F5 BIG-IP SSL Orchestrator Training Lab > All SSL Orchestrator Lab Guides > SSLO 202: More Use Cases with F5 BIG-IP SSL Orchestrator (AppWorld 2025 | 2 hours) > 3. Lab 2: Outbound Transparent Forward Proxy with User Coaching Source | Edit on
3.6. Enable User Justification¶
Let's take the user coaching functionality a step further by enabling the user justification option which requires the user to provide a reason for accessing that destination.
3.6.1. Modify User Coaching iRule¶
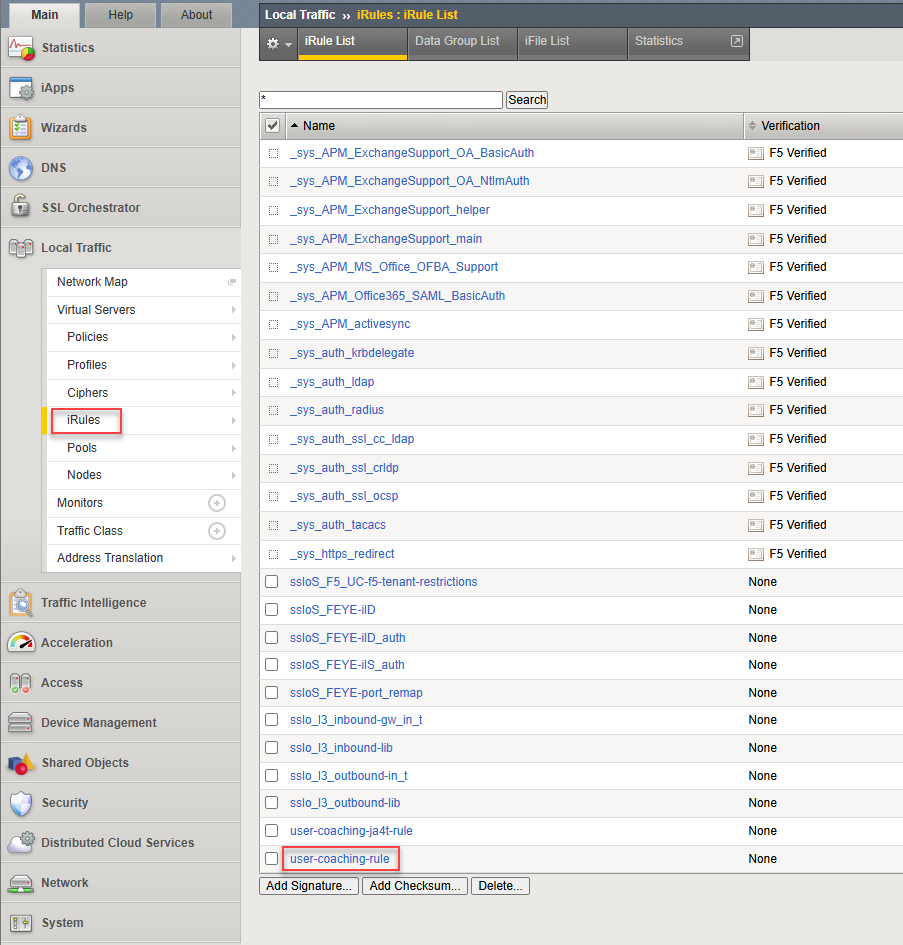
In the BIG-IP TMUI, navigate to Local Traffic > iRules.
Click on the user-coaching-rule iRule to edit it.
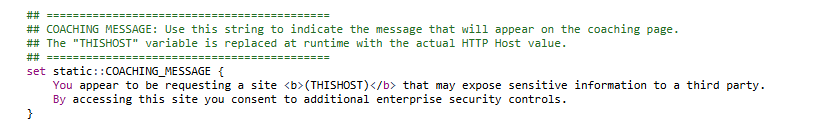
Notice that the coaching message text is defined as a variable called COACHING_MESSAGE. This allows you to customize the message based on your organization's policies. Do not change it at this time.
Below that, notice that the JUSTIFICATION_LOGGING variable is set to "" (empty string).
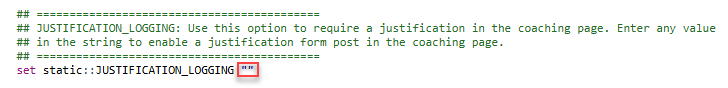
In between the double quotation marks, enter
onto enable this feature.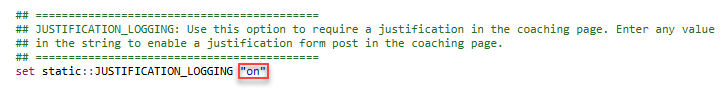
Click on the Update button to save your change.

3.6.2. Test User Justification¶
Return to the Ubuntu-Client WEBRDP session.
Close the Firefox browser window and restart the application.
Navigate to https://copilot.microsoft.com/ again. Since you acknowledged the user coaching prompt previously (without requiring justification), you will not be prompted again.
Navigate to a new site: https://gemini.google.com/. Now, the user coaching prompt appears but also includes a text box for users to enter a justification/reason for accessing that destination.
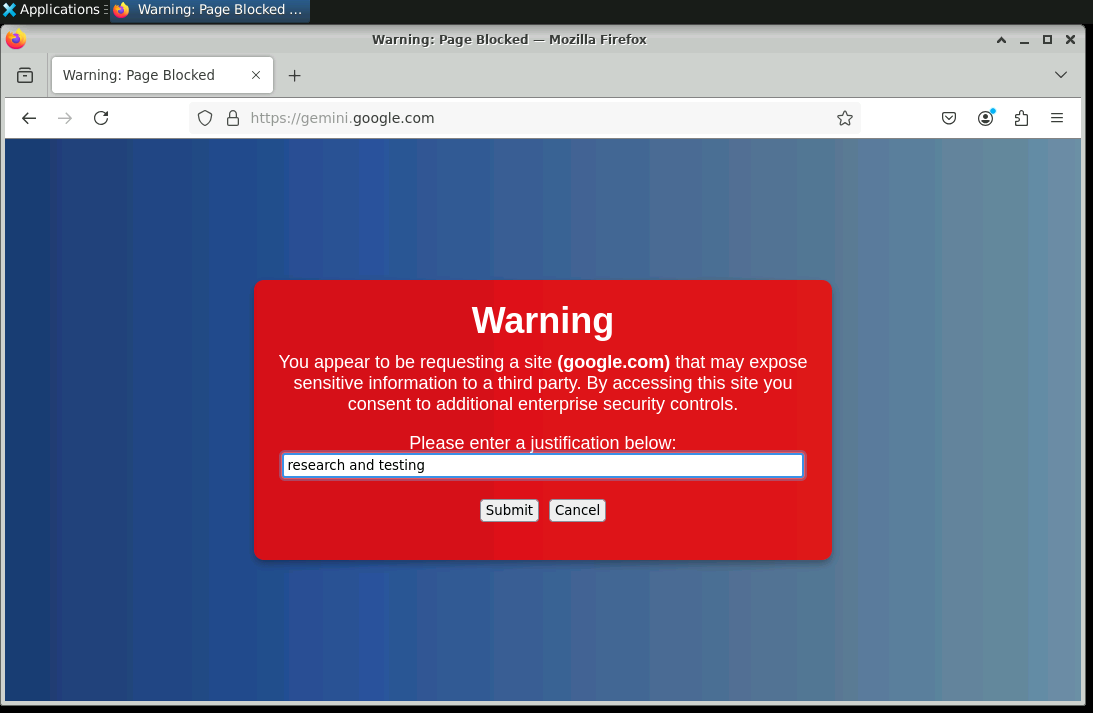
Enter
research and testingin the text box and click on the Submit button to acknowledge the warning and terms of use policy. You will then be presented with the requested destination web site.
3.6.3. Review User Coaching Logs¶
The user coaching iRule has logging enabled (currently local logging, but could be sent to an external log collector or SIEM). Let's take a look at what has been logged.
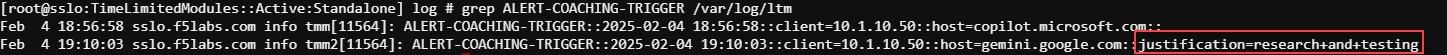
Return to the BIG-IP SSL Orchestrator Web Shell tab.
Enter
grep ALERT-COACHING-TRIGGER /var/log/ltmto extract the user coaching logs from the LTM log file. You should see log entries similar to the following: