F5 BIG-IP SSL Orchestrator Training Lab > All SSL Orchestrator Lab Guides > SSLO 301: Automating SSL Orchestrator Deployments in Public Cloud (Agility 2022 | 2 hours) > 2. Automating BIG-IP (SSL Orchestrator) Provisioning with Terraform Source | Edit on
2.6. Review the Deployment in AWS Console¶
Now, you will check the objects that were created by Terraform. The deployment includes the following:
VPC and Subnets
Route Tables
Transit Gateway
Network Interfaces
Elastic IP Addresses
SSH Keypair
EC2 Instances
Return to your web browser and ensure that you are logged into the AWS Console.
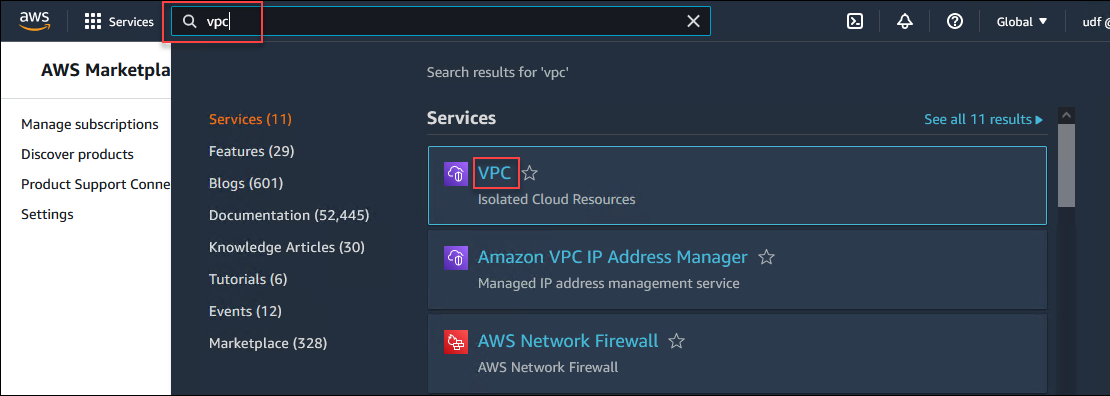
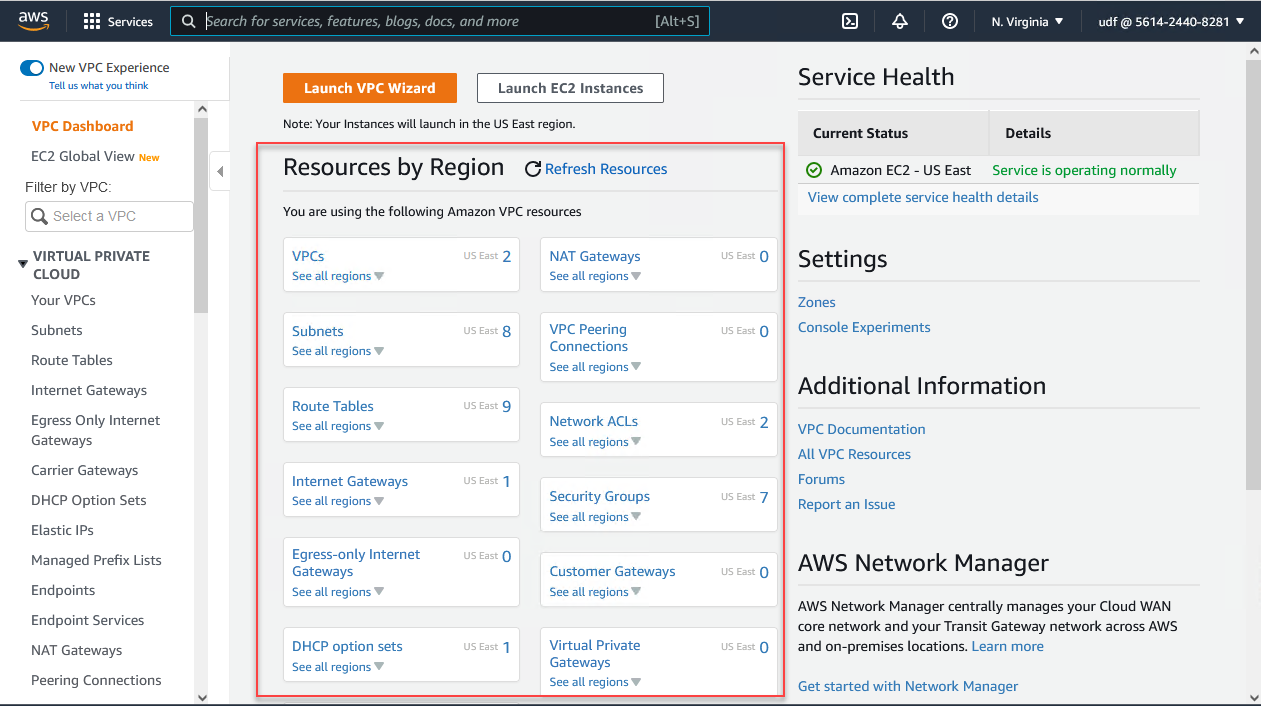
2.6.1. VPC Dashboard¶
Type vpc in the AWS Console search box at the top of the page and select VPC from the search results.
The VPC Dashboard will show a summary of your resources.
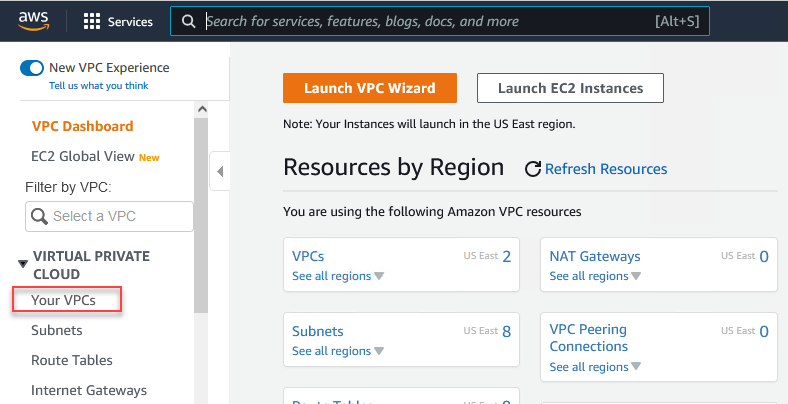
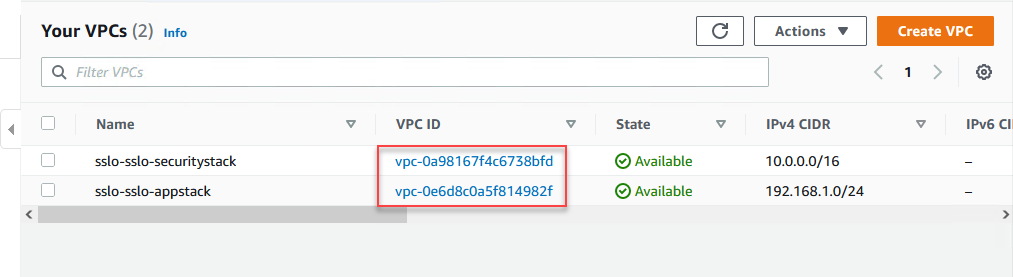
2.6.2. VPC and Subnets¶
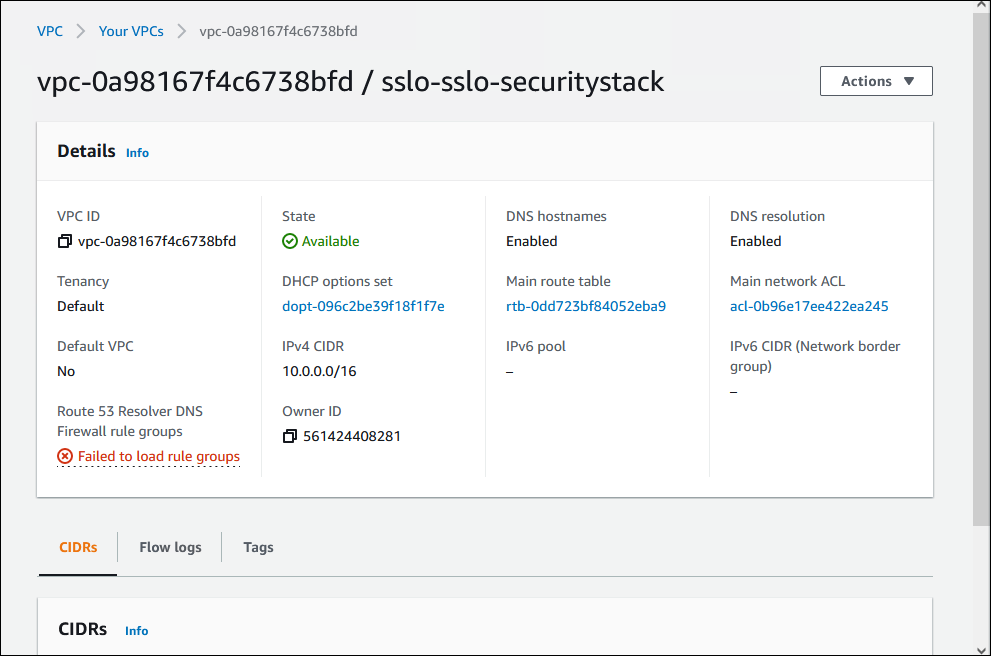
Click on Your VPCs from the left panel menu.
Two (2) VPCs were created.
Click on the sslo-sslo-securitystack VPC ID to view the configuration.
You may ignore the "Failed to load rule groups" error.
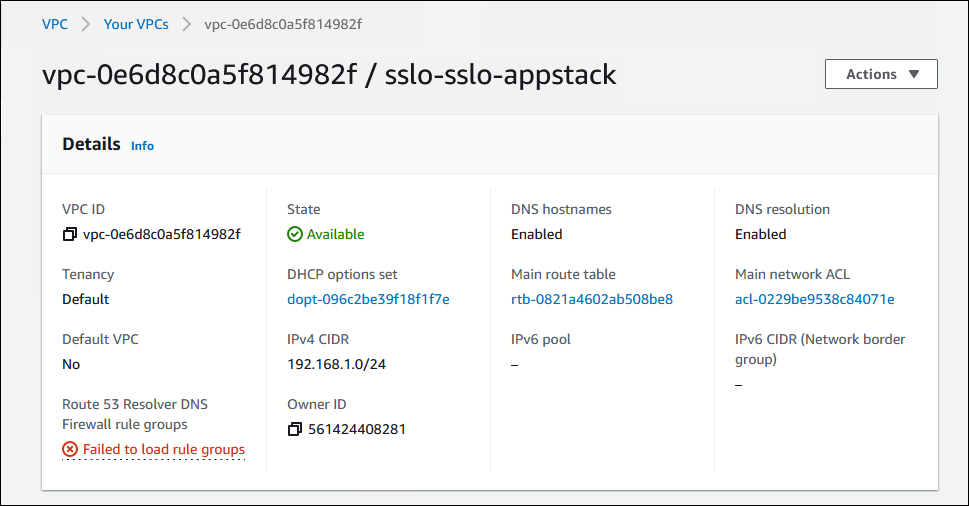
Click on Your VPCs to return to the VPCs list and then click on the sslo-sslo-appstack VPC ID.
You may ignore the "Failed to load rule groups" error.
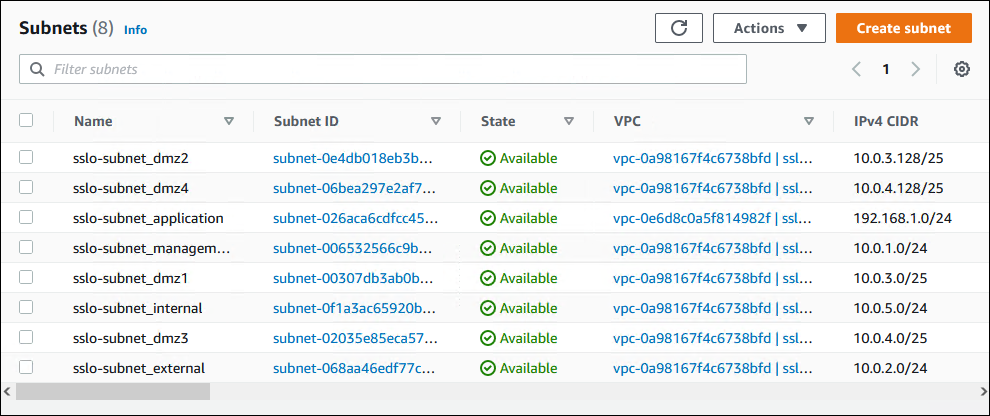
Click on Subnets from the left panel menu and confirm that following resources were created:
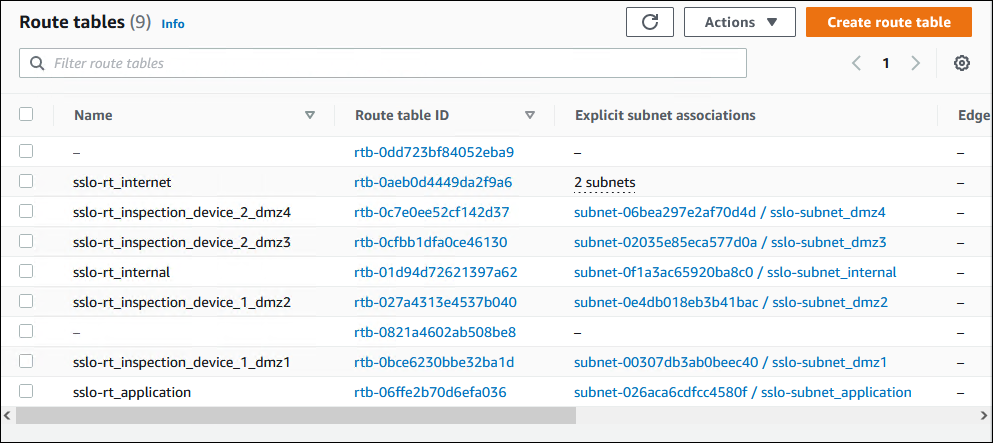
2.6.3. Route Tables¶
Click on Route Tables from the left panel menu and confirm that the following resources were created:
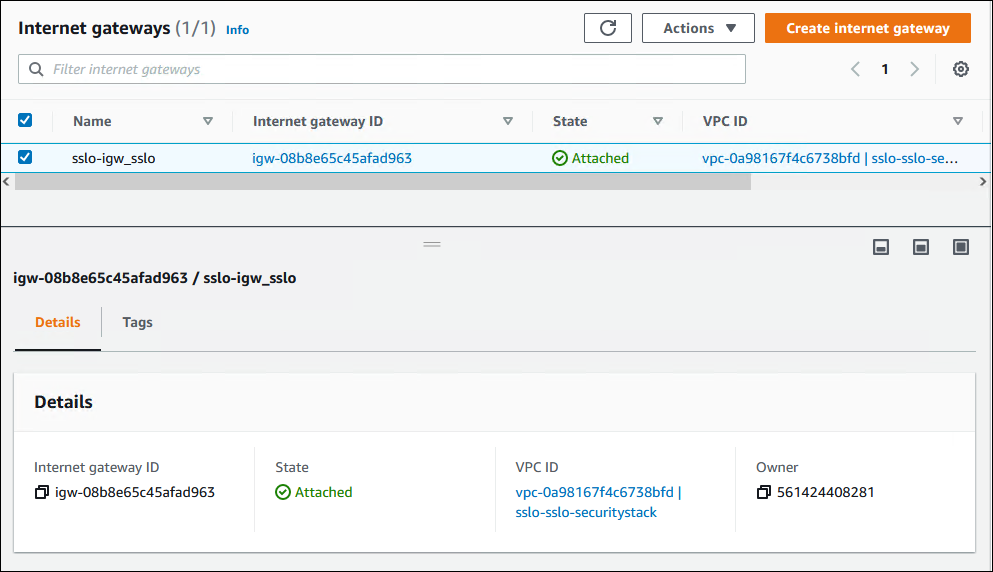
2.6.4. Internet Gateway¶
Click on Internet Gateways from the left panel menu and confirm that the following resource was created:
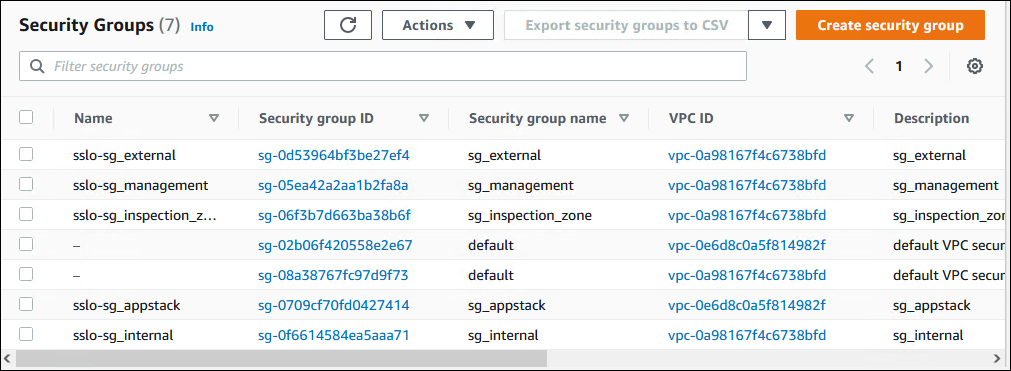
2.6.5. Security Groups¶
Scroll down in the left panel menu to the SECURITY section and click on Security Groups.
Confirm that the following resources were created:
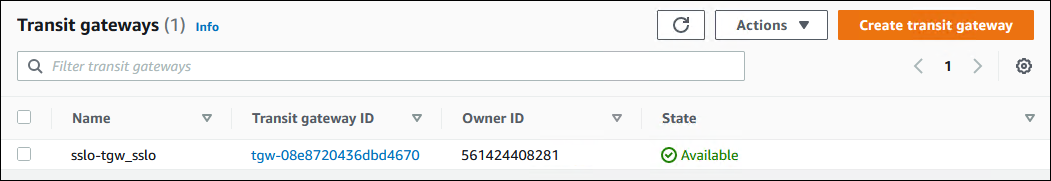
2.6.6. Transit Gateway¶
Scroll down in the left panel menu to find and click on Transit Gateways.
Confirm that the following resources were created:
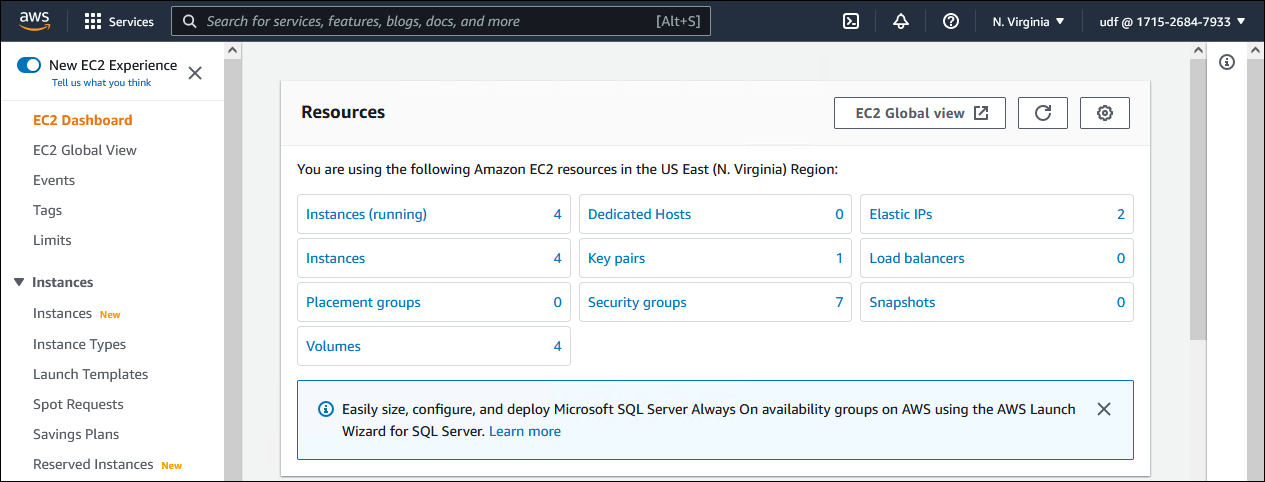
2.6.7. EC2 Dashboard¶
Type ec2 in the AWS Console search box at the top of the page and select EC2 from the search results.
The EC2 Dashboard will show a summary of your resources.
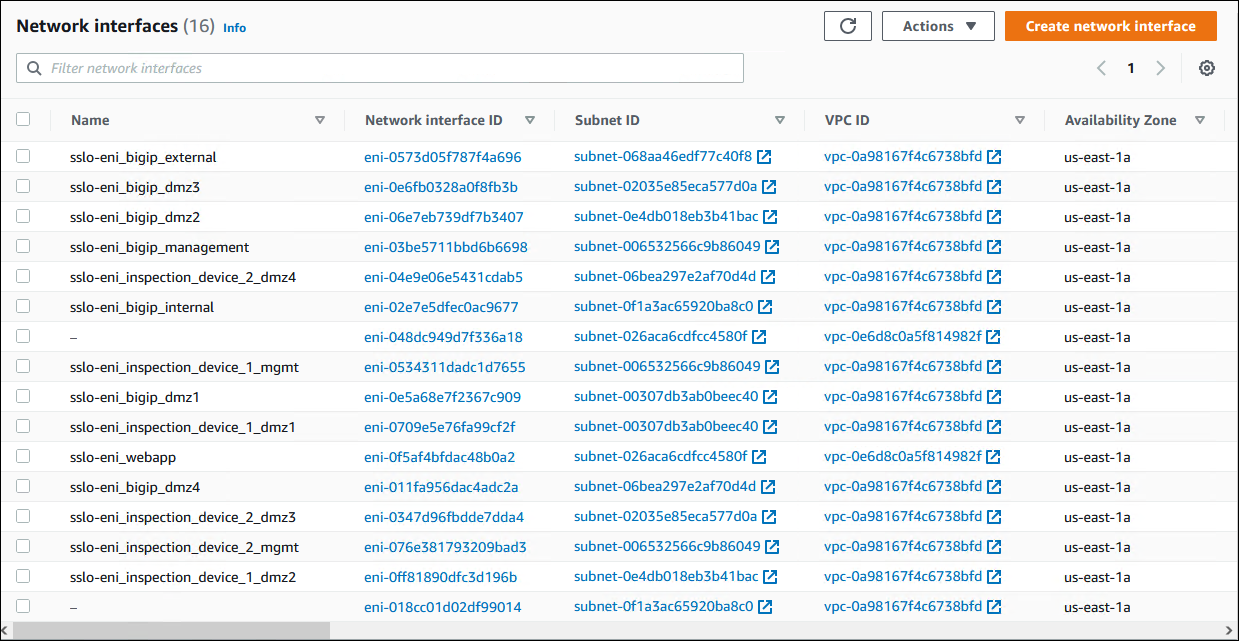
2.6.8. Network Interfaces¶
Scroll down in the left panel menu to find and click on Network Intefaces.
Confirm that the following resources were created:
The BIG-IP (SSL Orchestrator) uses 7 NICs (management, external, internal, dmz1, dmz2, dmz3, dmz4).
The first inspection device uses 3 NICs (management, dmz1, dmz2).
The second inspection device uses 3 NICs (management, dmz3, dmz4).
The webapp server uses 1 NIC (application).
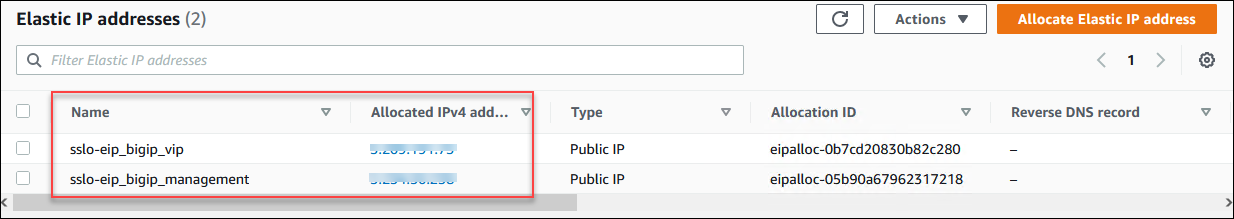
2.6.9. Elastic IP Addresses¶
Click on Elastic IPs from the left panel menu and confirm that the following resources were created:
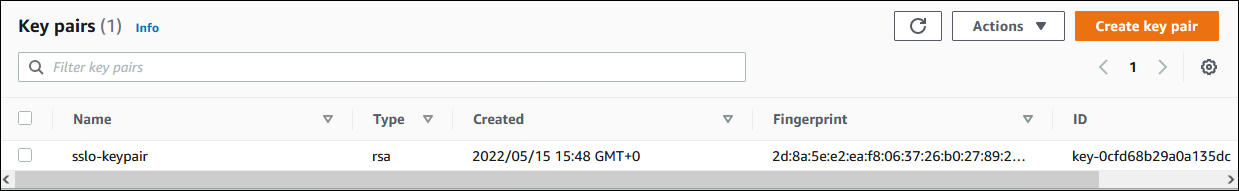
2.6.10. SSH Key¶
Click on Key Pairs from the left panel menu and confirm that the following resource was created:
2.6.11. EC2 Instances¶
Click on Instances from the left panel menu and confirm that the following resources were created:
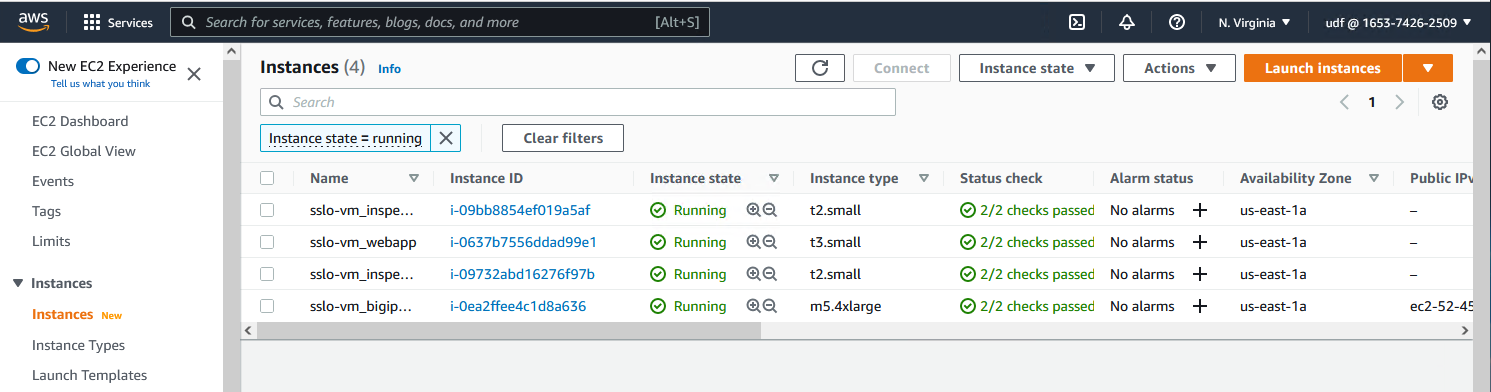
Attention
The sslo-vm_bigip_sslo instance might still be in Initializing state (look at the Status check column). Eventually, this will transition to 2/2 checks passed.
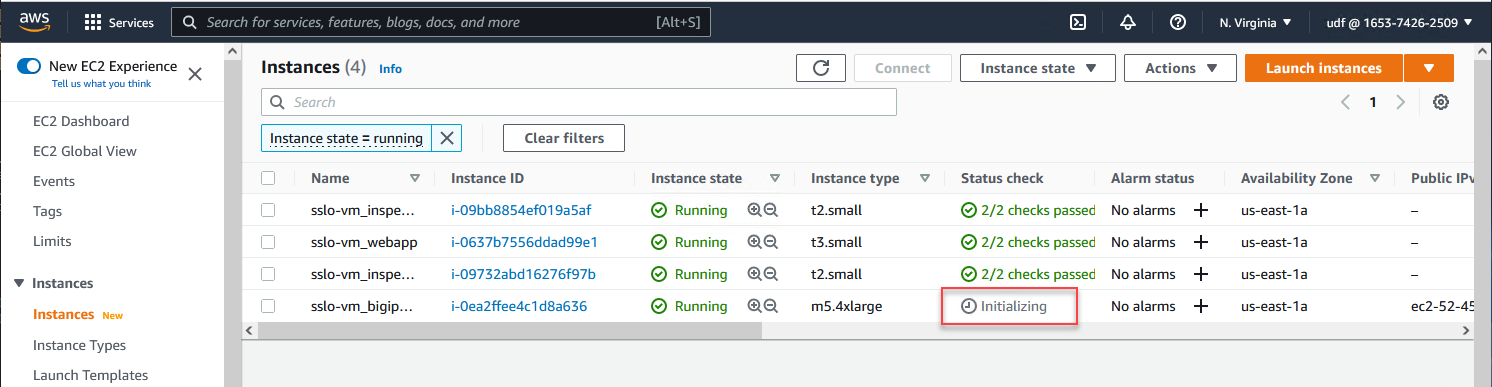
Do not proceed until the Status check column is green for all instances.