3.4. Creating an ICAP Service¶
3.4.1. What it is¶
The Internet Content Adaption Protocol (ICAP) is defined by RFC3507 and constitutes an encapsulation protocol. Packets are encapsulated by an ICAP client and passed to an ICAP server. What the ICAP server does with the encapsulated data depends on the underlying service, and typically ranges from malware and antivirus detection, to data loss prevention (DLP). An ICAP device is defined by the following primary characteristics:
Layer 3: It contains at least one network interface with assigned IP address as its listening interface for encapsulated ICAP queries.
ICAP-enabled service: It is running at least one service that is accessible through an ICAP interface and adheres to RFC3507.
SSL Orchestrator as the ICAP client directs traffic to a listening IP address and port on the ICAP server.
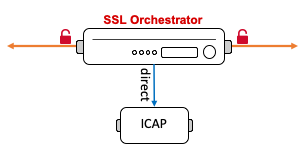
Figure 34: ICAP service
Many modern security products fit into this category, including products by Symantec, McAfee and Digital Guardian. SSL Orchestrator defines an ICAP service is an ICAP client interface that performs the encapsulation and forwards queries to an ICAP server.
3.4.2. How to build it¶
Either from a topology workflow or directly under the Services tab in the SSL Orchestrator user interface, click the Add button to create a new inline HTTP service.
| ICAP Service | User Input |
|---|---|
| Service Properties | Choose an ICAP service from the catalog or select the “Generic ICAP Service” and click the Add button. |
| Name | Provide a name for this service. |
| Description | Optionally provide a description. |
| IP Family | Choose between IPv4 and IPv6. |
| ICAP Devices | This setting defines the entry point IP address and listening port of the ICAP service. Multiple IP addresses and ports can be assigned here to load balance multiple ICAP devices. Click the Done button to add each device. |
| Device Monitor | Optionally define an alternate monitor. In most cases the default tcp monitor is preferable for ICAP services. |
| ICAP Headers | In the event that custom headers are needed at the ICAP server, this setting optionally allows for simple, static configuration of these headers, but is usually not required. |
| OneConnect | This setting enables OneConnect optimization to re-use server-side TCP connections for optimal communication with the ICAP server. It is recommended to leave this enabled (checked). |
| Request Modification URI Path | Enter the request modification URL path specific to this ICAP product. Consult with the ICAP product’s documentation, as each vendor’s service paths will be different. However, the “traditional” URL path is “/REQMOD”. |
| Response Modification URI Path | Enter the response modification URL path specific to this ICAP product. Consult with the ICAP product’s documentation, as each vendor’s service paths will be different. However, the “traditional” URL path is “/RESPMOD”. |
| Preview Max Length(bytes) | Enter the max preview length value here. Consult with the ICAP product’s documentation, as each vendor’s preview length setting will be different. For many ICAP products, however, the value would be 0 (zero), indicating full streaming support. |
| Service Down Action | Optionally select an alternate service down action. This setting defines what happens if all devices in a service pool are down and will either ignore (skip this service in the chain), reset, or drop the traffic. |
| HTTP Version | Select either HTTP/1.0 & HTTP/1.1, or HTTP/1.1 only, depending on what the ICAP server supports. |
| ICAP Policy | Select an existing ICAP policy here to control when SSL Orchestrator sends ICAP requests and responses. |
Click Save & Next to proceed.
The workflow will proceed to the Service Chains page to allow adding of this new service to a service chain. Once complete here, if in a topology workflow click Save & Next to continue. If adding the service directly, click the Deploy button.
3.4.3. How it works¶
SSL Orchestrator uses the following configuration information to correctly ICAP-encapsulate packets and address an ICAP server or load balanced set of servers.
Service Properties - the Service Properties page represents a Service Catalog of validated product integrations and represents each of the five security product types. If your security product is not listed, there are also “generic” service icons at the bottom of the catalog.
ICAP Devices - an ICAP service may be defined as the load balances set of multiple devices on the same IP subnet. Minimally one device IP address and listening port must be defined.
Device Monitor - the device monitor for an ICAP service performs an active health check on its pool members. The default tcp monitor if fine for most ICAP service definitions, but it may be useful to create and assign a more thorough monitor to more deeply test viability of the ICAP servers.
ICAP Headers - this option provides a set of optional, static headers to pass to the ICAP server.
OneConnect - OneConnect transformation is a TCP connection re-use optimization that provides a mechanism to minimize the amount of connections and connection tear downs that must happen to an ICAP server. It is recommended to leave this setting enabled.
Request Modification URI Path - an ICAP-enabled security product will run at least one security function but may contain multiple. The ICAP interface will differentiate these services by a unique URL, similar to an HTTP URL. An ICAP server will also often differentiate request traffic from response traffic, thus this setting will set the URL path for request traffic flows (client to server).
Response Modification URI Path - an ICAP-enabled security product will run at least one security function but may contain multiple. The ICAP interface will differentiate these services by a unique URL, similar to an HTTP URL. An ICAP server will also often differentiate request traffic from response traffic, thus this setting will set the URL path for response traffic flows (server to client).
Preview Max Length(bytes) - preview is an ICAP option for sending a “sample” of a packet to an ICAP server. The ICAP server may then decide if it wants to see more of the packet and respond accordingly. If the ICAP server supports and recommends a preview length, specify it here. Otherwise most ICAP vendor products support and recommend the streaming option, whereby preview length is set to 0 (zero) and the ICAP client streams the packet payload.
Service Down Action - a security service defines a pool of one or more load balanced and monitored devices. Depending on the state of the monitor, a different action may be taken. It may be most appropriate, for example, to simply bypass a failed service (i.e. all of the members are down) in order to maintain availability.
HTTP Version - this setting will enable full HTTP/1.0 and 1.1 support, or limit to 1.0 depending on what the ICAP server requires.
ICAP Policy - ICAP policies are defined in the F5 BIG-IP user interface under Local Traffic -> Policies and are simply LTM policies that control access to ICAP services based on characteristics of the HTTP request or response. ICAP policy management is covered in more detail in a later chapter.