Solution9 Policy¶
Policy Walk-Through¶
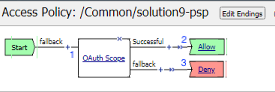
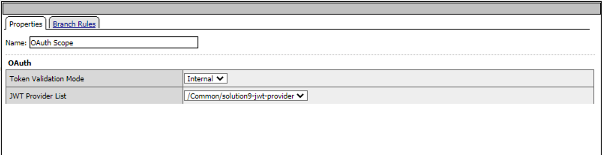
When a user accesses a VIP protected by this policy JWT and scope validation is performed
Upon successful Authorization, the user is granted access via the Allow Terminal
If unsuccessful, the user proceeds down the fallback branch and denied access via the Deny Terminal
Profile Settings¶
All profile settings are left the defaults
Supporting APM Objects¶
Provider¶
The settings below define all the components of the Authorization Server’s endpoints to retrieve and validate tokens.
The Policy from a user’s perspective¶
This solution is designed to be integrated with Authorization Server based solutions. Please ensure you deply the Authoriztion Server prior to deploying this solution.
Open Postman on the Jumphost
Click Import
Click Upload Files
Navigate to C:\access-solutions\solution9\student_files, select solution9 request.json, and click Open
Click Import
Expand the collection.
Select 1. Retreive OAuth Client Settings
Click Send
You will receive a response body containing the ClientId and ClientSecret. This request saved those values as a Postman Variables.
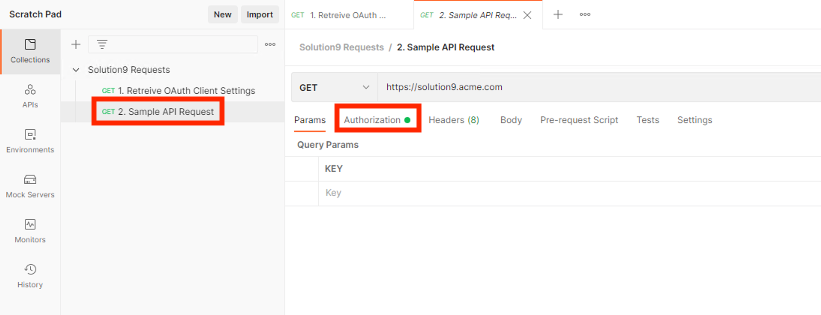
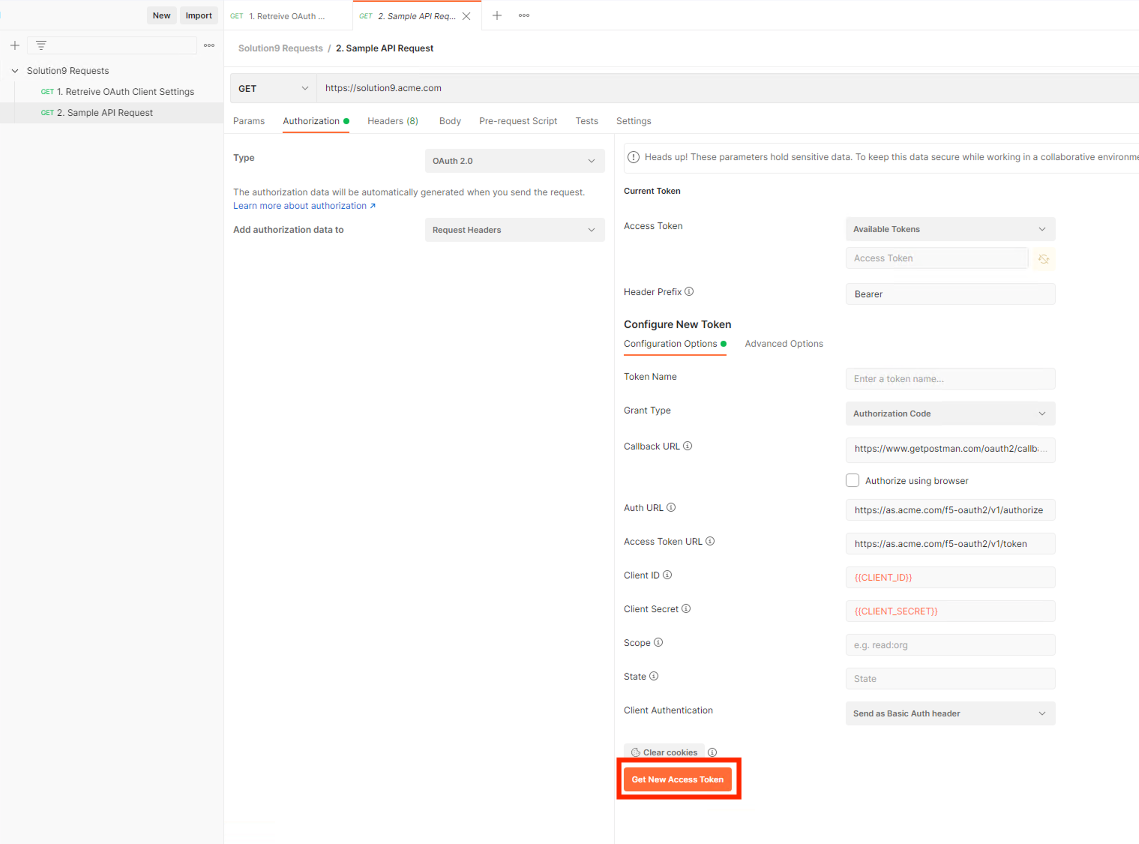
Select 2. Sample API Request
Click the Authorization tab.
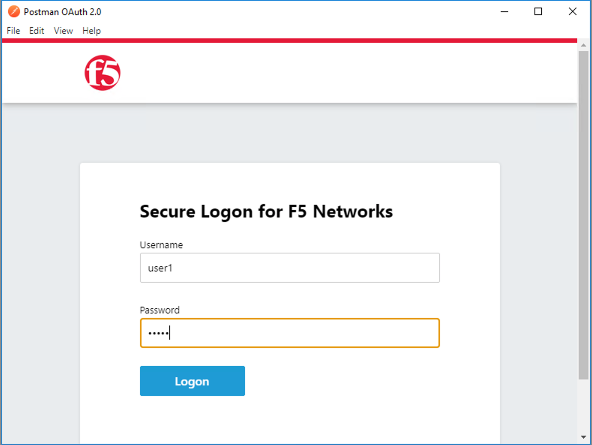
Click Get New Access Token
Login using Username: user1 and Password: user1
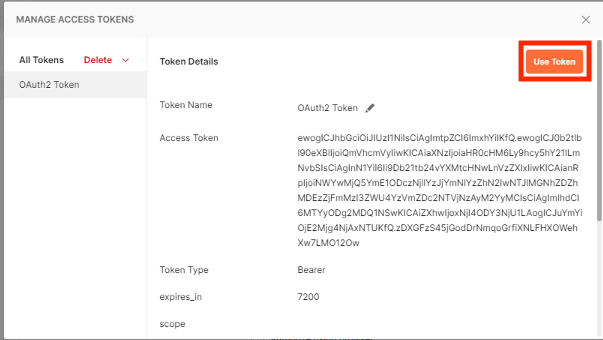
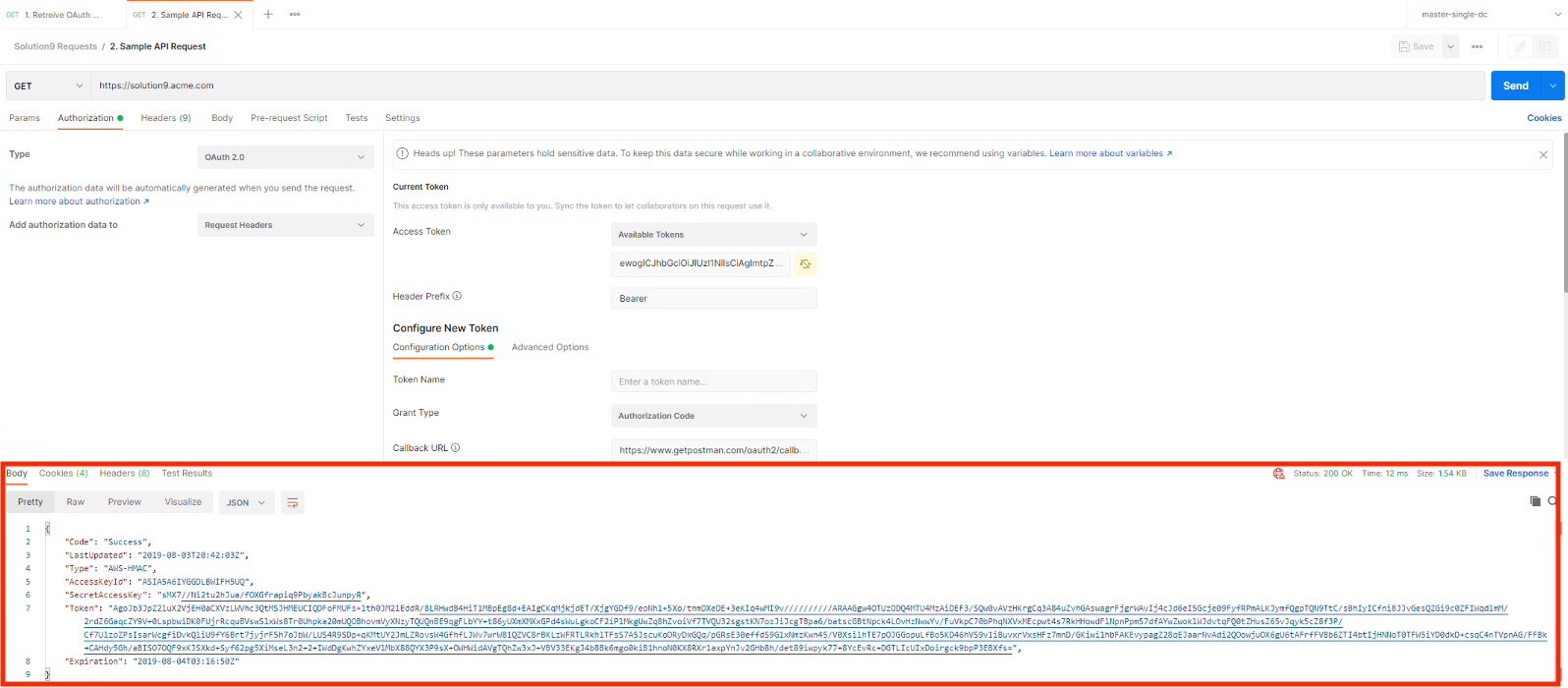
Click Use Token
Click Send
The user receives a 200 OK with a response. The Access Token was successfully validated by the BIG-IP to permit access.