F5 Fraud Protection Solutions > Class 1: Introduction to Fraud and F5 WebSafe Source | Edit on
Lab Network Setup¶
In the interest of focusing as much time as possible seeing malware and phishing detection and protection in action, we have provided some resources and basic setup ahead of time. These are:
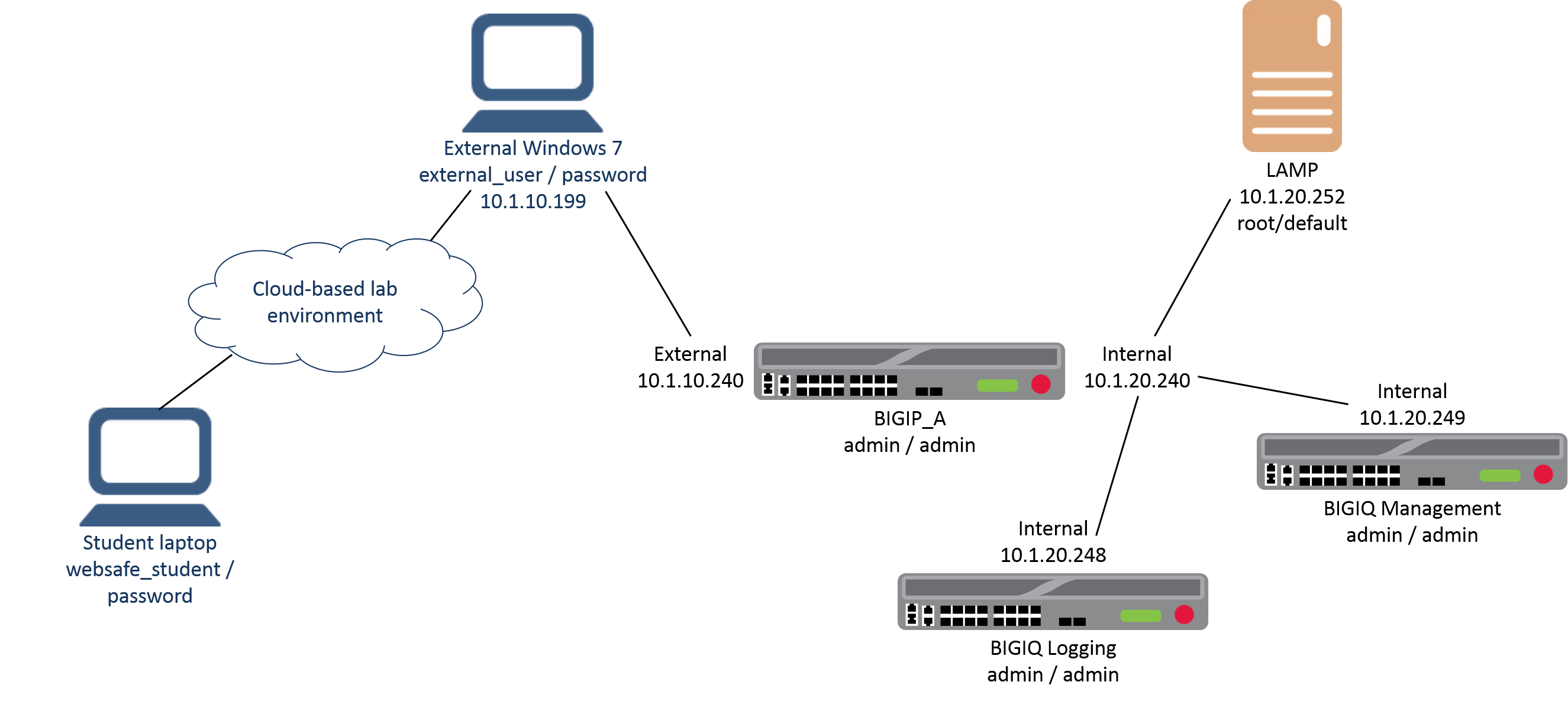
- Cloud-based lab environment complete with an infected Windows workstation, a virtual BIG-IP (VE), a virtual BIG-IQ acting as a logging node, a virtual BIG-IQ acting as a management node, and a back-end banking application running on a Linux web server.
- The virtual BIG-IP has been pre-licensed and provisioned for WebSafe
If you wish to replicate these labs in your office you will need to perform these steps accordingly. Additional lab resources are provided as illustrated in the diagram on the next page.
To access the lab environment, you will require a web browser and Remote Desktop Protocol (RDP) client software. The web browser will be used to access the lab training portal. The RDP client will be used to connect to a Windows workstation, where you will be able to access the BIG-IP and BIG-IQ management interfaces (HTTPS, SSH).
You class instructor will provide additional lab access details.
Lab Diagram¶
Timing for Labs¶
The time it takes to perform each lab varies and is mostly dependent on accurately completing steps. This can never be accurately predicted but we strived to derive an estimate among several people each having a different level of experience. Below is an estimate of how long it will take for each lab:
| LAB Name (Description) | Time Allocated |
|---|---|
| LAB 1 – Examine the Dangers of Malware and Phishing) | 25 minutes |
| LAB 2 – Use Malware Detection) | 30 minutes |
| LAB 3 – Use Phishing Detection | 30 minutes |
| LAB 4 – Use Application Layer Encryption | 30 minutes |