NGINX Modern Apps > Class 10 - NMS API Connectivity Manager > Module 7 - Advanced Security Lab Source | Edit on
Step 13 - Oauth2 Introspection¶
JWT is based on OAuth and OIDC. Keycloak is the OAuth Authorization Server. Keycloak is already configured to issue JWT tokens for developers.
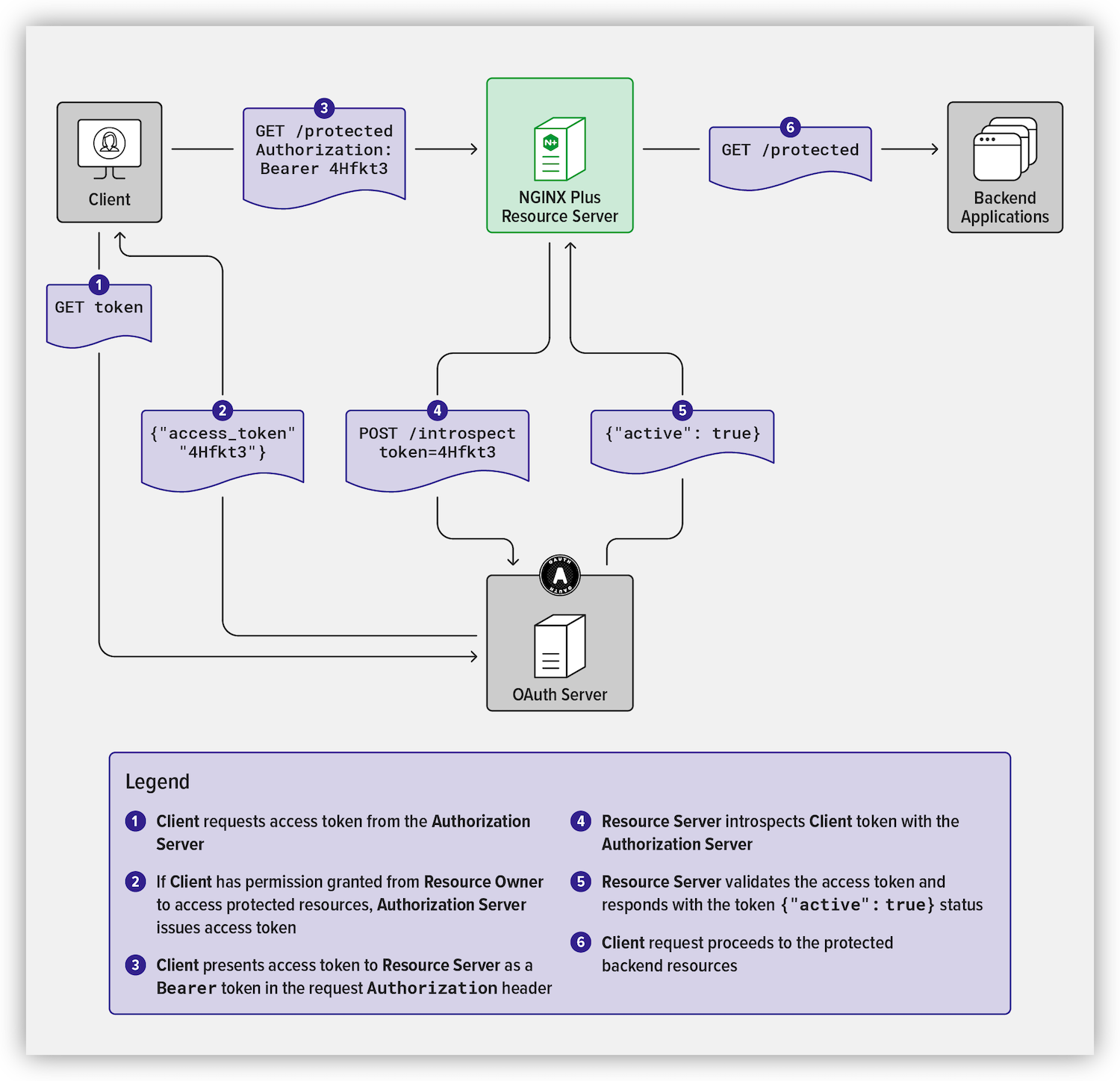
What is Oauth2 Introspection?¶
In the previous lab, we configure a Policy to authenticate API requests with JWT tokens. This policy checked if a JWT token is part of the Authorization header, and the API Gateway checked if Keycloak signs the JWT (we pasted the JWKS keys into the JWT Policy). But in this use case, the API GW does not check against Keycloak if the JWT token is valid. Instead, only the signature and the timestamp are checked.
OAuthv2 Introspect adds a capability for the API GW to check against the Oauth AS (Keycloak) if the JWT is valid (https://docs.nginx.com/nginx-management-suite/acm/how-to/policies/introspection/)
Add Oauth2 Introspection on API-Proxy¶
- Edit
API-Proxyv2like previously (we are going to replace JWT Auth with Oauth2 Introspection) - In
Policies, remove theJSON Web Token Asserionpolicy - Add a new
Oauth2 Introspectionpolicy - In the
Introspection Requestsection, configure as follows- Introspection endpoint: http://10.1.1.4:8080/realms/devportal/protocol/openid-connect/token/introspect
- In
Credentialssection, configure as follows- Client ID: apigw
- Client secret: iOVsaPIfoQ2gk8CSO9H40qPUOXFNvn48
- Click
Add - Click
Save and Publish
Test Oauth2 Introspection out with Postman¶
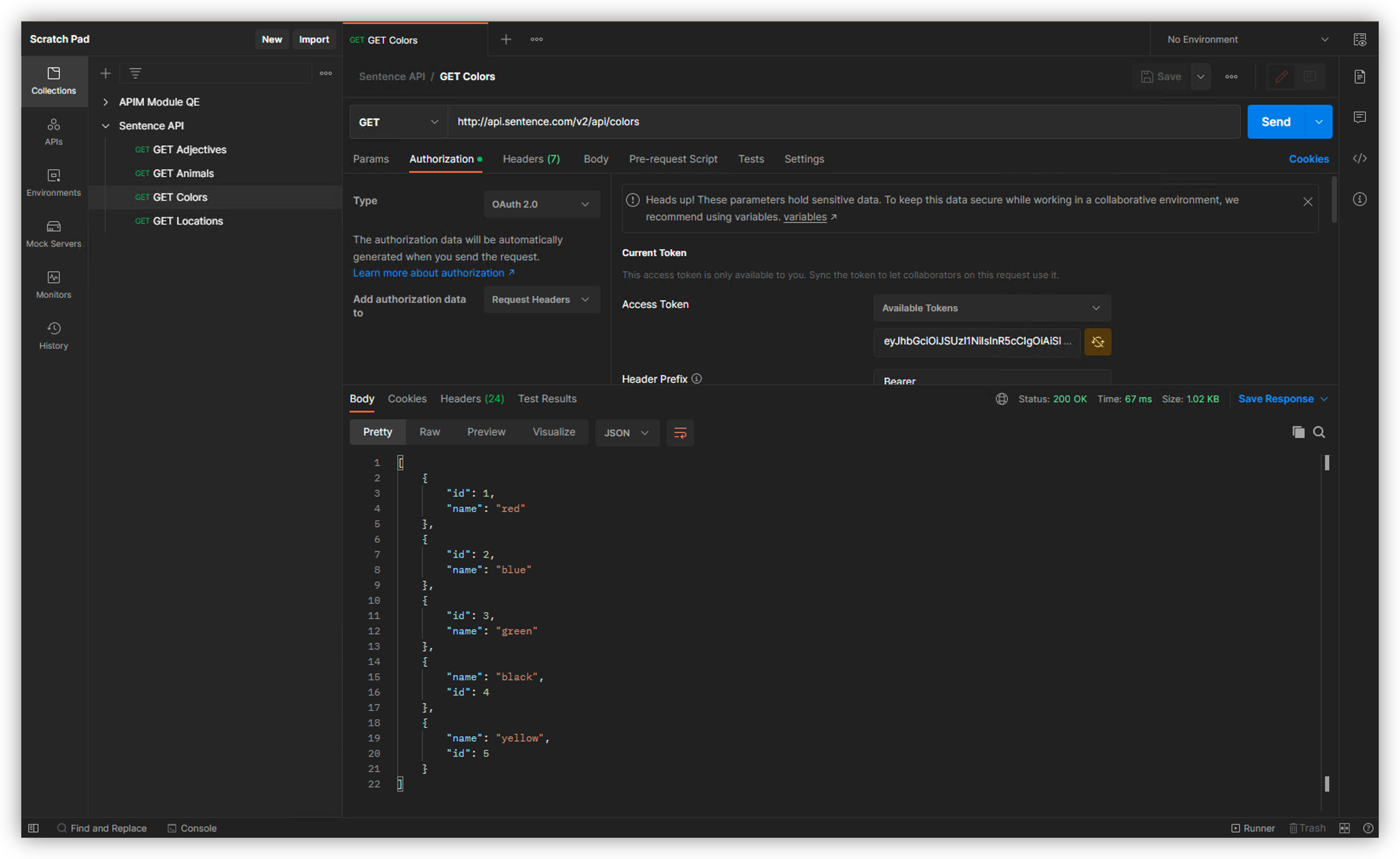
In Postman, select the call
GET Colorsand check the version isv2http://api.sentence.com/v2/api/colorsIn Authorization, select type
OAuth 2.0Note
As you can notice, the Postman OAuth v2.0 client is already set to request JWT against Keycloak
Scroll down and click on
Get New Access Token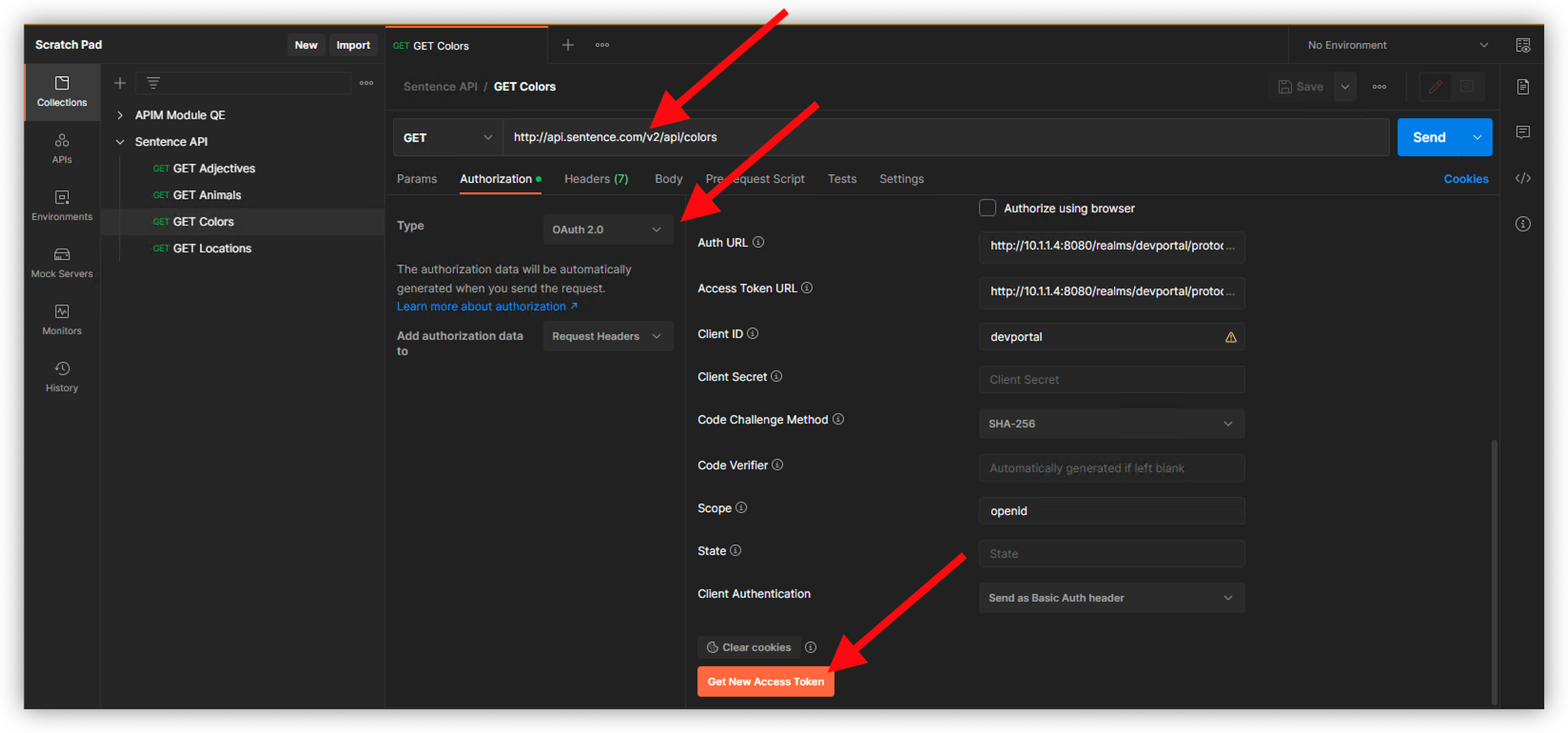
Authenticate as
dev1and passworddev1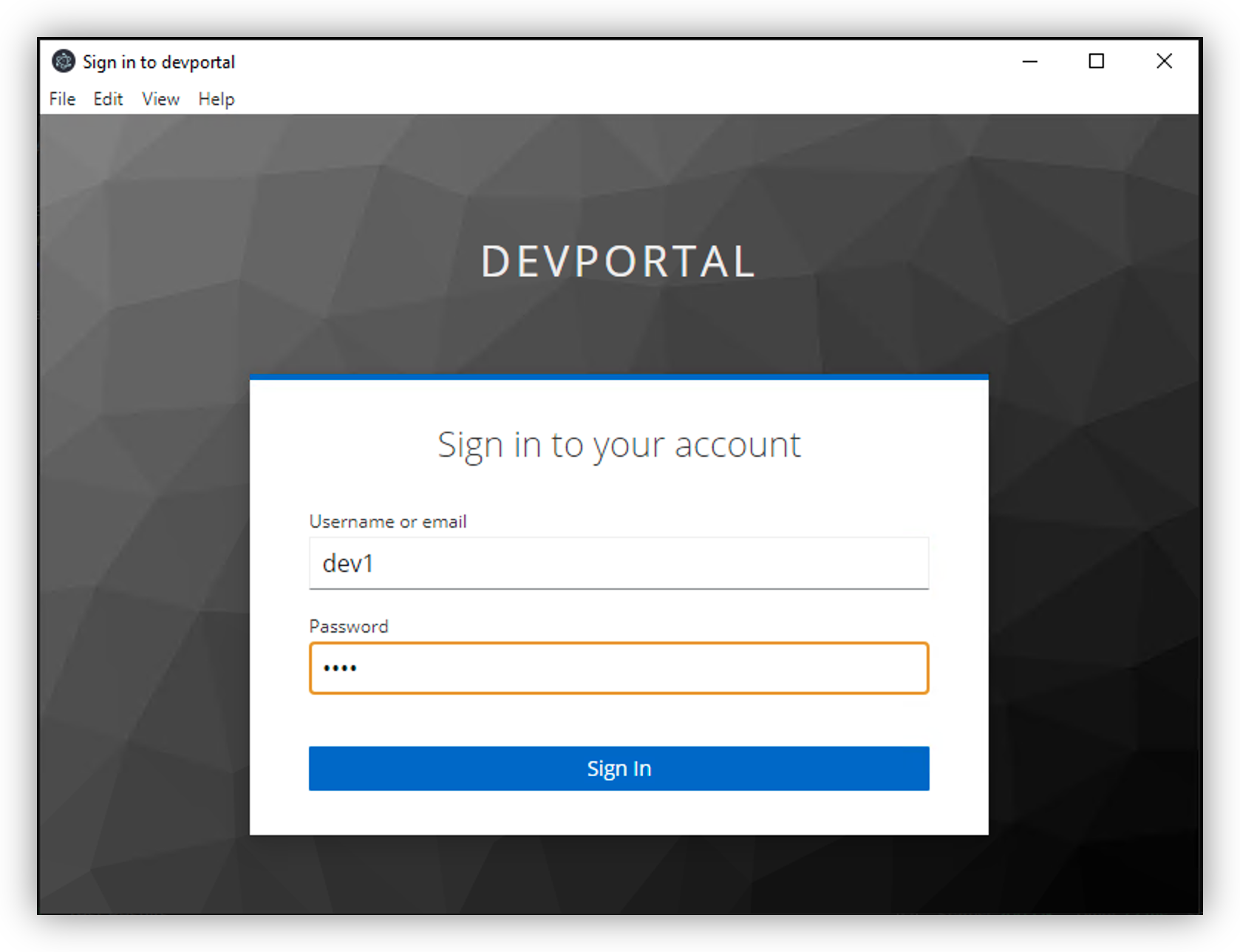
Click
Proceed, thenUse Token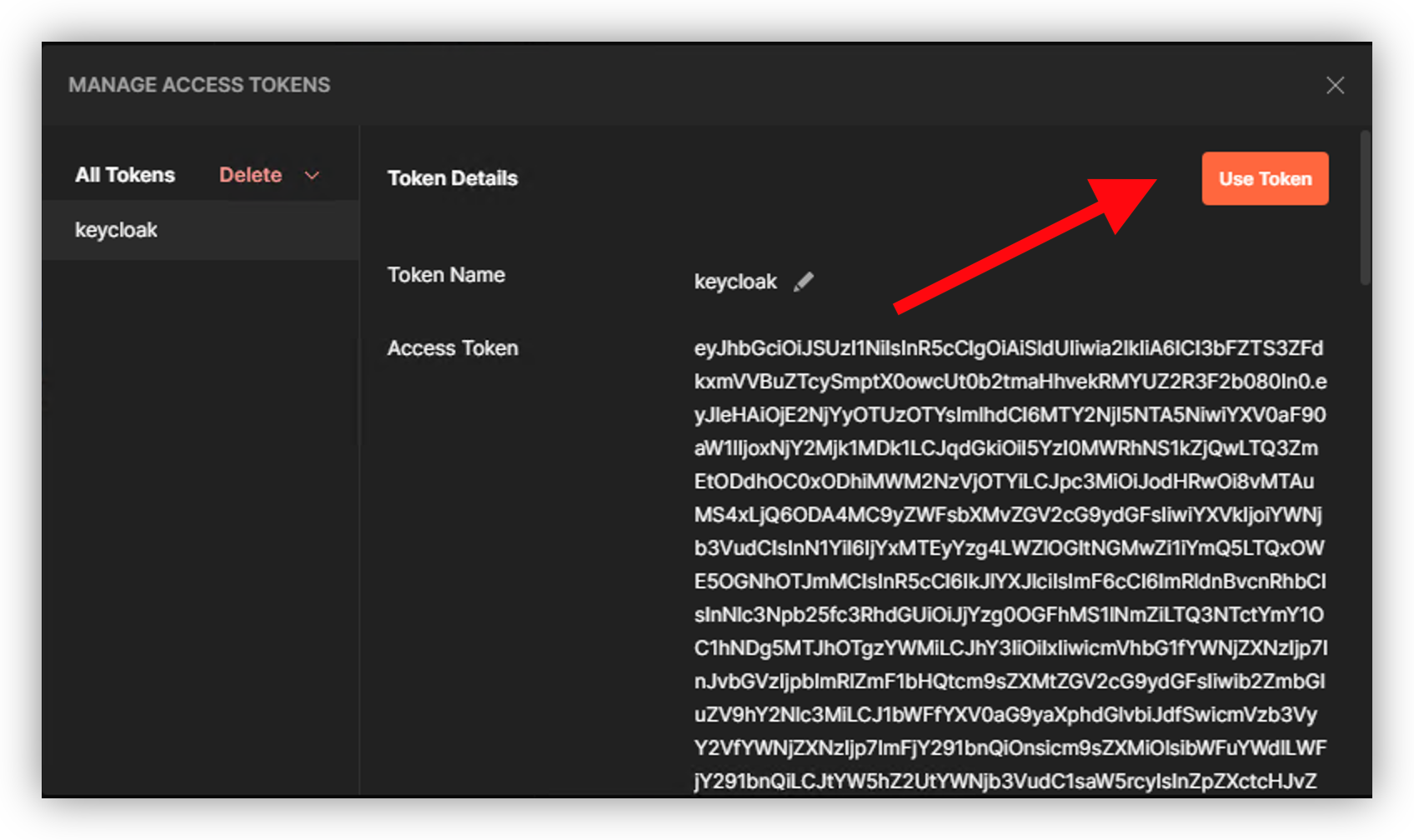
Send the request. It should pass.
Note
Congratulations, you configured your API Gateway to use Oauth2 Introspection from Keycloak as Authorization Server.
Note
Remember to clean up your Postman Oauth v2 store by deleting all JWT tokens.