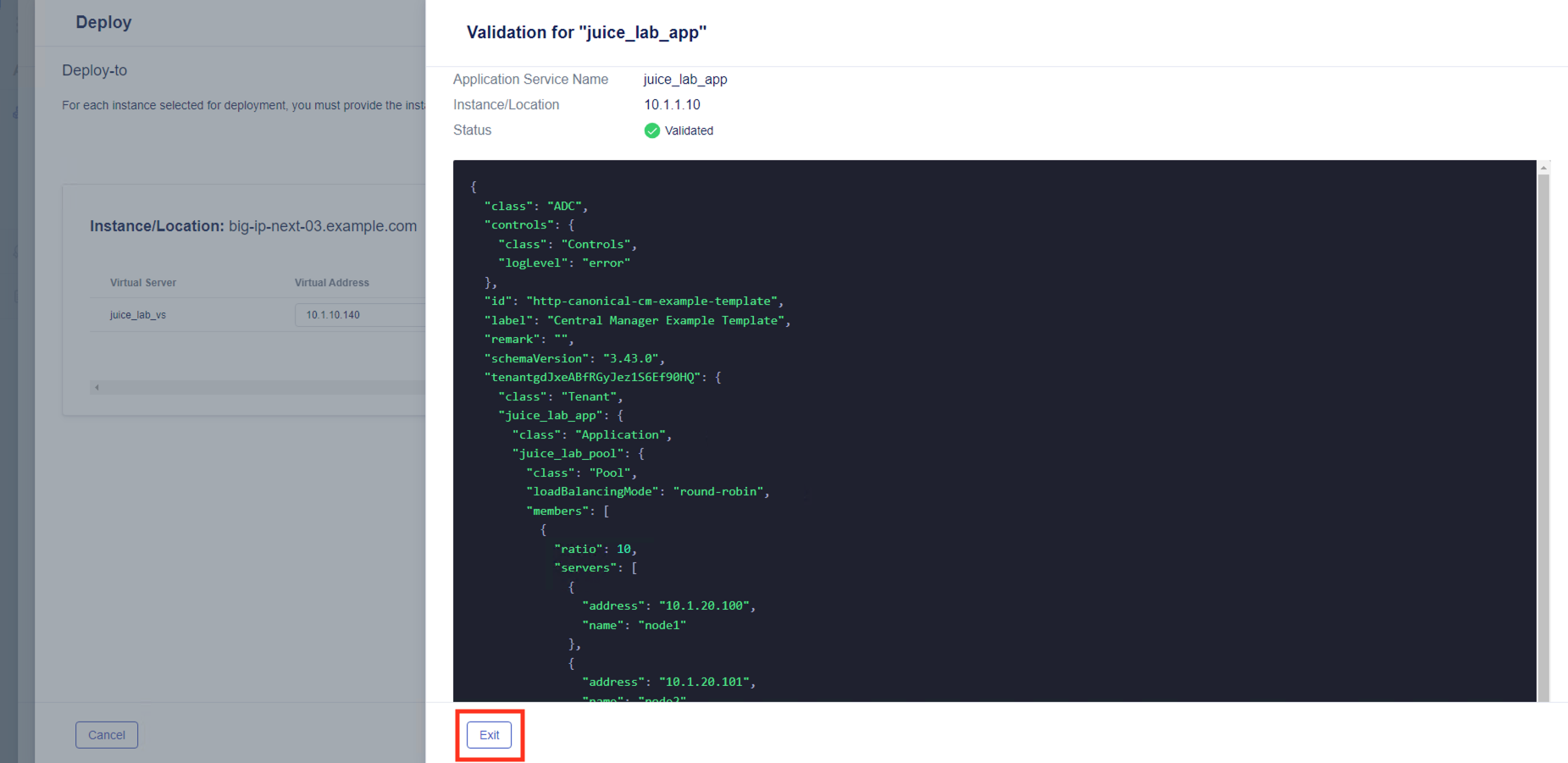
- Click “Exit” and “Deploy Changes”
- Confirm by selecting “Yes, Deploy”
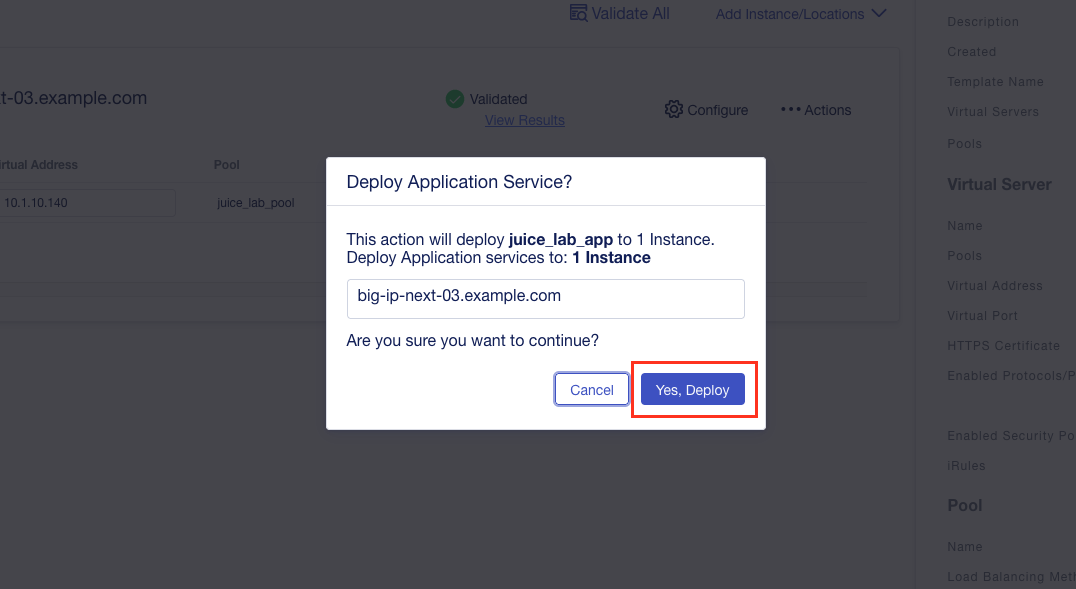
- After deploying, you should see the app and the WAF policy deployed

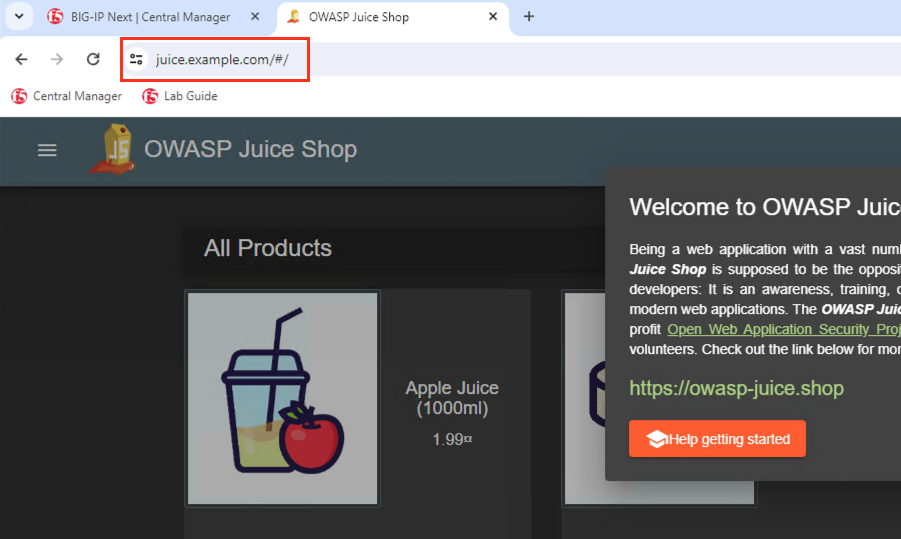
12. Now let’s go to the Windows Jump Host and check it out
Open Chrome, go to https://juice.example.com and you should see the Juice Shop app. (The lab environment already has a host entry configured for “juice.example.com” to resolve to “10.1.10.140”)
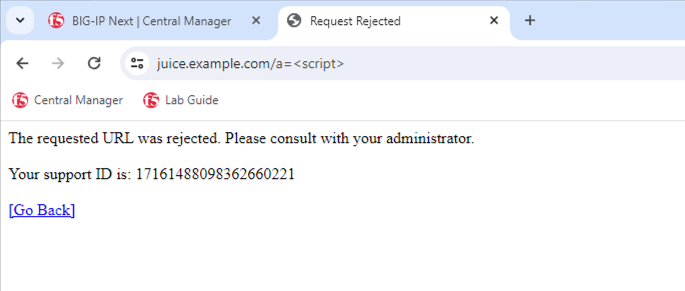
Enter “https://juice.example.com/a=<script>” and you should see the blocking page.
13. Finally let’s check the BIG-IP Next Central Manager WAF Security Dashboard
Go back to the Central Manager and follow the steps shown in the short video below.
- Click the menu icon in the top left
- Go to the “Security” section
- Under “Monitoring” select “WAF Dashboards”
- In the policies section of the dashboard, hover over the “juice_lab_policy” and select the “…” menu
- Select “Filter by Policy Name”
- In the “Attack URLS” section of the dashboard, click on the attacked URL we used “/a=<script>”
- Click on “View Logs”
- Click on the event itself to get the details
The dashboard allows actions too.
- In the “Signatures” section of the dashboard, select the triggered signature (200000093)
- Click on “Actions”
- You can change the enforcement setting for that signature and also decide what policy it should be applied to
Congratulations - You have finished Module 2