F5 BIG-IP SSL Orchestrator Training Lab > All SSL Orchestrator Lab Guides > SSLO 201: Advanced Use Cases with SSL Orchestrator (Agility 2022 | 2 hours) > 4. Web Application Firewall-as-a-Service (WAFaaS) Source | Edit on
4.6. Validate WAFaaS¶
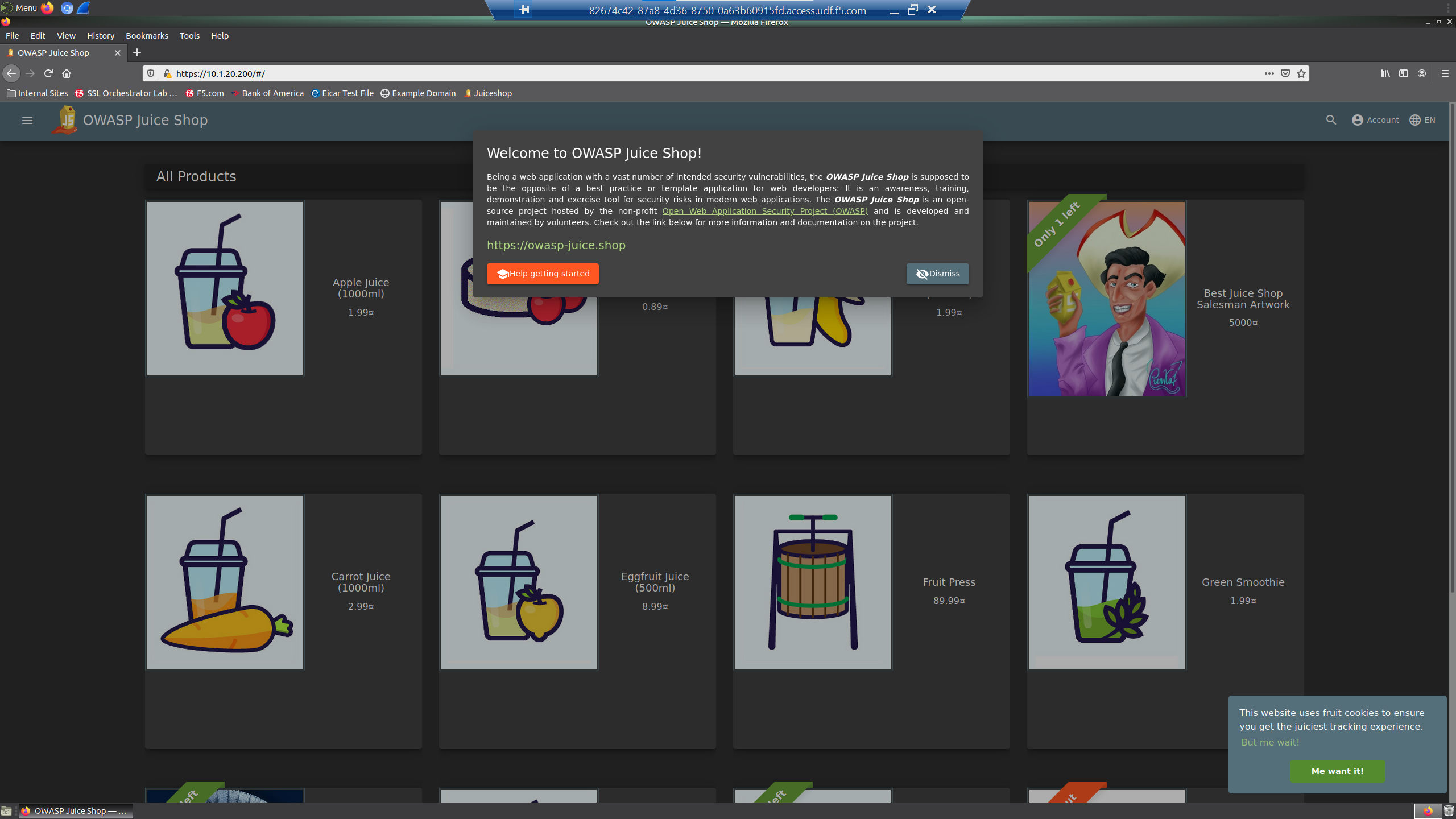
Let's take a look to see if our WAFaaS is providing the protection that we are looking for.
RDP back into the Ubuntu Client 18.04. (Components > Ubuntu18.04 Client > ACCESS > XRDP)
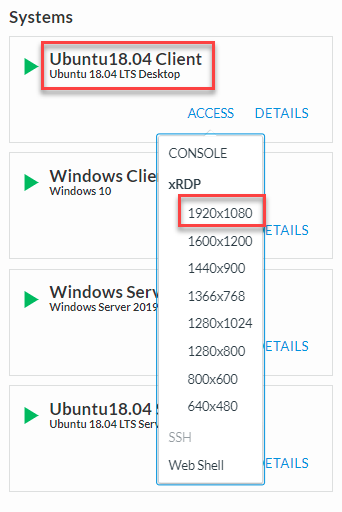
When prompted, save the RDP file to your local machine and then open it to connect.
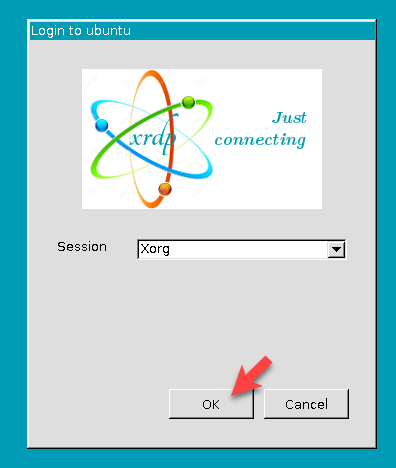
At the Ubuntu Login prompt, click on the OK button to continue.
Tip
If the RDP session times out, refer to the User Credentials for the student user password.
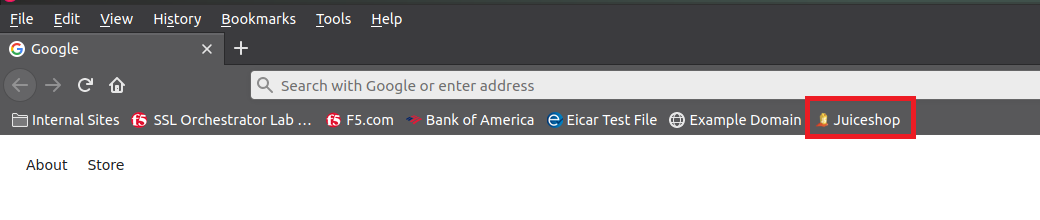
Open the Firefox browser
Click on the Juiceshop bookmark on the browser bar
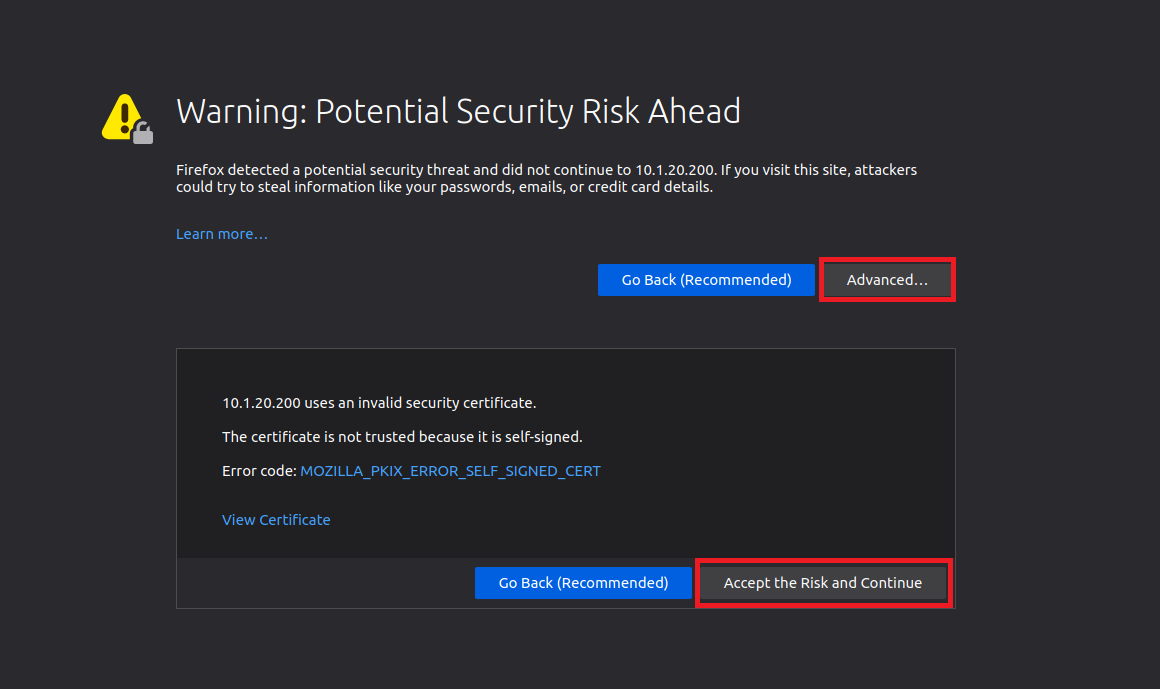
Accept the security risk by clicking Advanced and Accept the Risk and Continue. This is due to the BIGIP using a self-signed certificate.
Now we will try the same simple SQL injection attack that we used at the beginning of this lab.
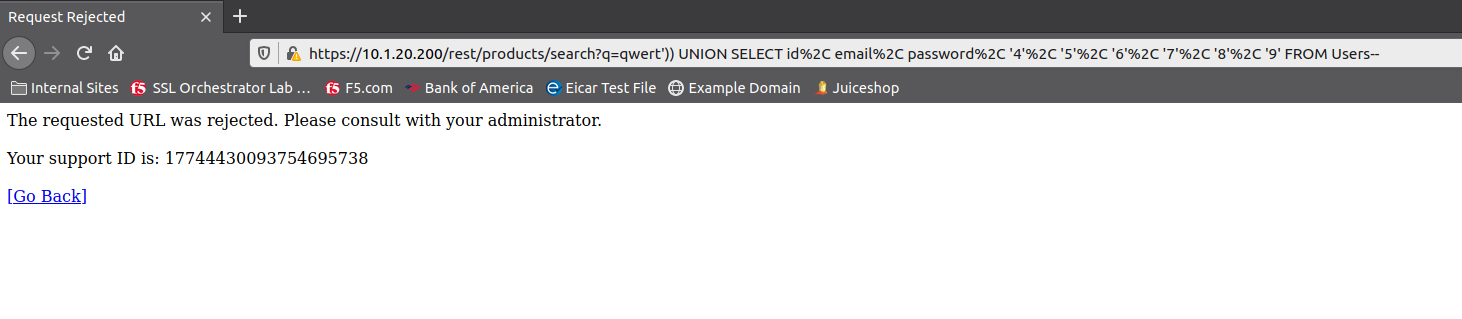
Copy and Paste the following path in your browser's location bar after https://10.1.20.200/
/rest/products/search?q=qwert%27%29%29%20UNION%20SELECT%20id%2C%20email%2C%20password%2C%20%274%27%2C%20%275%27%2C%20%276%27%2C%20%277%27%2C%20%278%27%2C%20%279%27%20FROM%20Users--
The browser's location bar should look like this:
https://10.1.20.200/rest/products/search?q=qwert%27%29%29%20UNION%20SELECT%20id%2C%20email%2C%20password%2C%20%274%27%2C%20%275%27%2C%20%276%27%2C%20%277%27%2C%20%278%27%2C%20%279%27%20FROM%20Users--
The SQL-Injection attack has been successfully blocked by the WAF policy attached to your inbound topology.
Let's look at the WAF logs to see where F5 Advanced WAF blocked our SQL-Injection attack.
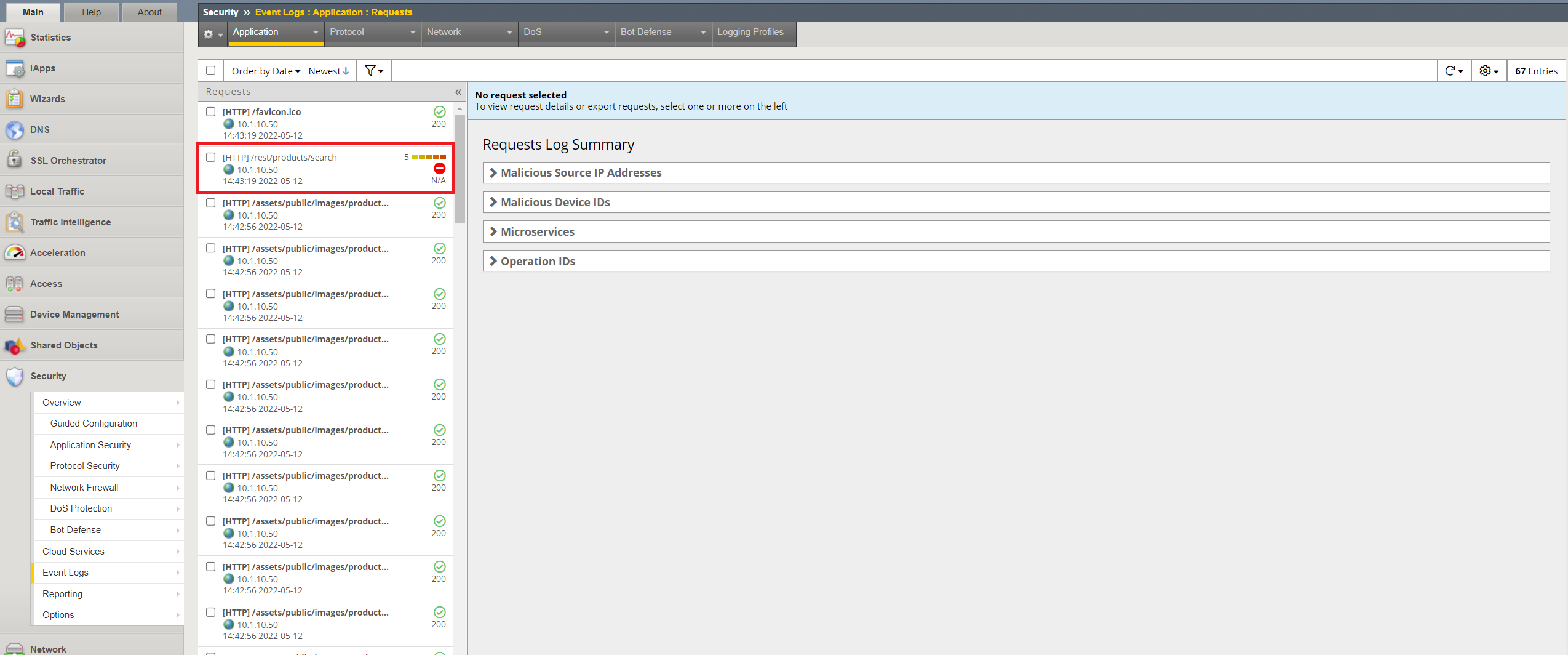
Accessing the BIG-IP, on the left side bar menu goto Security>>Event Logs>>Application>>Requests. Click on one of the log entries that has /rest/products/search.
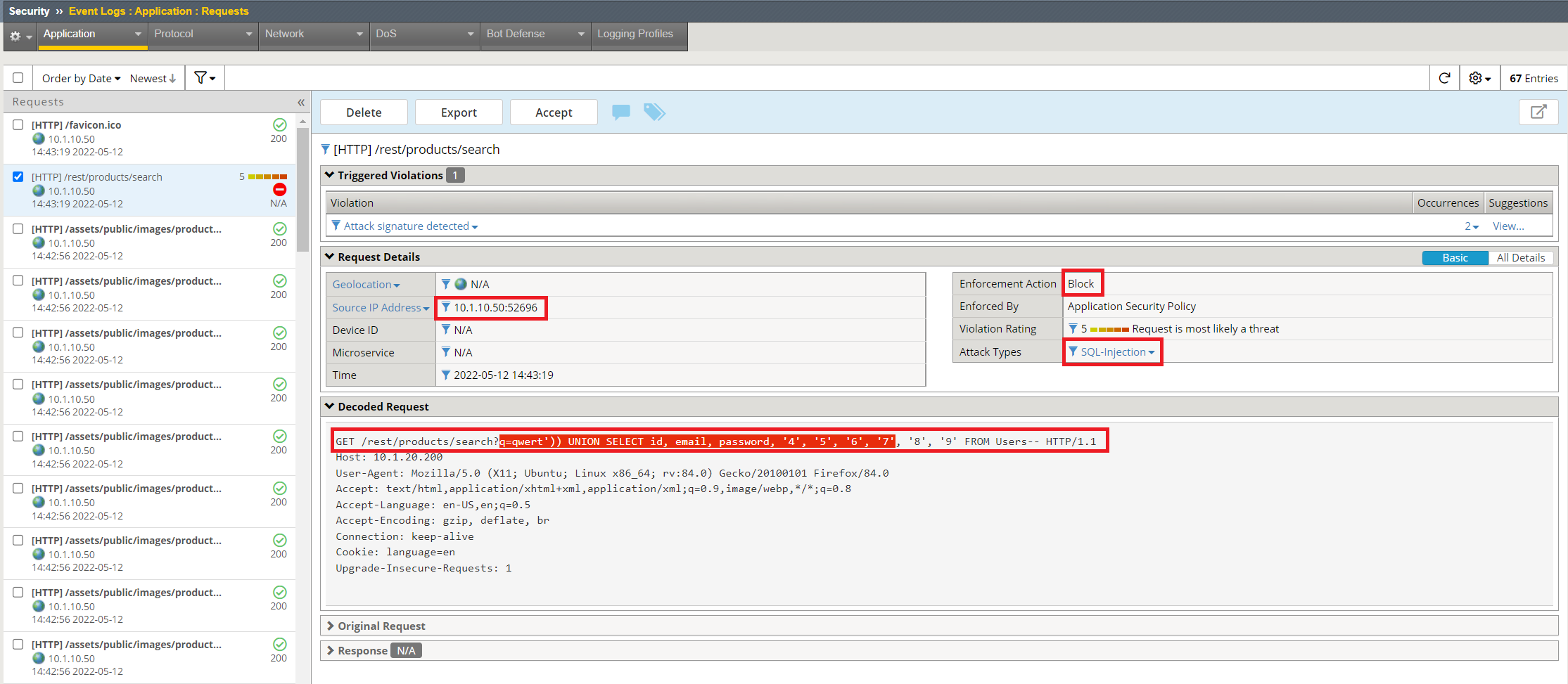
Lots of good information on this page regarding the attack. We can see that it was a SQL-Injection attack that was blocked, where it came from and even see the decoded attack.
LAB COMPLETE!!