F5 BIG-IQ Centralized Management Lab > BIG-IQ All Labs > Class 7: BIG-IQ Application Firewall Manager > Module 1: Network Security Firewall Objects Source | Edit on
Lab 1.3: Report on orphaned, unused, network security (new 8.0)¶
Note
Estimated time to complete: 15 minutes
In this lab, we will generate a report of network security objects that are currently not being used by any AFM policies or rules.
Prerequisites¶
Make sure your devices have AFM module discovered and imported for BOS-vBIGIP01.termmarc.com, BOS-vBIGIP02.termmarc.com and SEA-vBIGIP01.termmarc.com under Devices > BIG-IP DEVICES.
Tasks¶
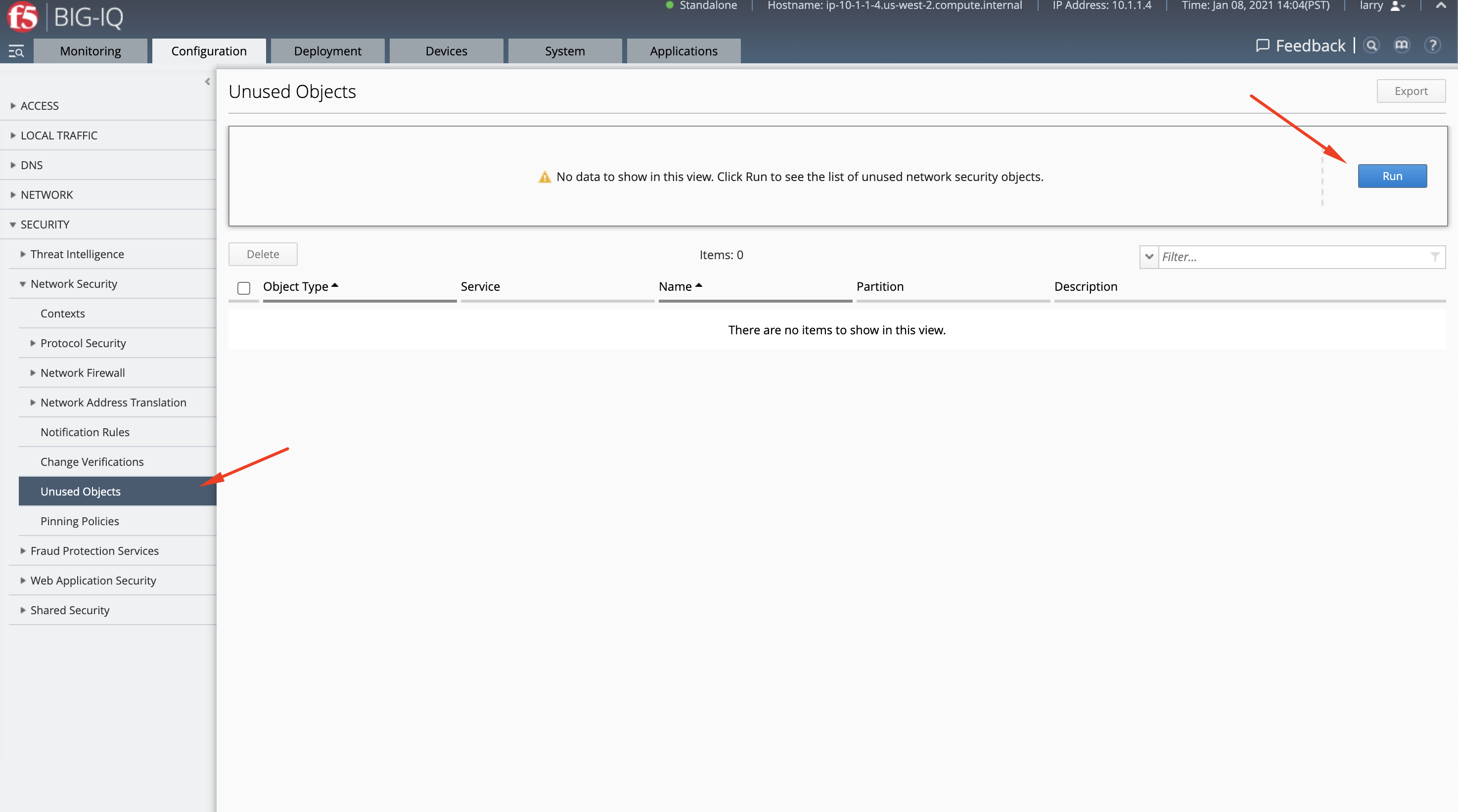
- Login to BIG-IQ as larry .
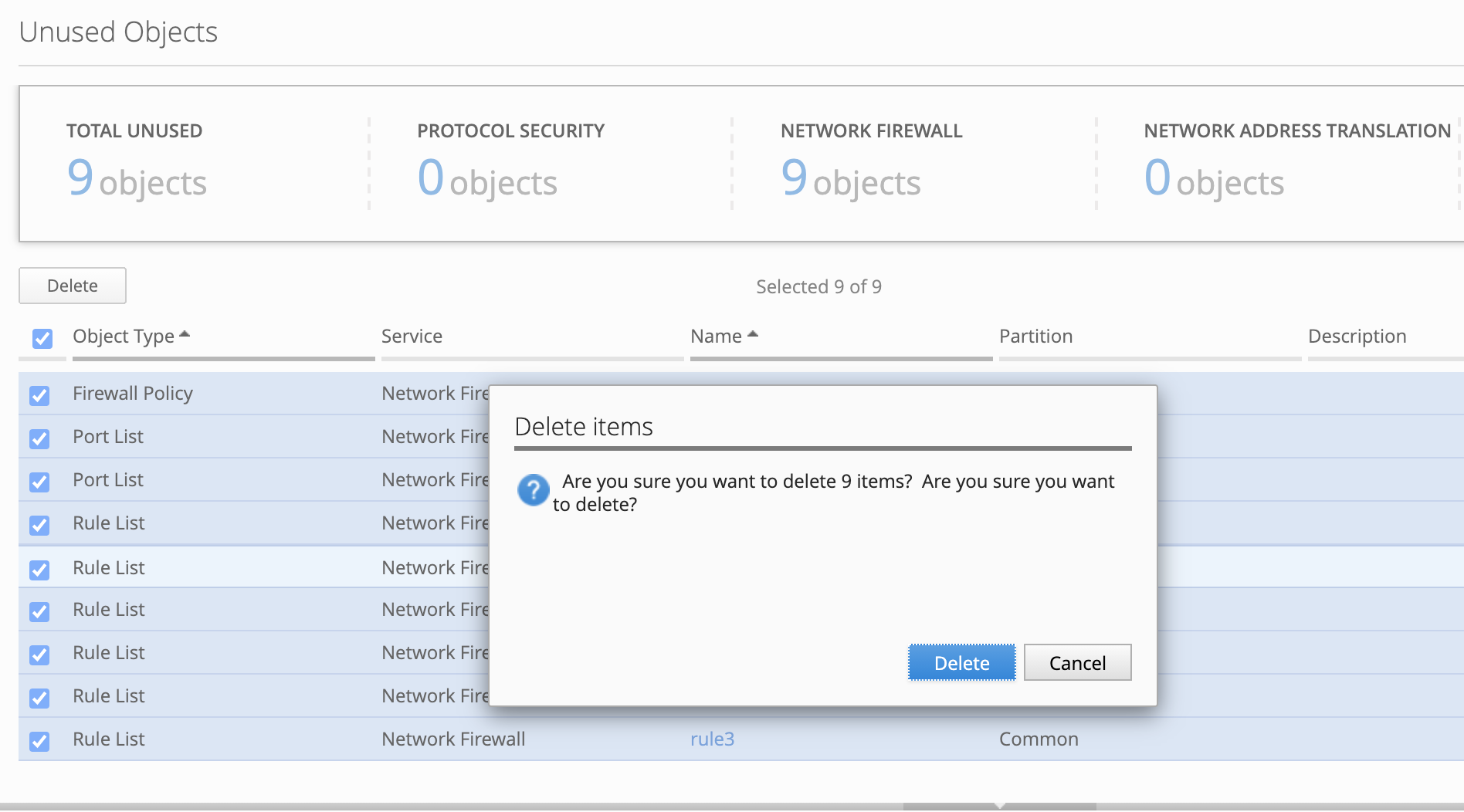
- Go to Configuration > Security > Network Security > Unused Objects, then click on Run to generate the report.
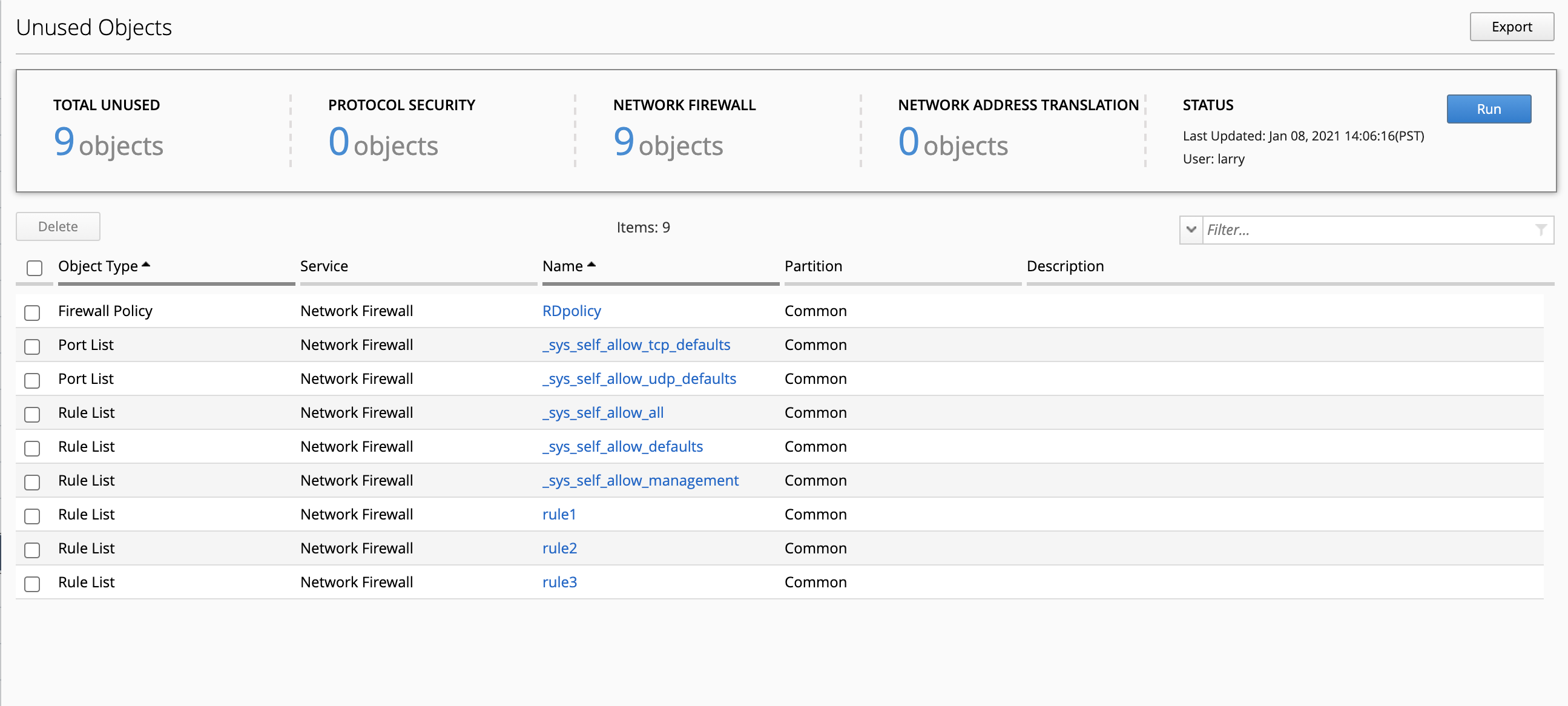
- A report is created showing a list of unused Network Security objects.
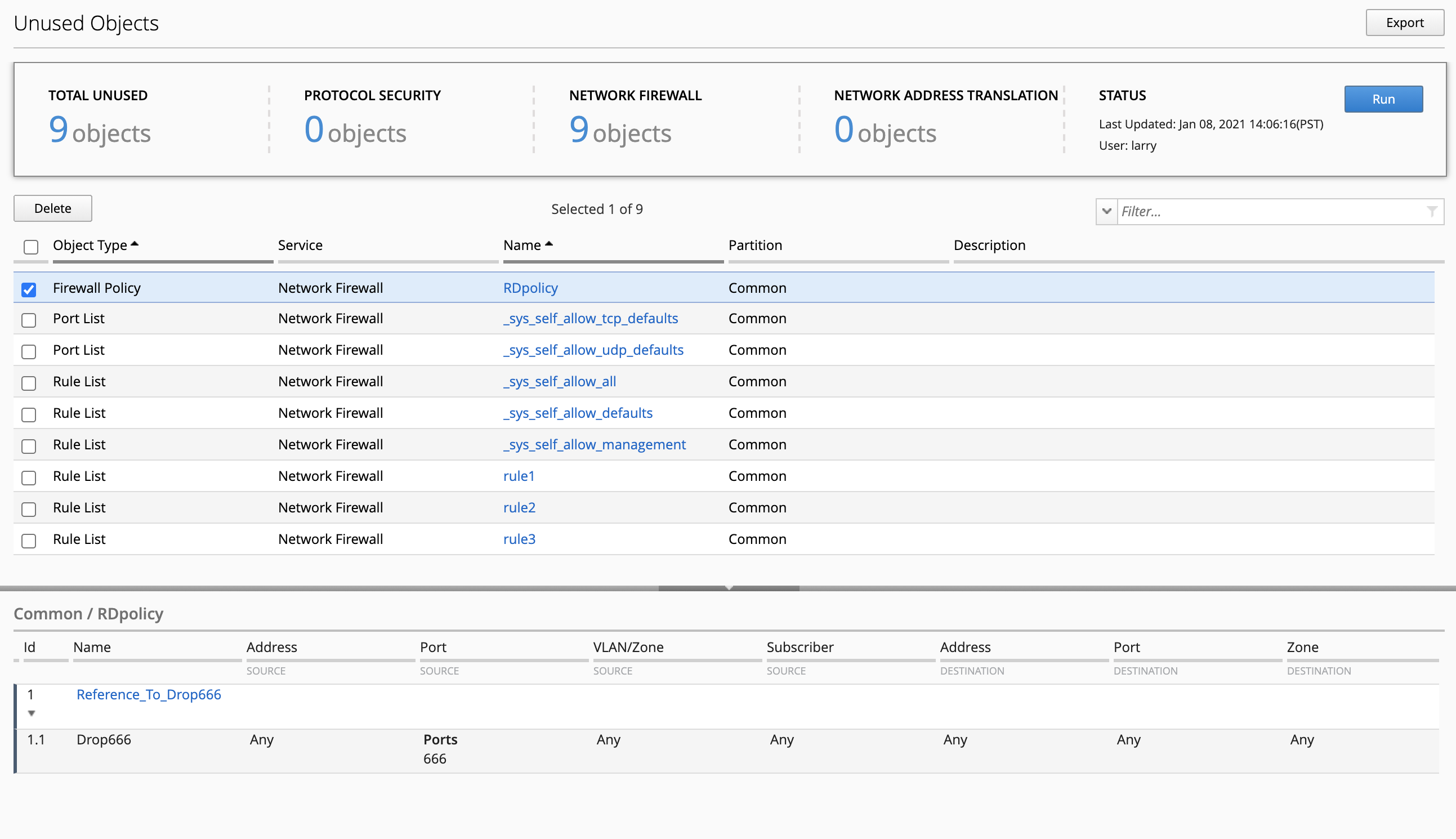
- By selecting an object, you can see its details.
- Now, let’s start to do some cleanup. Select all the objects and click on Delete. This action will not delete objects from the BIG-IPs but only from the BIG-IQ.
..warning:: Address lists might be referenced in other services such as LTM or Shared Security.
- Next, we will create an evaluation and deploy the changes we just made.
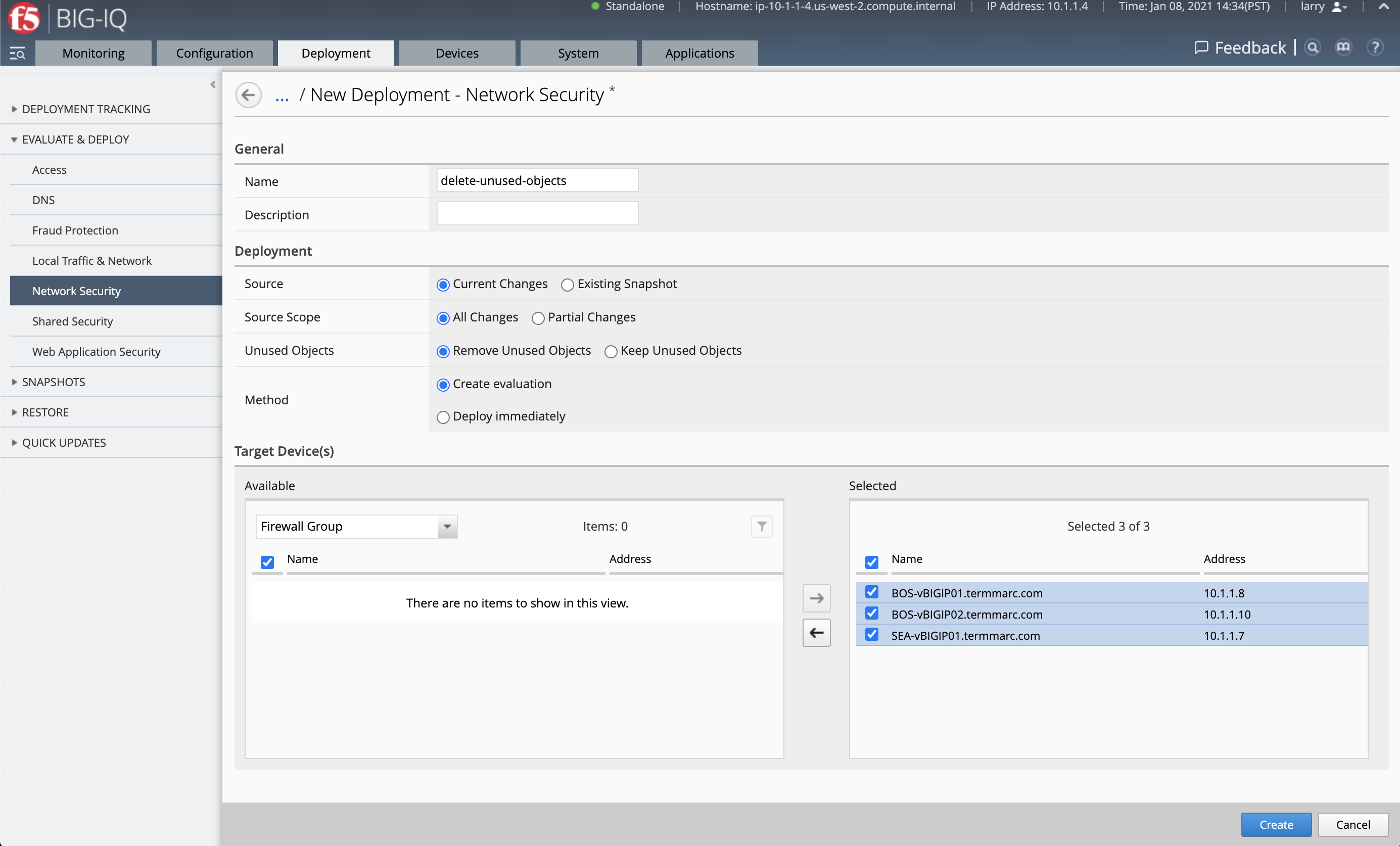
- Click on top Deployment tab, select under EVALUATE & DEPLOY: Network Security and click Create.
Set a name, Under Target Devices, select all the devices, click Create to launch the evaluation.
- Once the evaluation is completed, review the objects to be removed.
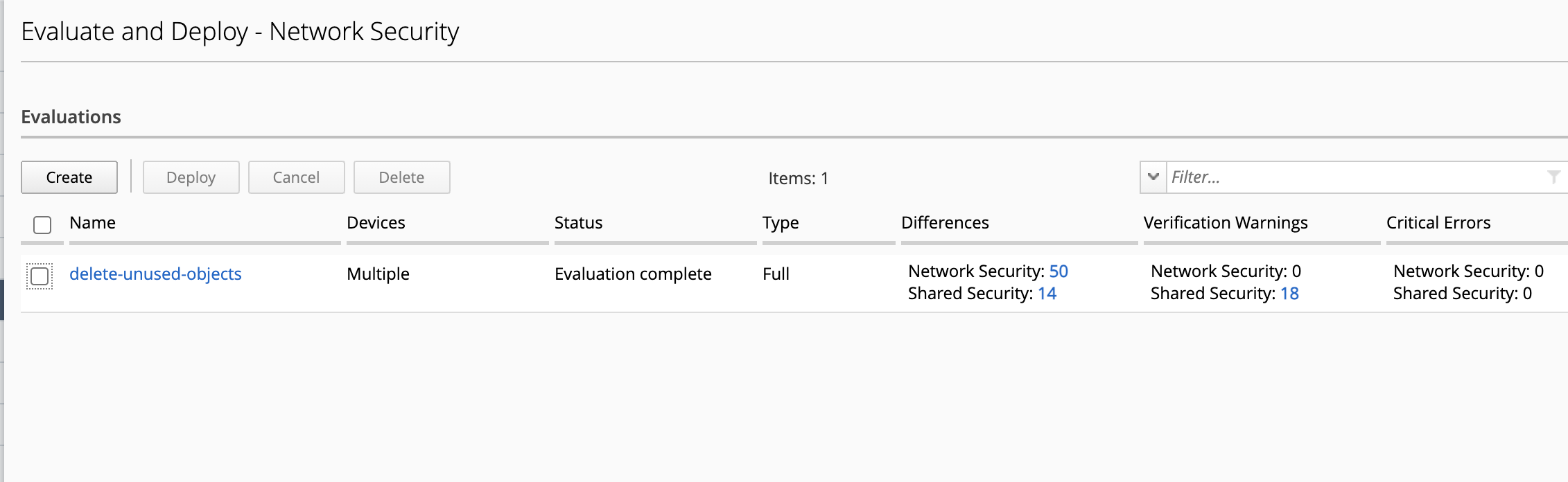
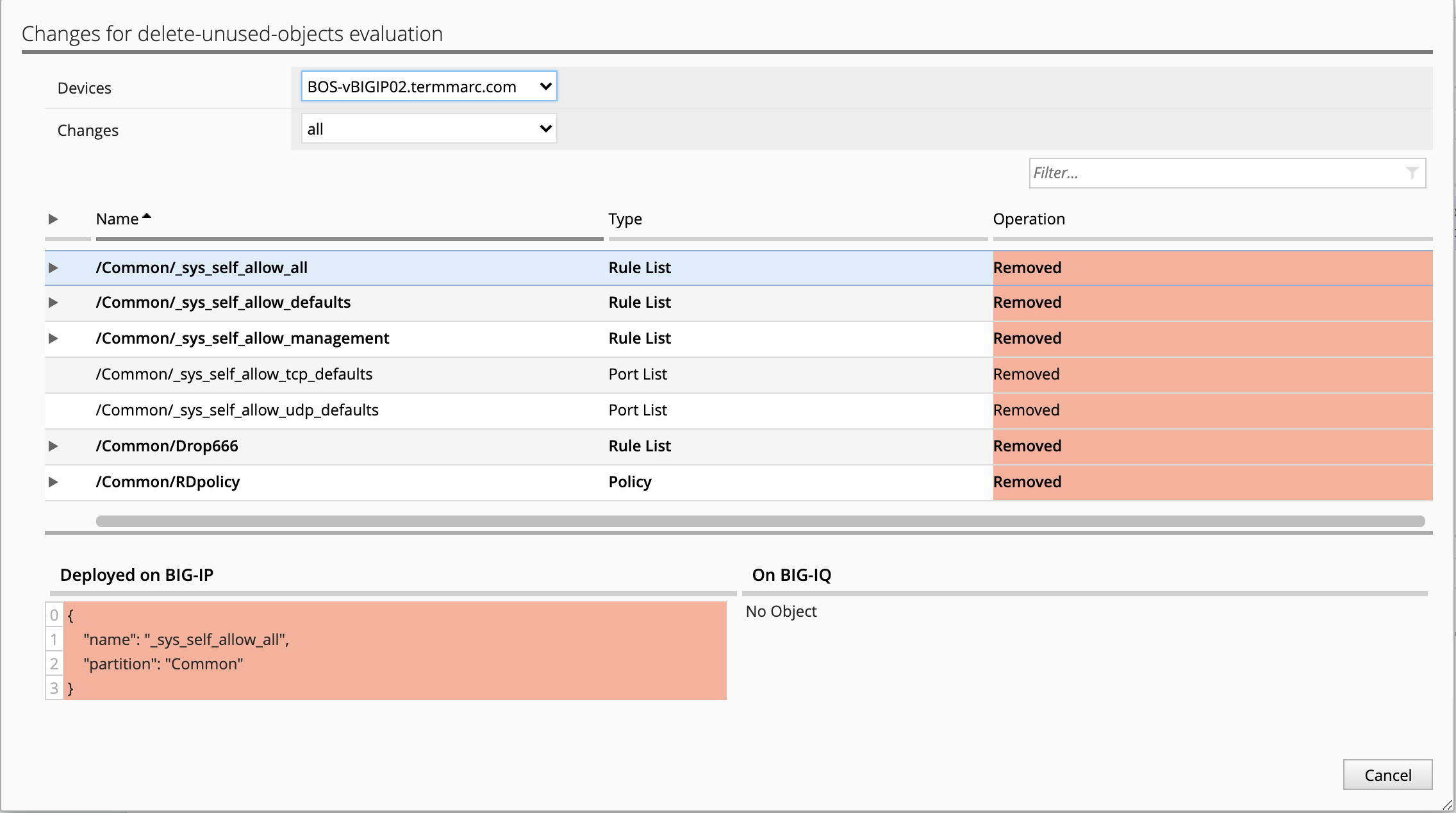
- Then, select the evaluation and click on Deploy.
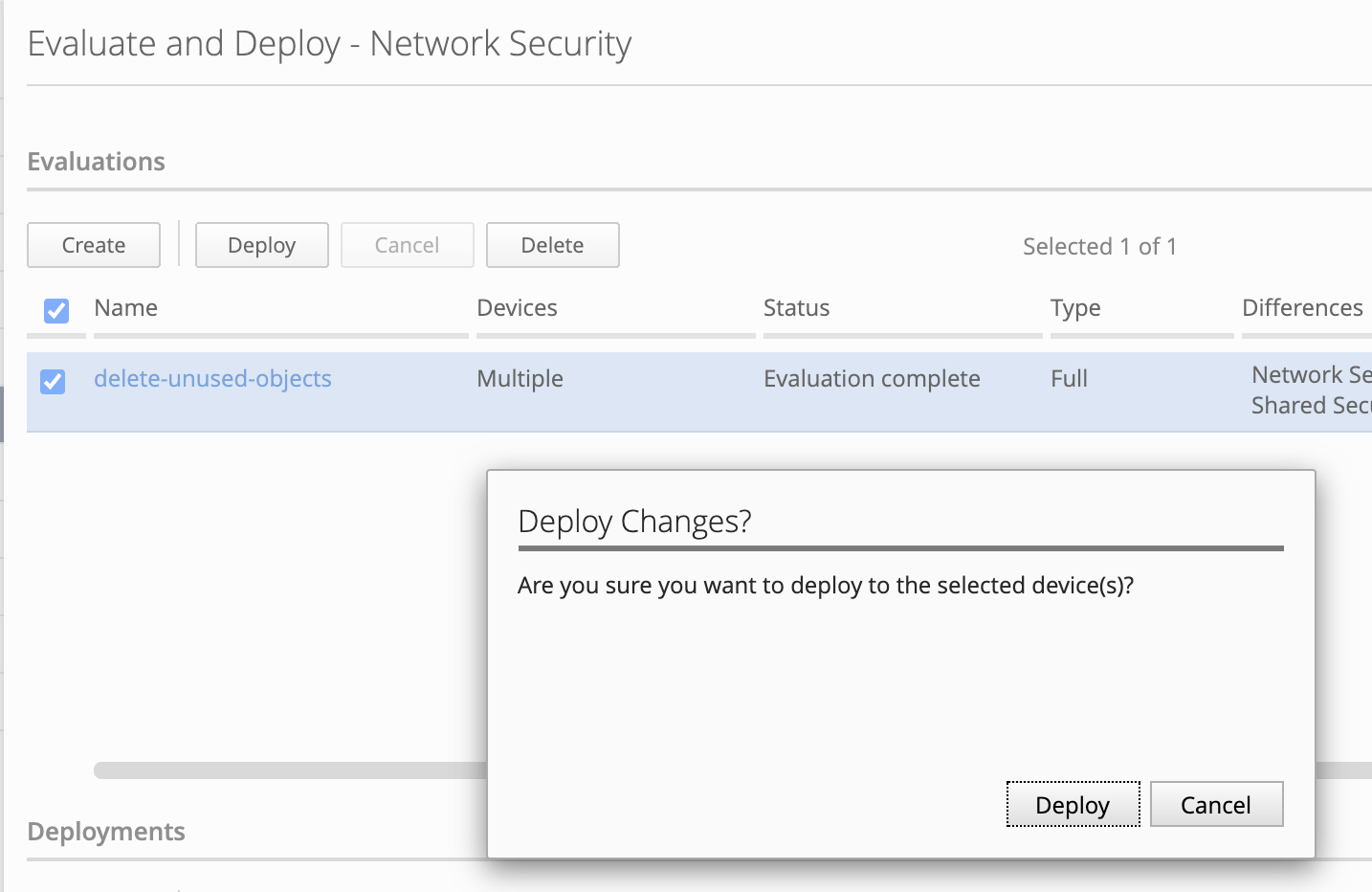
- Verify the deployment is successful.
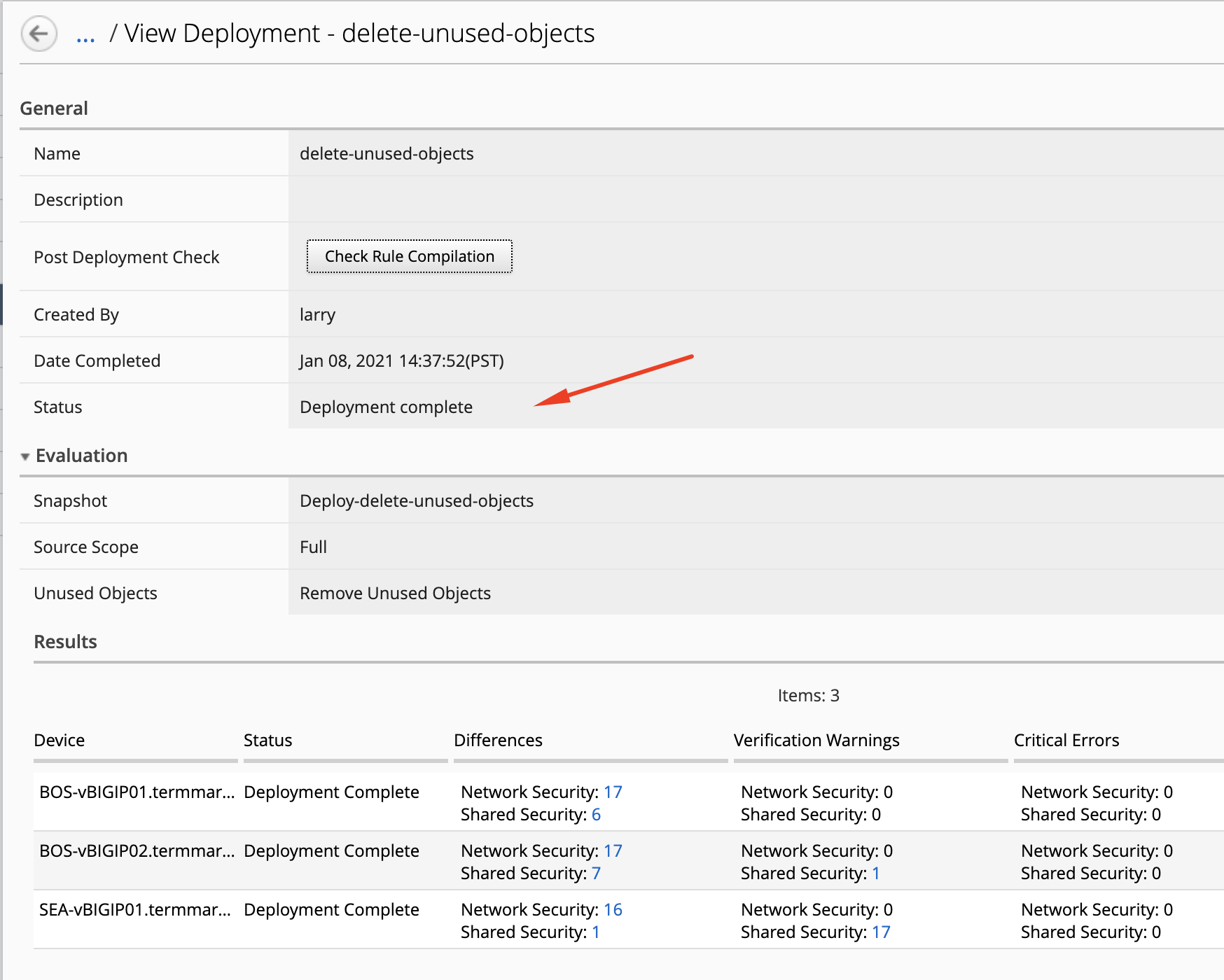
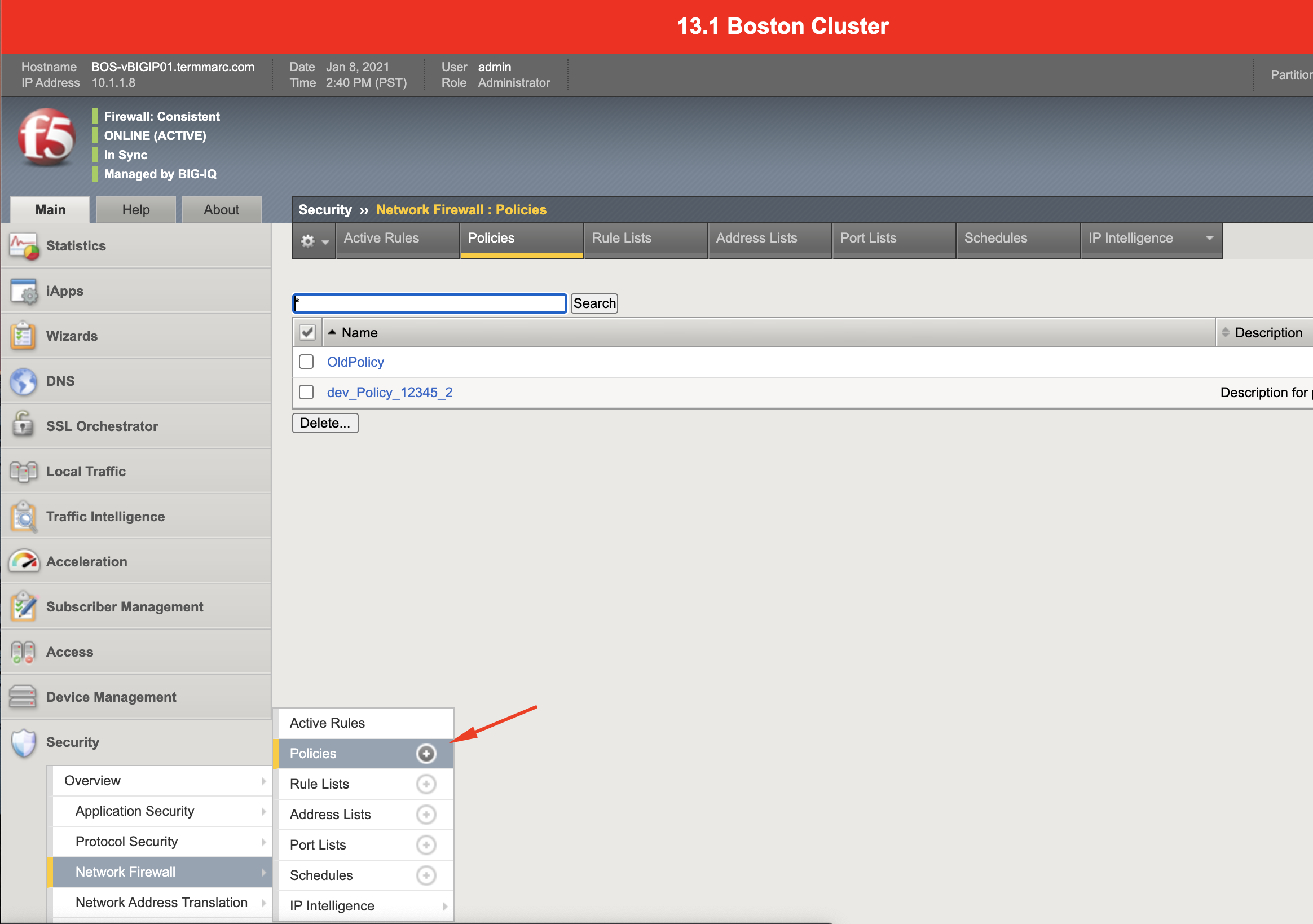
- Now, the cleanup of unused network objects is done. Let’s verify on BIG-IP. From the lab environment, login to the BOS-vBIGIP01.termmarc.com and navigate under Security > Network Firewall > Policies. Confirm the unused objects showing in the report at the beginning of this lab are deleted from the BIG-IP.