4.2. Manage SSL Orchestrator in a High Availability Environment¶
4.2.1. What it is¶
High Availability (HA) is a cornerstone of operational efficacy. Networking devices are mostly made of silicon and human ingenuity. But despite this, devices fail. And when they fail, they usually take other things with them…like critical resources. Security devices are no exception. While they may not always block availability (i.e. fail open), loss of a security device means loss of visibility and a loss of protection against malware, denial of service, and exfiltration. Simply put, failing open in the security stack should rarely be an option, and HA is the best way to defend your environment.
The F5 SSL Orchestrator presents multiple paths to high availability:
The F5 device itself is highly available. Device peers maintain full synchronization and a heartbeat to provide millisecond-speed failover when a device goes down.
The security services attached to SSL Orchestrator are in load balanced and actively monitored pools. Traffic is only sent to active, available security devices that can be added and removed from the resource pools with no downtime.
It is also important to note that the combination of TLS offload, and SSL Orchestrator dynamic service chaining, means that security devices are not burdened by the weight of encryption and that traffic a device cannot inspect can be steered around it. This means that existing security products can dedicate more computing power to security functions, thus requiring a smaller overall footprint and generally higher availability.
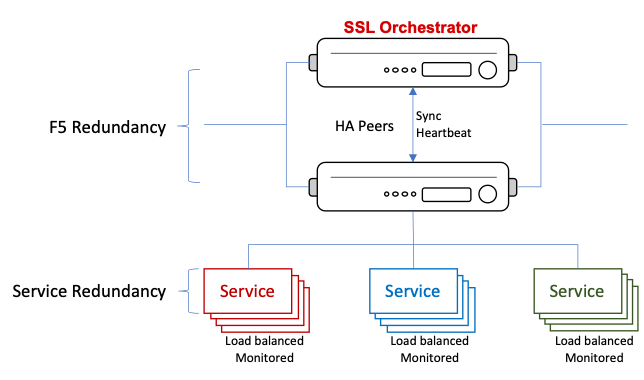
Figure 56: SSL Orchestrator High Availability
In this section we will explore the requirements for SSL Orchestrator HA.
4.2.2. How to build it¶
Current versions of SSL Orchestrator impose the following limitations on HA configuration:
| HA Limitations | User Input |
|---|---|
| HA mode | HA is restricted to two (2) devices in active/standby mode. |
| Sync mode | HA requires MANUAL sync mode, with either full or incremental updates. |
| Device groups | HA supports ONE (1) device group. |
Notably, SSL Orchestrator does not rely on native BIG-IP synchronization processes. Configuration sync is handled directly through a separate REST-based communication between the peers. To create an SSL Orchestrator HA configuration, note these prerequisites:
| HA Configuration | User Input |
|---|---|
| BIG-IP version and provisioning | Both devices must be running the same BIG-IP version with the same licensing and software provision. |
| Sync channel port lockdown | After selecting Network -> Self-IPs, ensure that the Self-IP used for peer synchronization has the Port Lockdown set to either Allow All or Allow Default. SSL Orchestrator sync happens via REST communications on port 443. |
| Time synchronization | After selecting System -> Configuration -> Device -> NTP, ensure that both devices are configured to use NTP and that time is correct (synchronized) on both devices. |
| Initial config sync | Ensure that both devices are synced before deploying the SSL Orchestrator configuration. |
| Non-SSL Orchestrator objects | Ensure that any objects not created by SSL Orchestrator are created on both devices. |
To configure F5 BIG-IP devices for basic HA:
| F5 HA Configuration | User Input |
|---|---|
| Device properties | After selecting Device Management -> Devices, click on the device. |
| On the ConfigSync tab, under Local Address, select the VLAN that will be used for sync information between the peers. For SSL Orchestrator, the self-IP assigned to this VLAN must have Port Lockdown settings at Allow All or Allow Default. Perform this step on both devices. | |
| On the Failover Network tab, click the Add button and select the appropriate Failover Unicast Access. The Management Address is generally acceptable here. Perform this step on both devices. | |
| On the Mirroring tab, minimally select an appropriate Primary Local Mirror Address. Perform this step on both devices. | |
| Device trusts | After selecting Device Management -> Device Trust, under the Device Trust Members tab, click the Add button. Enter the IP address of the peer device and follow the remaining prompts to add the peer. If successful, the peer will also show a device trust member. |
| Device groups | Under Device Management -> Device Groups, click the Create button. |
| Name: Provide a unique name. | |
| Group Type: Select Sync-Failover. | |
| Members: Add both members to the Includes box. | |
| Sync Type: Select either Manual with Incremental Sync or Manual with Full Sync. | |
| Initial Sync | Perform an initial sync and ensure that the BIG-IP devices are in Active/Standby mode. Also ensure that the SSL Orchestrator RPM package is installed on both devices. After selecting iApps -> Package Management LX, ensure that the SSL Orchestrator RPM package is installed on both devices and is the same version. |
| HA status | After selecting Device Management -> Overview Status, ensure that there are no warnings or errors. |
Upon full system HA configuration and initial sync, navigate to SSL Orchestrator -> Configuration. In the top right corner, click on the HA Status link. This utility provides status of the SSL Orchestrator sync engine, including REST communications. If any of these indicators are red, do not proceed with the SSL Orchestrator configuration. Move to the Troubleshooting section below.
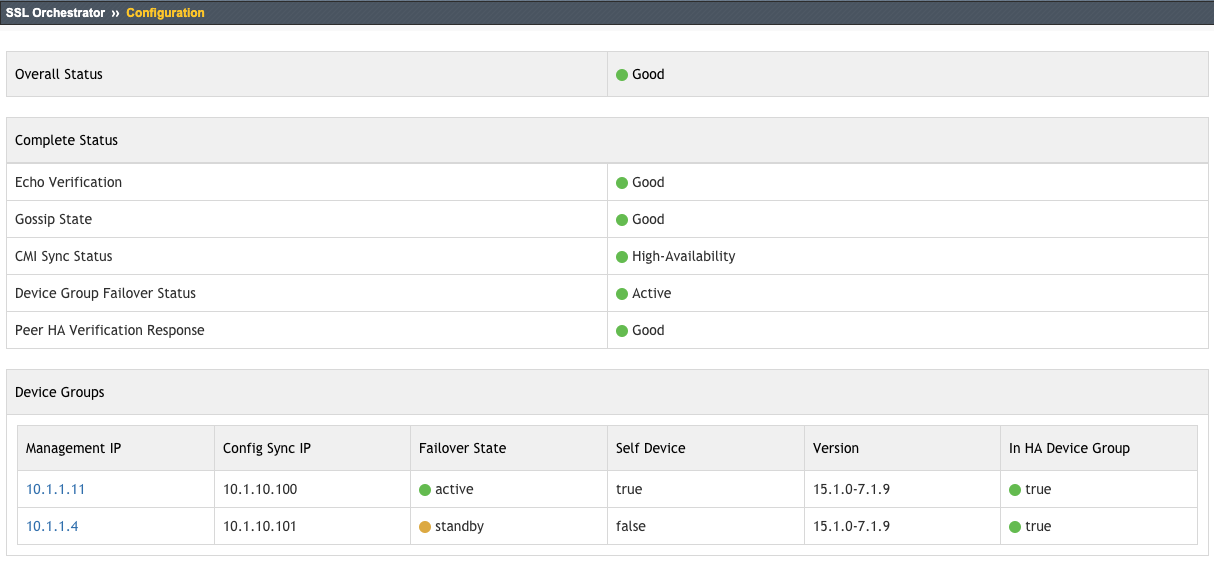
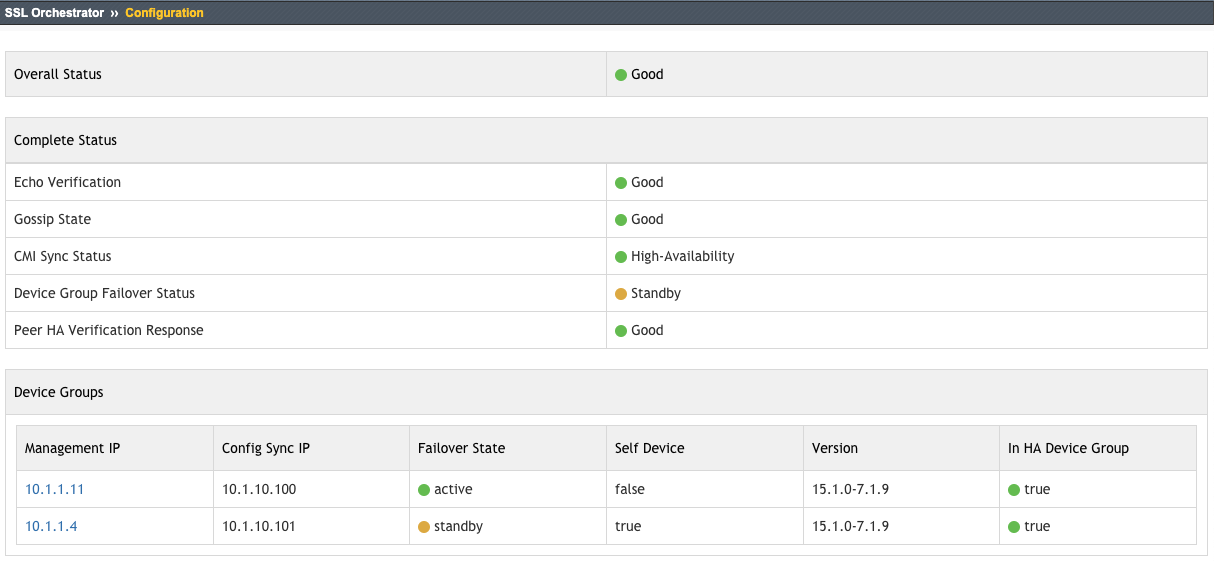
Figure 57/58: SSL Orchestrator HA Status
If all indications are good (green), you may proceed to build SSL Orchestrator configurations. The peers will sync their configurations through the REST communications between them.
Note that this may, at times, present a warning in the BIG-IP UI that indicates the devices are out of sync even though they are not. Review both devices to verify similar settings. It is also acceptable to perform a manual sync after an SSL Orchestrator configuration, but it is not strictly necessary.
In the event that some of the above indicators are bad (red), or an SSL Orchestrator configuration fails because of HA issues, navigate to the Troubleshooting section of this guide.