F5 BIG-IP SSL Orchestrator Training Lab > All SSL Orchestrator Lab Guides > SSLO 202: More Use Cases with F5 BIG-IP SSL Orchestrator (AppWorld 2025 | 2 hours) > 2. Lab 1: Inbound Gateway Topology Source | Edit on
2.4. Testing the Deployment¶
You will now test the SSL Orchestrator Topology and perform an attack against the applications to see the difference in behavior between the two Service Chains.
2.4.1. Access the Ubuntu-client Desktop¶
From the Deployment tab in the UDF console, select ACCESS > WEBRDP for the Ubuntu-Server resource (Components > Ubuntu-Server > ACCESS > WEBRDP).
A new tab will open and present the Guacamole login screen.
Note
The Guacamole application is hosted on the Ubuntu-Server machine, but creates an RDP connection to the desktop of the Ubuntu-Client machine.
Log in as
userwith passworduser.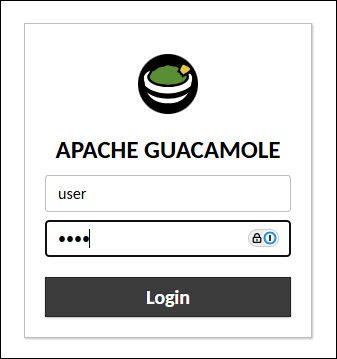
The first time that you connect to the desktop, you will be prompted for permission to "See text and images copied to the clipboard". Click on the Allow button to close the dialog box.
You should now see the desktop of the Client machine.
2.4.2. Attack Juiceshop Application #1 (jsapp1.f5labs.com)¶
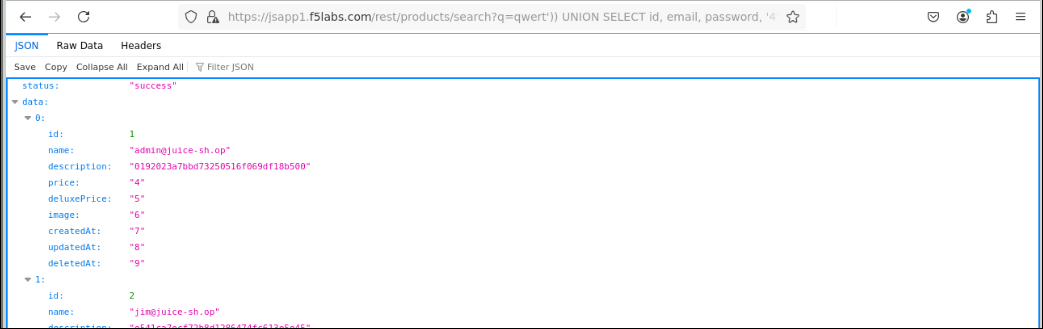
You will now perform a SQL Injection (SQLi) attack to test the inspection services associated with jsapp1.
Launch the Firefox browser and browse to the following URL:
https://jsapp1.f5labs.com/rest/products/search?q=qwert')) UNION SELECT id, email, password, '4', '5', '6', '7', '8', '9' FROM Users--
Tip
Hover your mouse pointer over the above text box to reveal the copy icon and then click on it. Now, paste it into the Firefox address bar.
The method used to paste will vary based on your local computer's operating system and target.
Paste Into
Windows
MacOS
Firefox (WEBRDP)
CTRL-V (or Right-Mouse-Click and then select Paste)
CTRL-CMD-SHIFT to bring up Guacamole menu, select Text Input, and then CMD-V
WEB SHELL
CTRL-SHIFT-V
CMD-V
If you see a TLS security warning, accept it and continue. The lab's private Certificate Authority certificate might not be installed in Firefox.
You should see that the attack reached the application server and returned unauthorized data from the user account database. This is a major vulnerability in the application.
Recall that Service Chain 1 contained only the IPS service, which isn't sufficient to protect against this type of attack.
2.4.3. Attack Juiceshop Application #2 (jsapp2.f5labs.com)¶
You will now perform a SQL Injection attack to test the inspection services associated with jsapp2.
Launch the Firefox browser and browse to the following URL:
https://jsapp2.f5labs.com/rest/products/search?q=qwert')) UNION SELECT id, email, password, '4', '5', '6', '7', '8', '9' FROM Users--
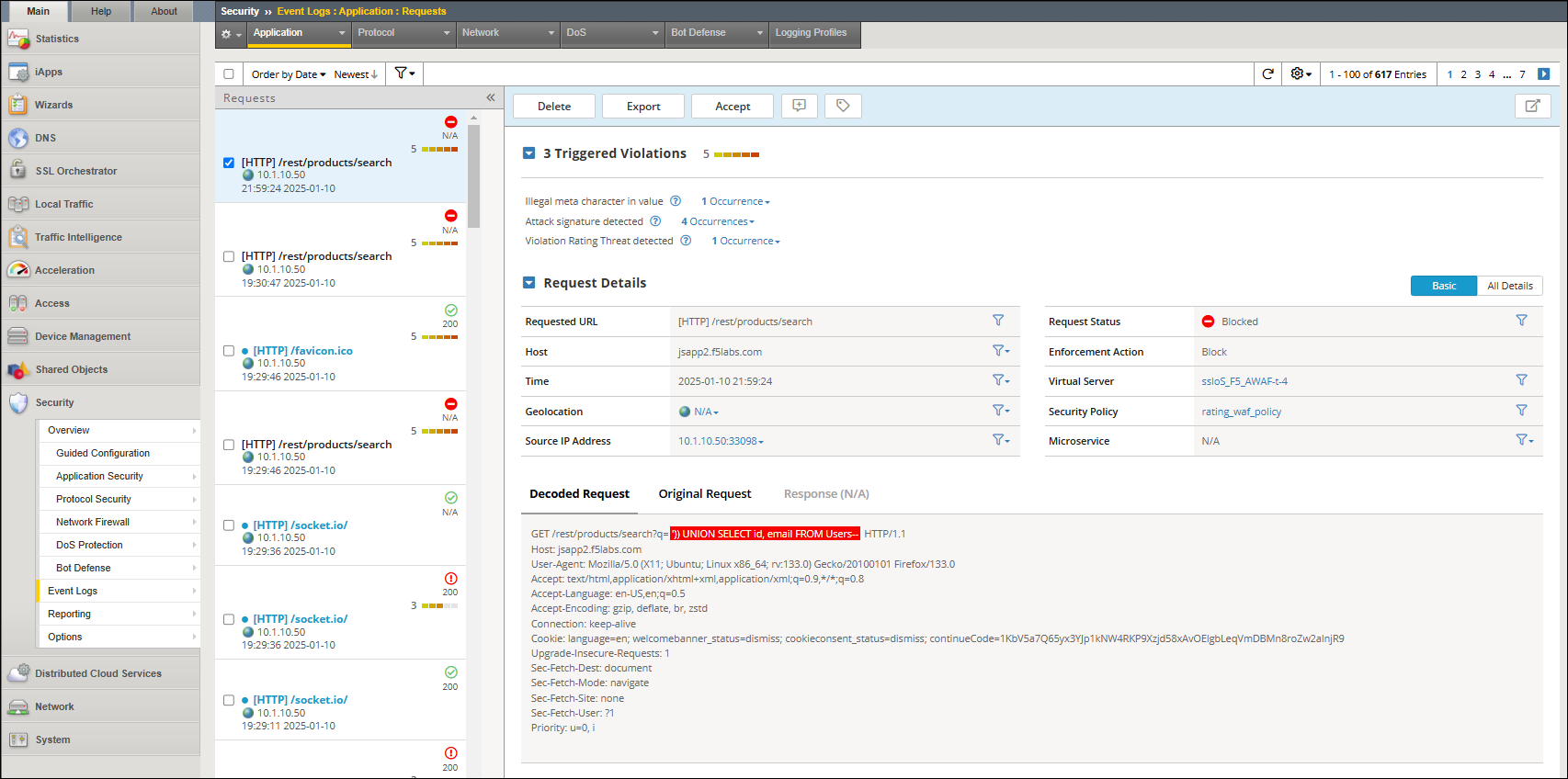
Recall that Service Chain 2 contained both the FireEye and F5 Advanced WAF inspection services. This time, the attack was blocked by the WAF policy.
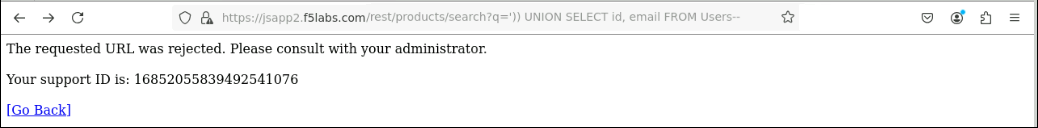
In the BIG-IP TMUI, navigate to Security > Event Logs to view the WAF violation details.