F5 Identity and Access Management Solutions > Archived Identity & Access Management Labs > 200 Series: Assisted Deployment Use Cases Source | Edit on
Lab 4: Explore AccessGuard(15.1)¶
IMPORTANT: The F5 Access Guard is DEPRECATED and the available configuration procedure is no longer supported for all the BIG-IP versions.
F5 Access Guard is a new set of client software tools designed to help administrators validate the security posture of incoming web connections from remote clients. F5 Access Guard allows real-time posture information to be inspected with per-request policy subroutines on BIG-IP Access Policy Manager. F5 Access Guard generates posture information asynchronously and transparently transmits it to chosen APM server endpoints using special HTTP headers
APM has included posture checking capability since its inception, and this new service improves upon this capability by allowing for instantaneous and continuous checks. Deployment of F5 Access Guard is significantly different than previous posture check implementations.
Section 4.1 - XML Configuration File¶
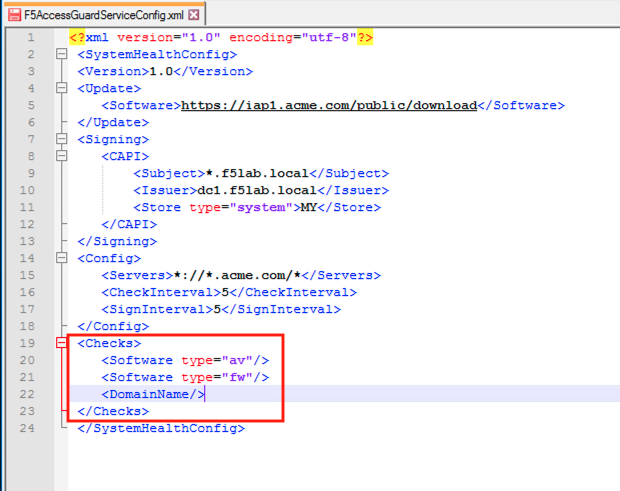
The F5 AccessGuardServiceConfig.xml file defines the settings used by the AccessGuard Service. This file contains settings for the signing certificate, timers, checks performed and websites posture data can be sent to.
Task 1 - Explore the configuration file setting¶
Note
Additional settings can be configured in the XML file beyond this example. For further information see the article Configuring F5 AccessGuard on askf5.com - https://techdocs.f5.com/en-us/bigip-15-0-0/big-ip-access-policy-manager-access-guard-config/configuring-f5-access-guard.html
Open the F5 Access Guard Config file shortcut located on the desktop by right clicking it and opening with notepad++
Note
The file is located in the C:\ProgramData\F5 Networks\F5AccessGuardService directory

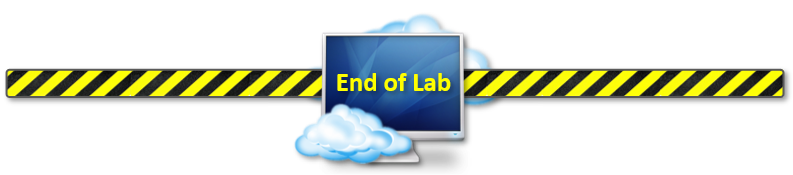
The Update section contains Software check library auto-update URI. The value specifies the location for software check (OesisInspector.cab) updates.
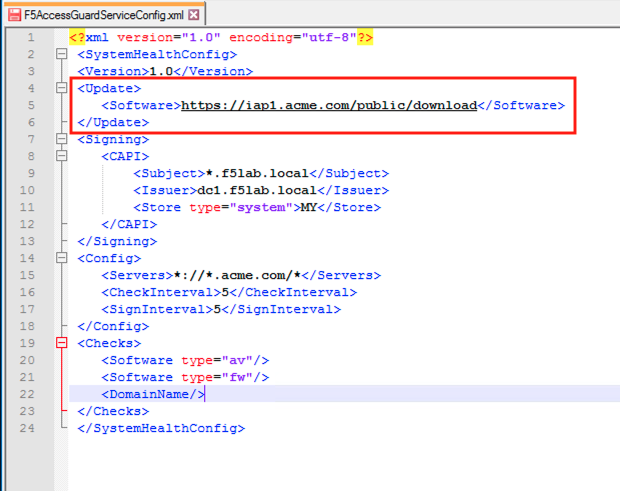
The Signing section contains the location, cert name, and Issuer Name, of the certificate/key pair used to sign the posture assessment data and
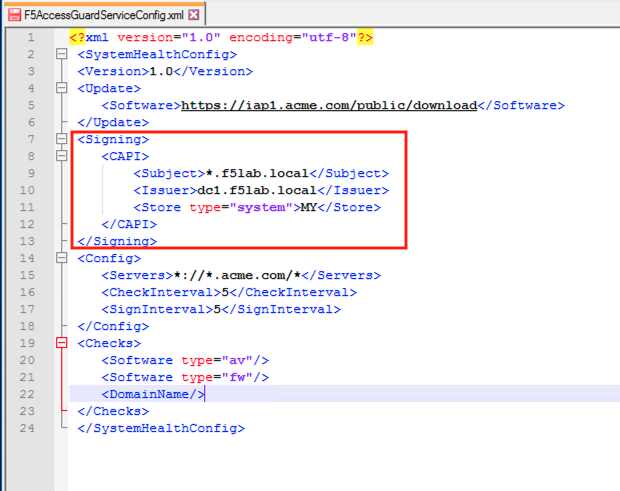
The Config section contain how often posture data is collect and signed. Also the Match patterns for URLs to which the health information would be sent via the HTTP header. This prevents AccessGuard from leaking client configuration data to an untrusted server.
The Checks section contains the check F5 AccessGuard Service will report on. As of 15.1 there are currently 10 different checks that can be performed.
Close the configuration file without saving it
Section 4.2 - System Service¶
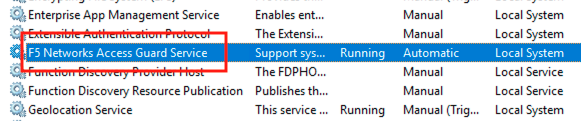
The AccessGuard System Service performs the continuous monitoring of the system based on the parameters in the previously explored F5AccessGuardServiceConfig.xml file
Task 1 - Locate the F5 Access Guard Service¶
Enter Services into the jumphost’s desktop search bar.
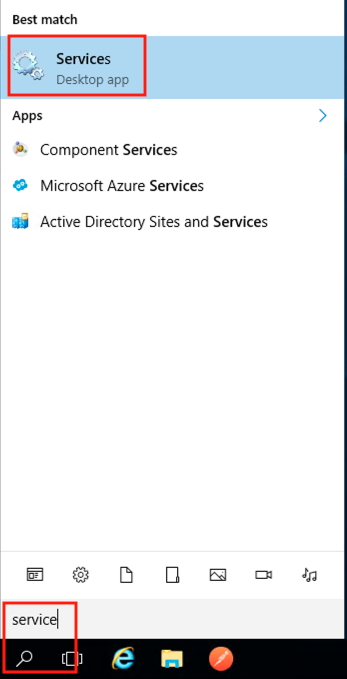
The F5 Networks Access Guard Service was installed via a .msi available on https://downloads.f5.com
Close the services screen.
Section 4.3 - Device Certificate¶
When the configuration file is set to sign posture data, it uses the specified certificate/key pair in the machines local certifcate store.
Task 1 - Explore the Device Certificate¶
Open the jump box’s certificate store by clicking the Certificate Management shortcut located on the desktop

Double click the jumpbox.f5lab.local certificate
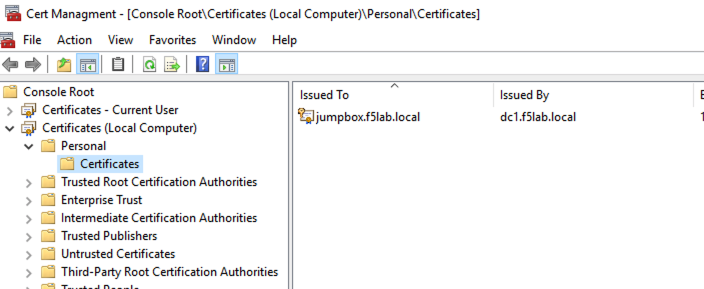
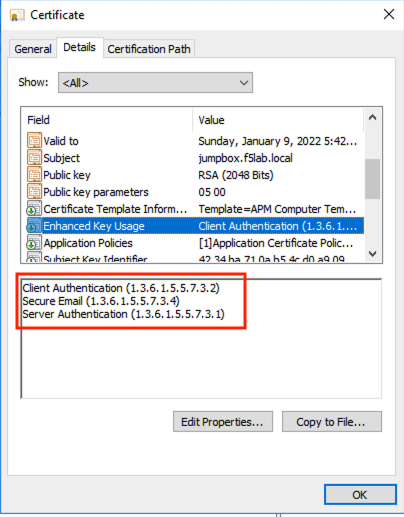
Click the Details tab and scroll to the Enhanced Key Usage section. The default usage types associated with a Microsoft CA template is Client Authentication and Server Authentication. The default template must be modified to include Secure Email.
Click OK and close the Certificate management window
Section 4.4 - Browser Extension¶
The browser extension takes the posture data generated by the Access Guard service and converts it to a header.
Task 1 - View the installed Extension¶
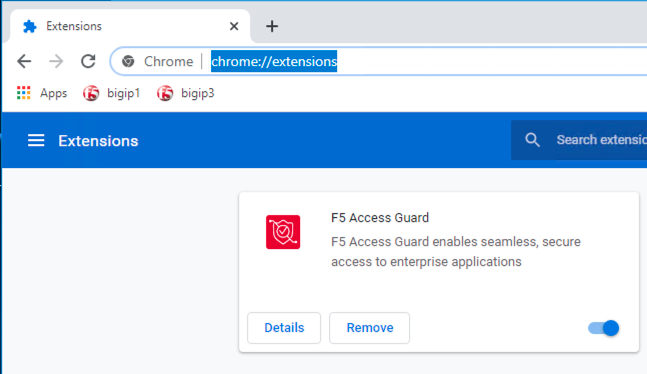
Open Chrome and enter chrome://extensions to see that the F5 Access Guard extension is installed. The extension is download and installed via a browsers extension store.
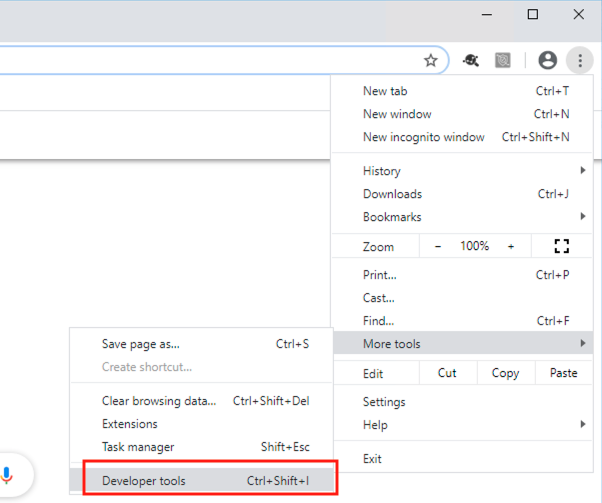
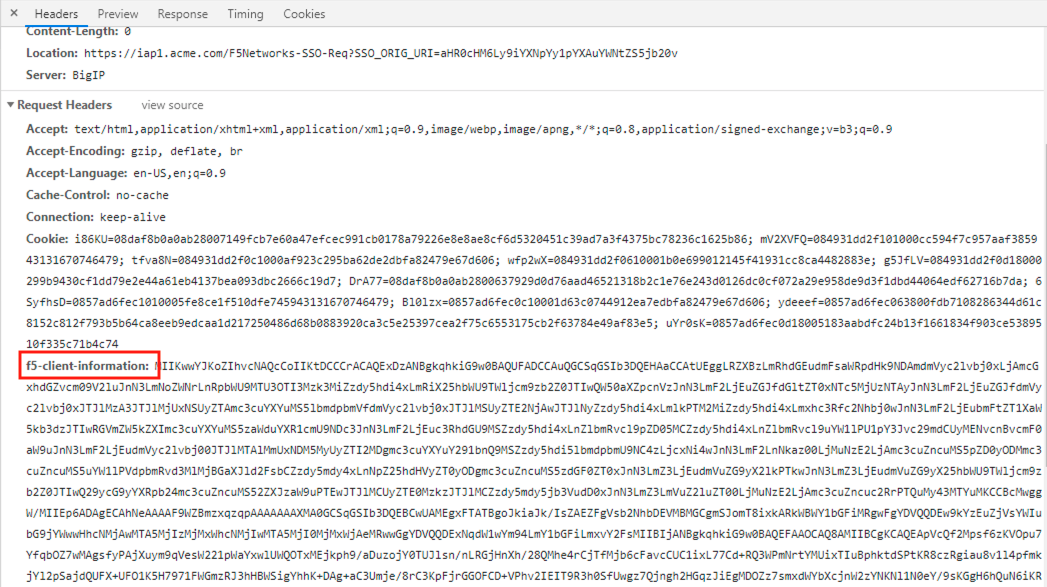
Open Developer Tools by navigating to settings >> More Tools >> Developer Tools.
Access the website https://ipa1.acme.com
Click on the request ipa1.acme.com under the network tab.
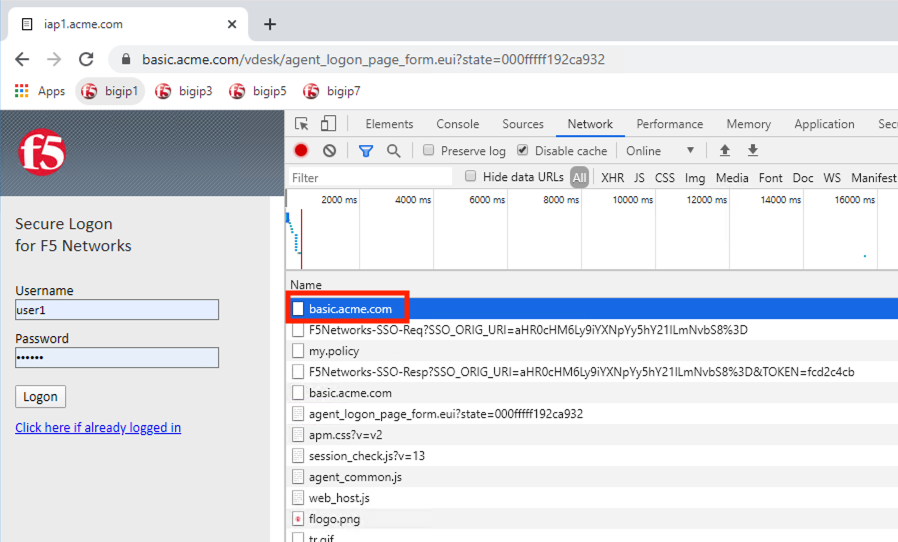
Under the Request Headers section of the request you will see an injected header called f5-client-information. This is the signed posture assessment data being sent to the BIG-IP on every request.
This concludes lab 4.