Solution1 Policy¶
Policy Walk-Through¶
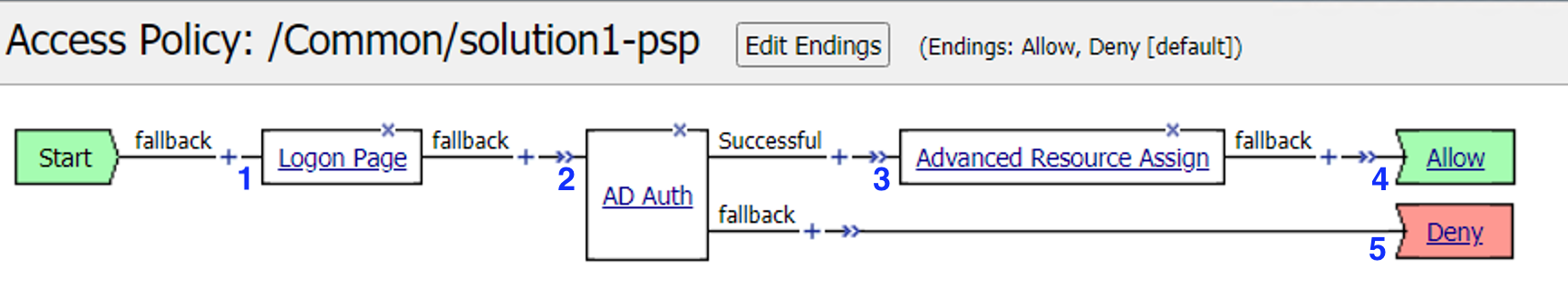
A user enters their credentials into the logon page agent. - Those credentials are collected, stored as the default system session variables of session.logon.last.username and session.logon.last.password.
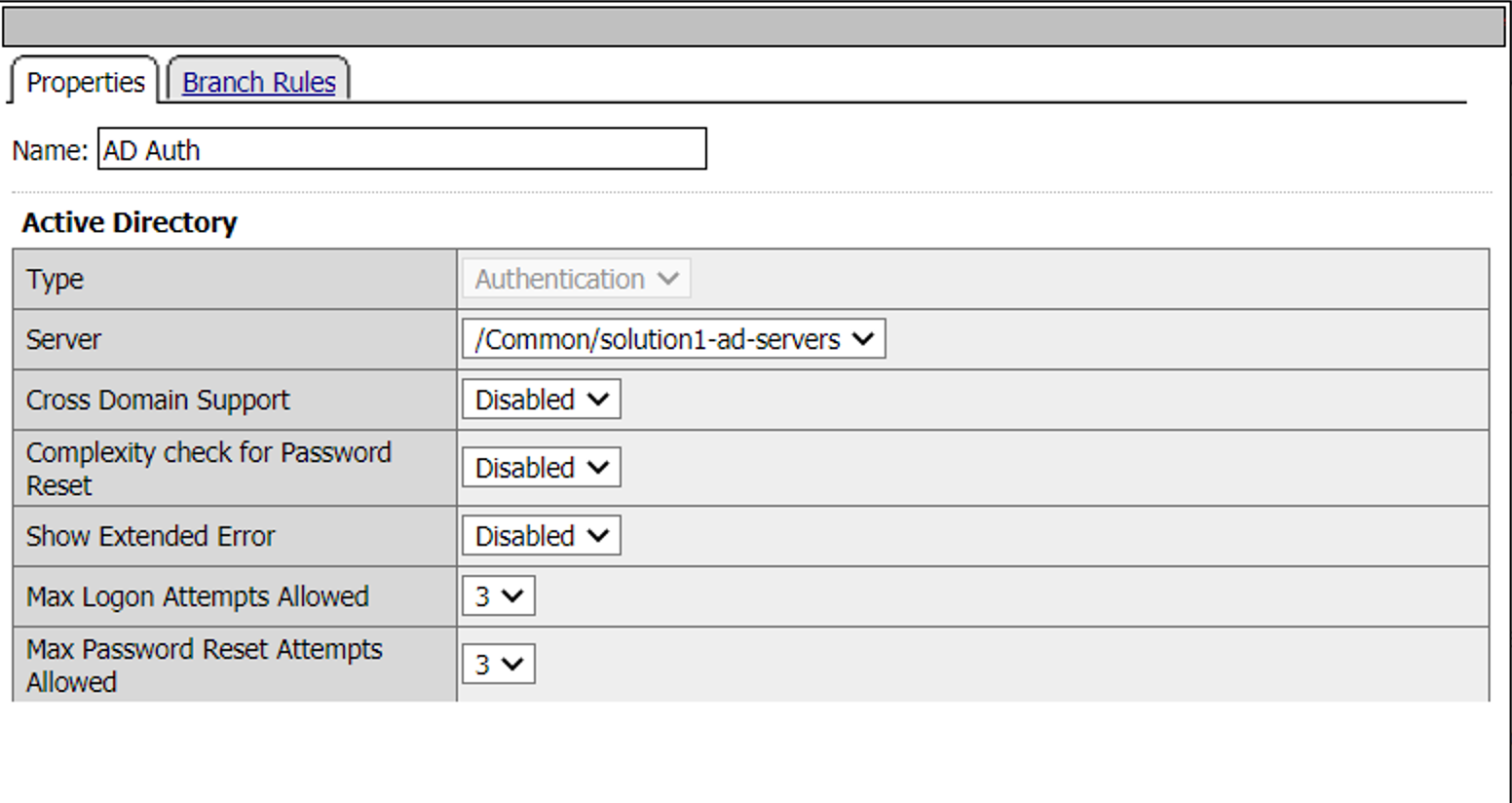
The AD Auth Agent validates the username and password session variables against the configured AD Domain Controller.
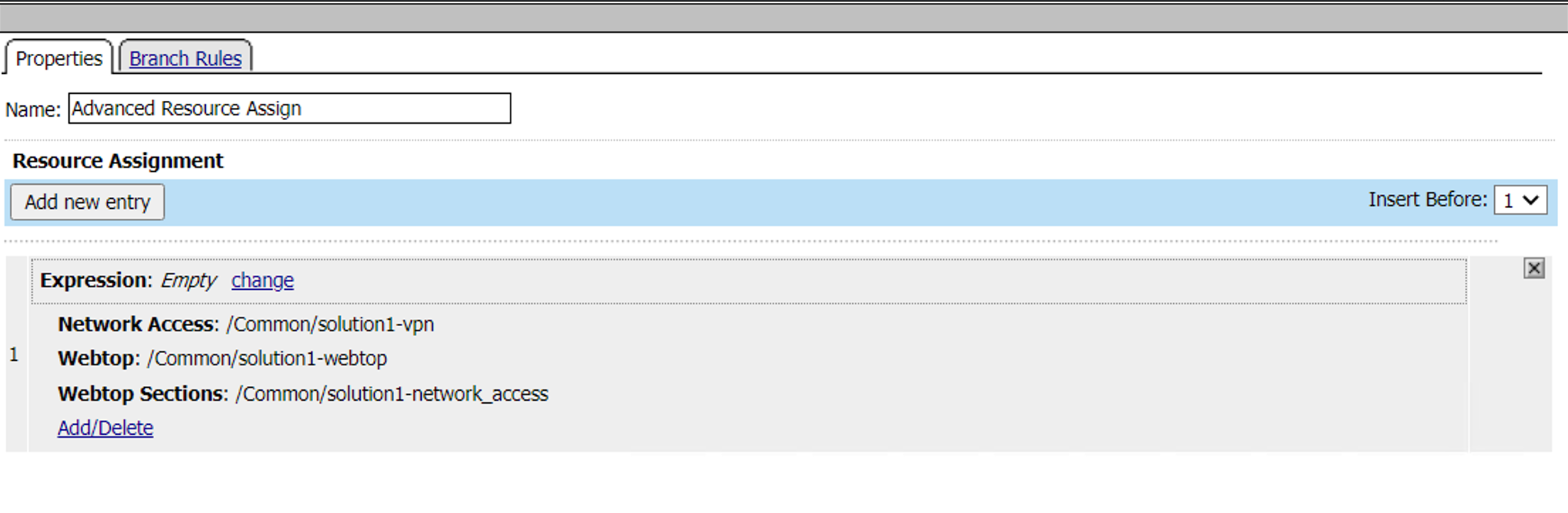
The user is assigned resources defined in the Advanced Resource Assign Agent
The user is granted access via the Allow Terminal
If unsuccessful, the user proceeds down the fallback branch and denied access via the Deny Terminal
Policy Agent Configuration¶
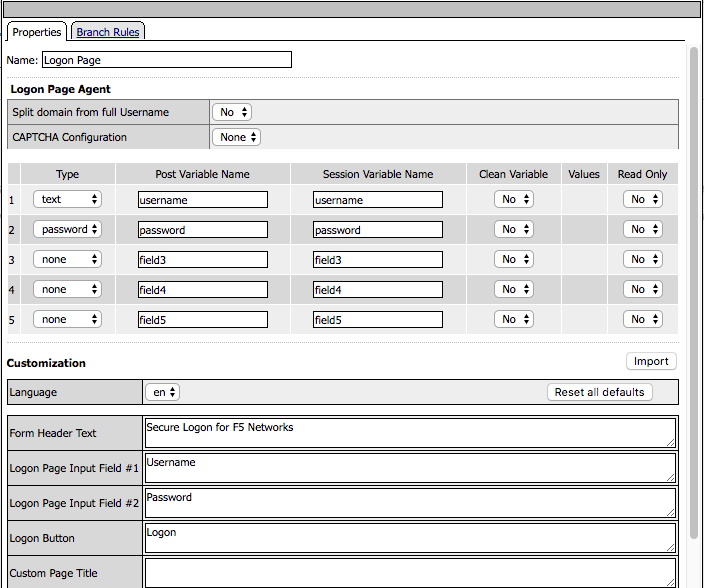
The Logon Page contains only the default setting
The AD Auth agent defines the AAA AD Servers that a user will be authenticated against. All Setting are the default.
The Advanced Resource Assign agent grants a user access to the assigned resources.
Supporting APM Objects¶
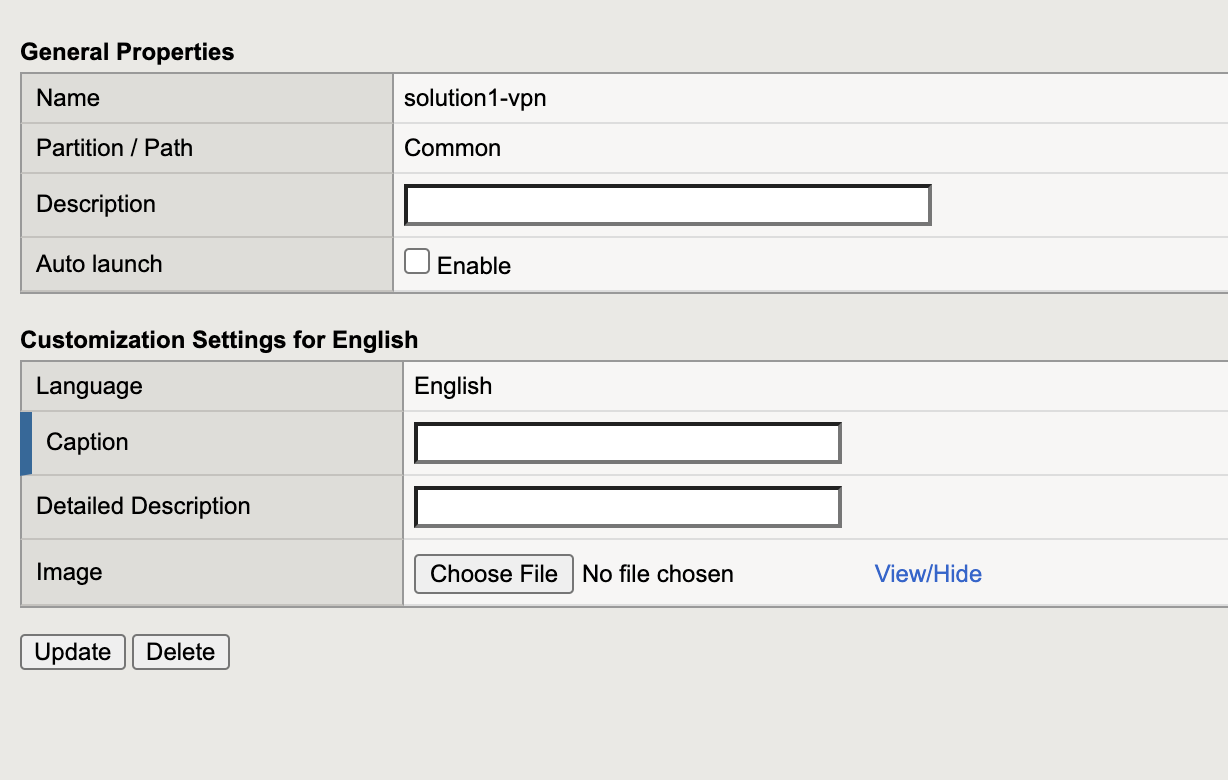
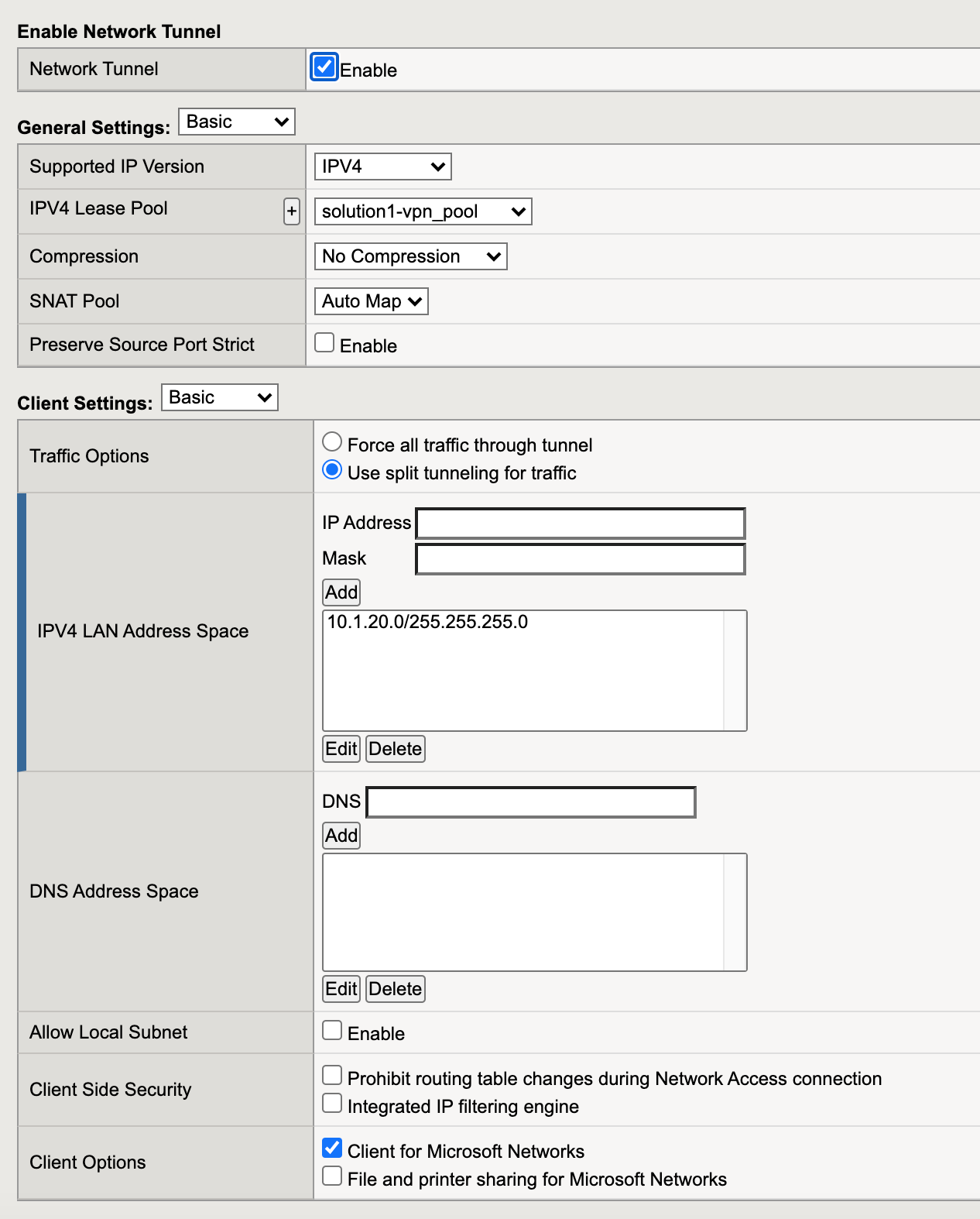
Network Access Resource¶
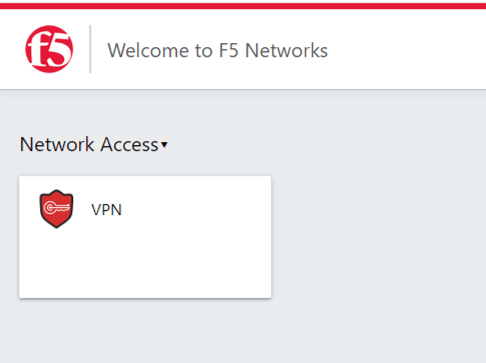
The Properties page contains the Caption name VPN. This is the name displayed to a user.
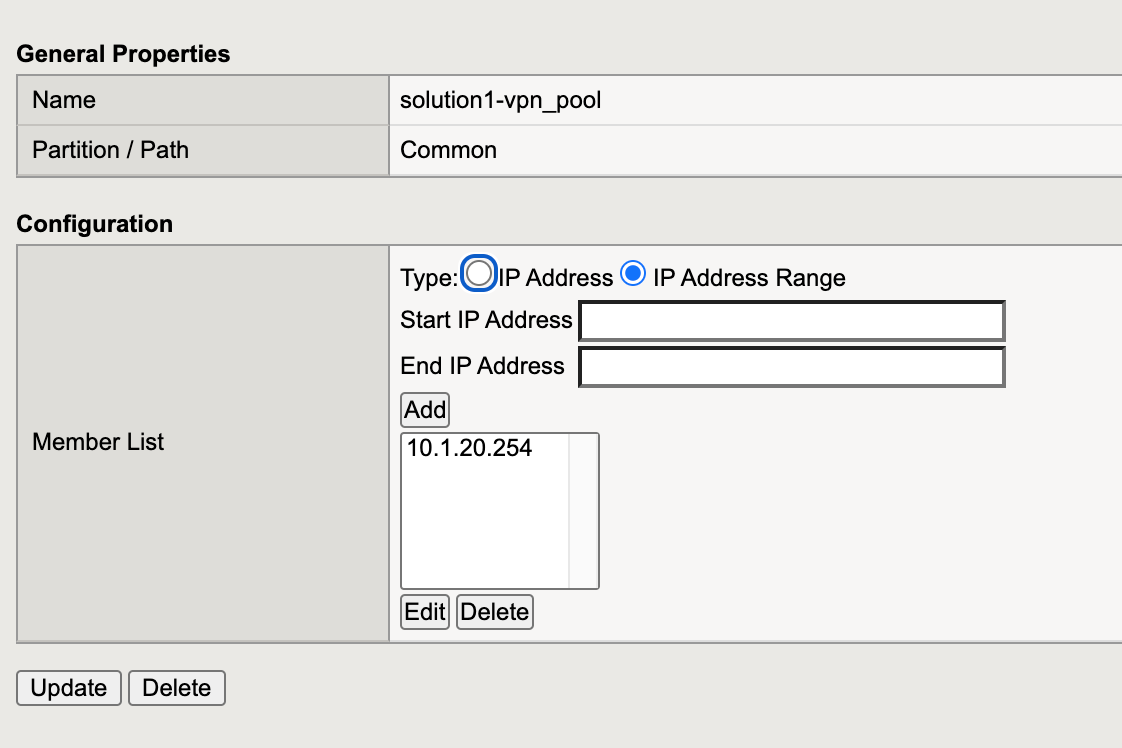
The Network Settings tab assigns the lease pool of ip addresses that will be used for the VPN.
Split Tunneling is configured to permit only the 10.1.20.0/24 subnet range inside the VPN.
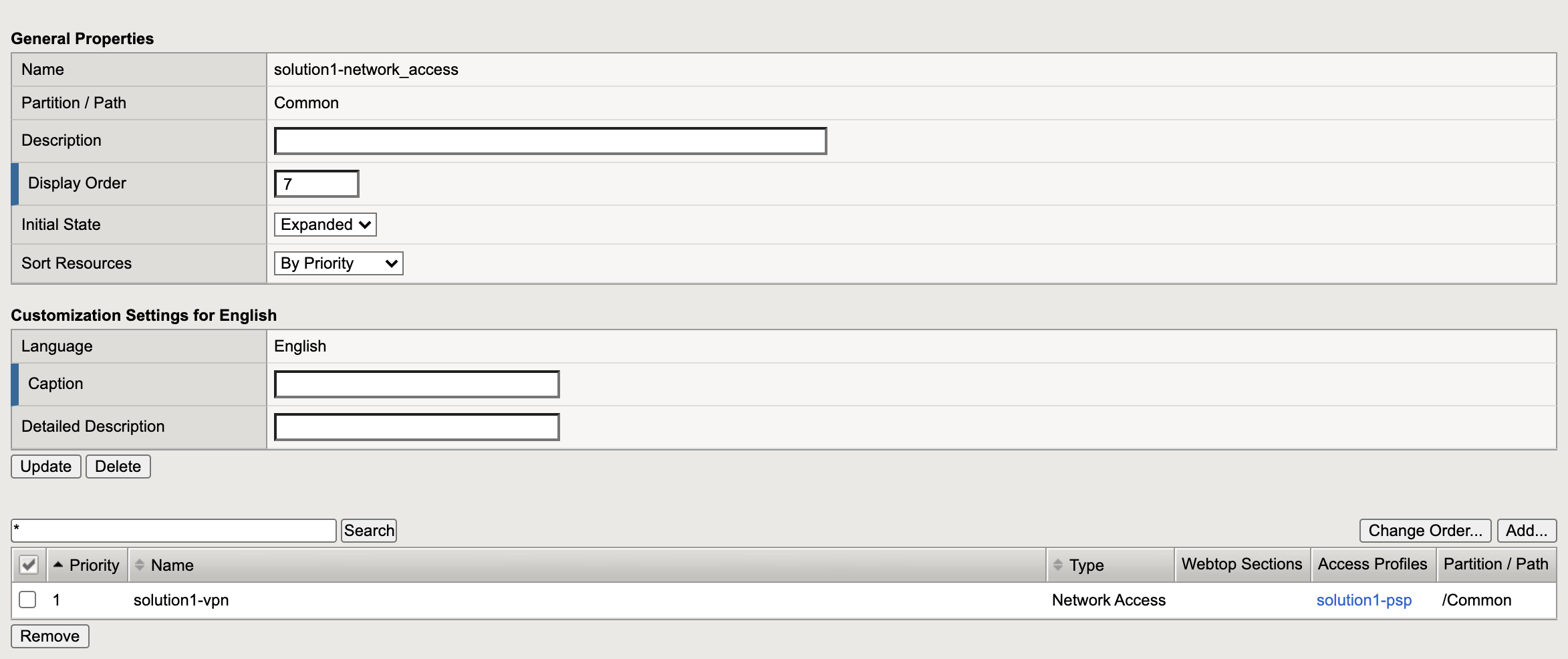
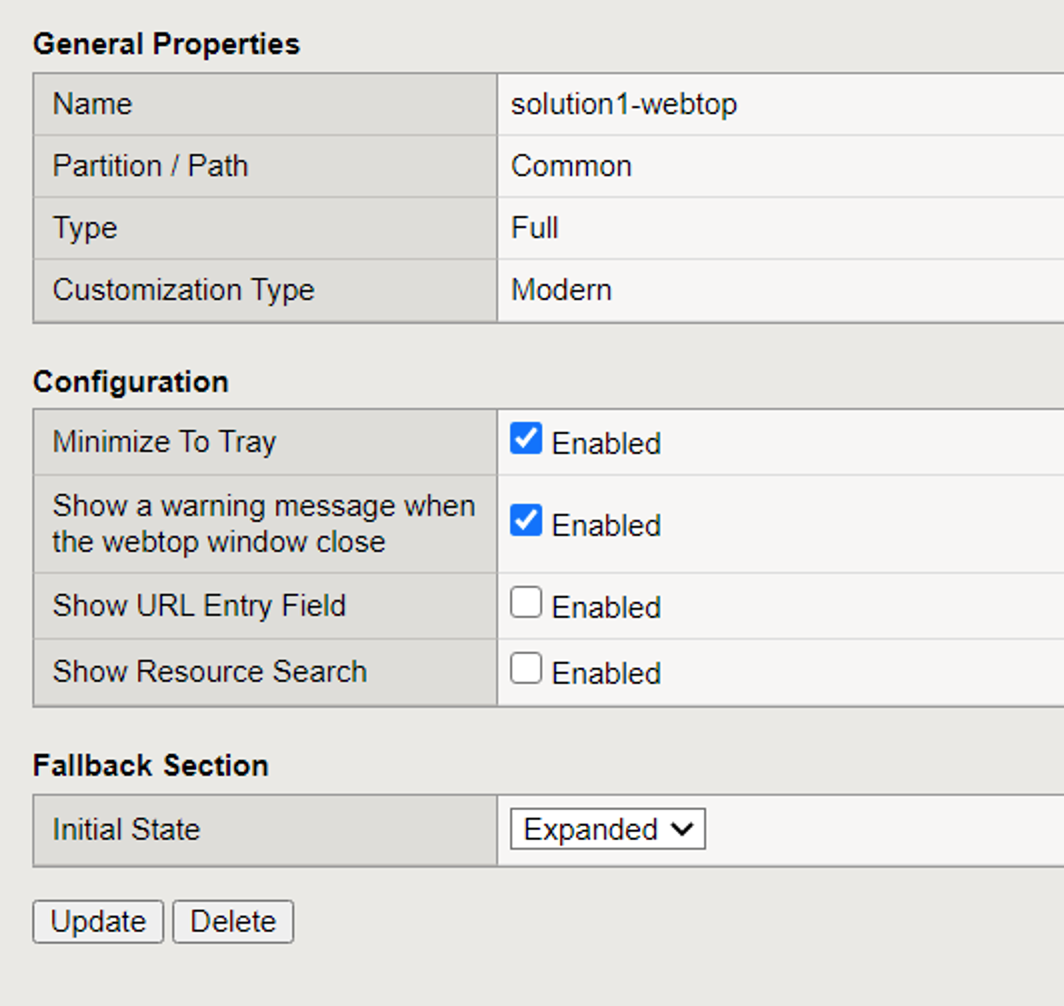
Webtop¶
A Full Webtop was defined with modified default settings.
The Minimize to Tray box is checked to ensure the Webtop is not displayed when a user connects to the VPN.
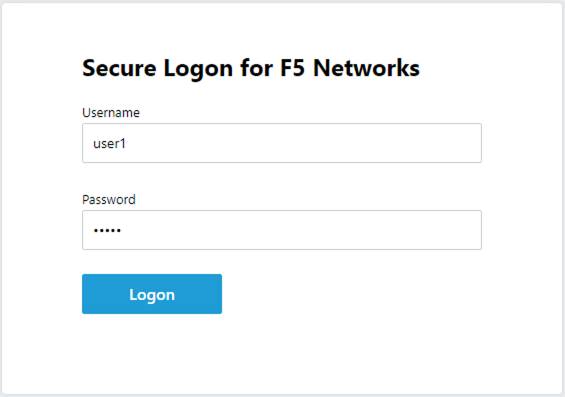
The Policy from a user’s perspective¶
The connects to https://solution1.acme.com with the following credentials
Username: user1
Password: user1
Once authenticated the user is presented a Webtop with a single VPN icon.
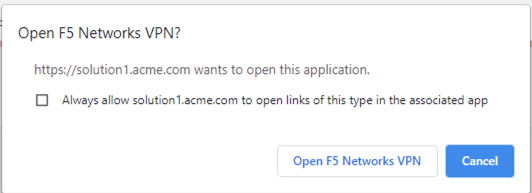
Assuming the VPN has already been installed the user is notified that the client is attempting to start
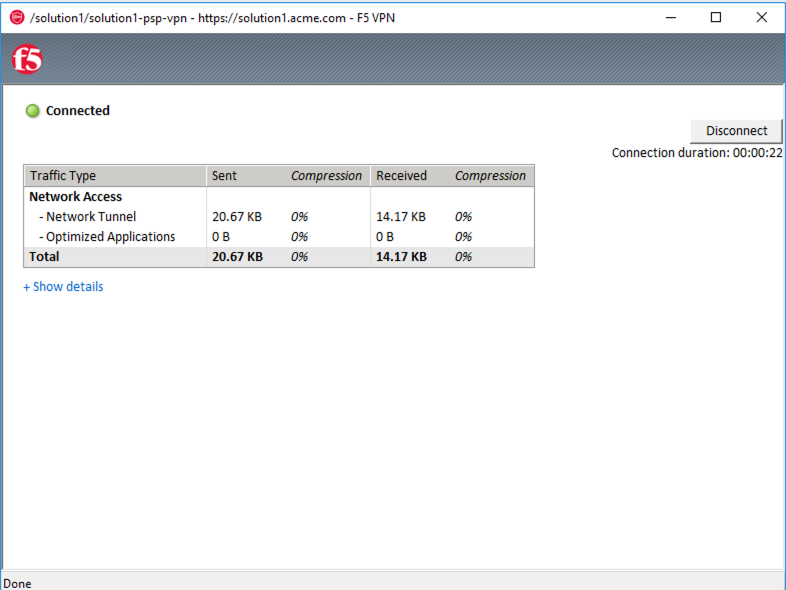
A popup opens displaying the status of the VPN connection. The status will eventually become Connected