F5 BIG-IP SSL Orchestrator Training Lab > All SSL Orchestrator Lab Guides > SSLO 201: Advanced Use Cases with SSL Orchestrator (Agility 2022 | 2 hours) > 3. Internal Layered SSL Orchestrator Architecture Source | Edit on
3.7. Layered Virtual Server and Topology Steering iRule¶
Note
The SSLOLIBEXP and sslo-layering-exp-rule files from the f5devcentral/sslo-script-tools Github repository have already been imported for you. You will review the contents of these iRules shortly.
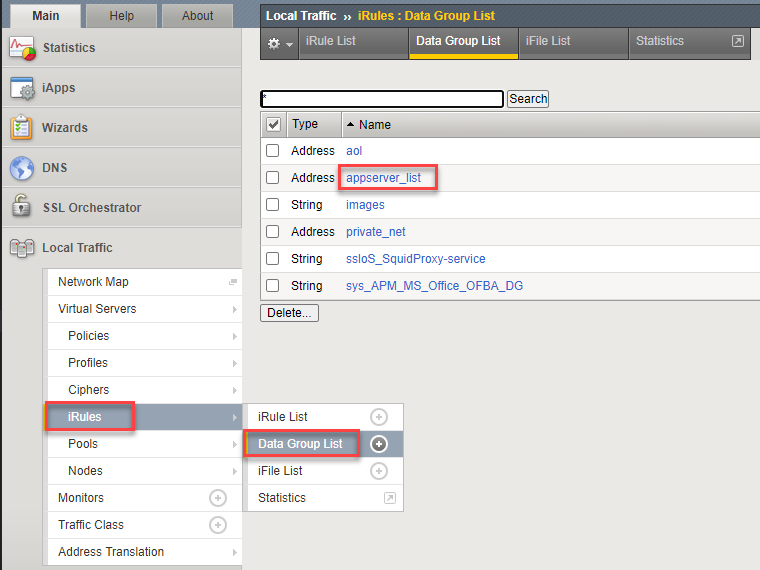
Navigate to Local Traffic > iRules > Datagroup List to view the data groups.
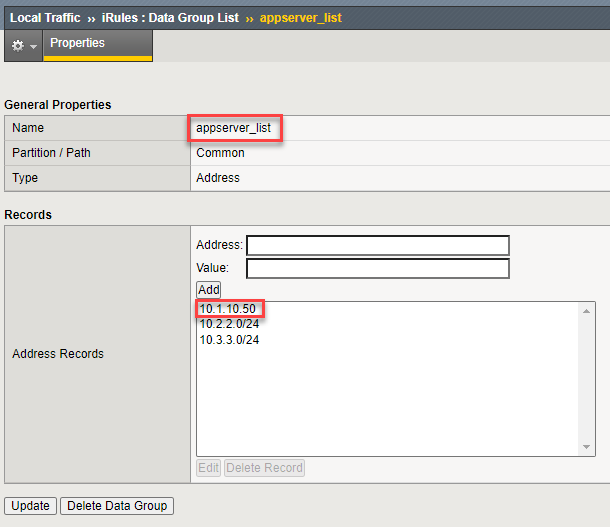
Click on the appserver_list data group to view the list of server subnets/addresses. Traffic from these source IPs will be directed to the appserver_explicit topology. Note that IP address 10.1.10.50 is the Ubuntu18.04 Client machine (representing an application server).
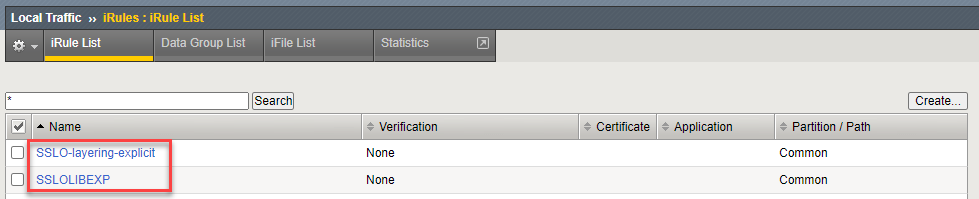
Navigate to Local Traffic > iRules > iRules List and review the two iRules.
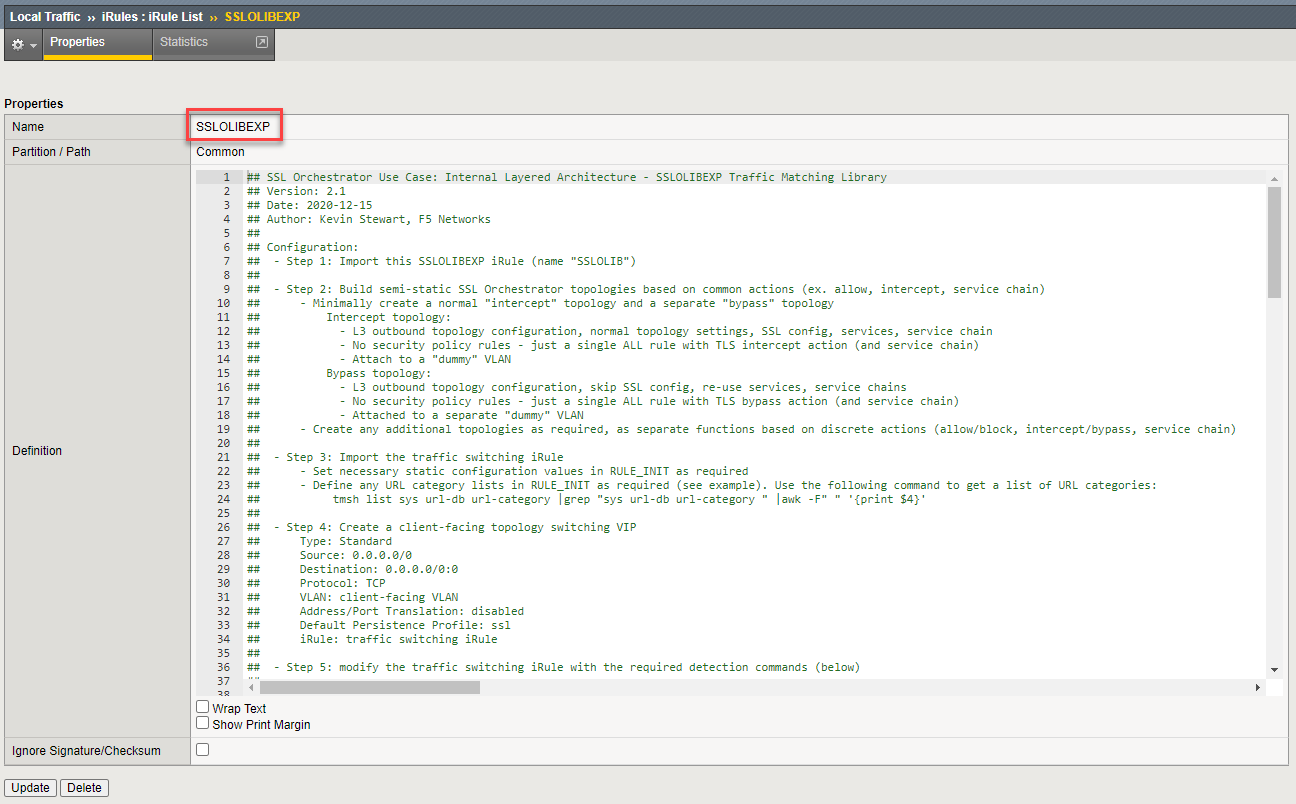
The SSLOLIBEXP iRule contains functions that allow the topology steering rule to easily match on various attributes and then target specific SSL Orchestrator topologies.
Warning
Do not modify the SSLOLIBEXP iRule.
The topology steering iRule contains your steering logic and defines the topology steering conditions.
Modify the SSLO-layering-explicit iRule with the following values:
Line 21: Replace
interceptexpwithf5labs_explicit(name of the original/existing L3 Explicit Topology). This defines the default SSL Orchestrator topology to use (if there is no other match).Insert 2 blank lines after line 41.
Copy line 45 into line 42.
Line 42: Uncomment this line by removing the '#' from the beginning of the line.
Line 42: Replace
my-srcip-dgwithappserver_list. This defines the data group to check for source address matches.Line 42: Replace
bypassexpwithappsvr_explicit(name of the new L3 Explicit Topology that you created in the previous section). This defines the topology to use if there is a source address match.
Attention
Ensure that there are no typographical errors in the iRule, or it will not function properly.
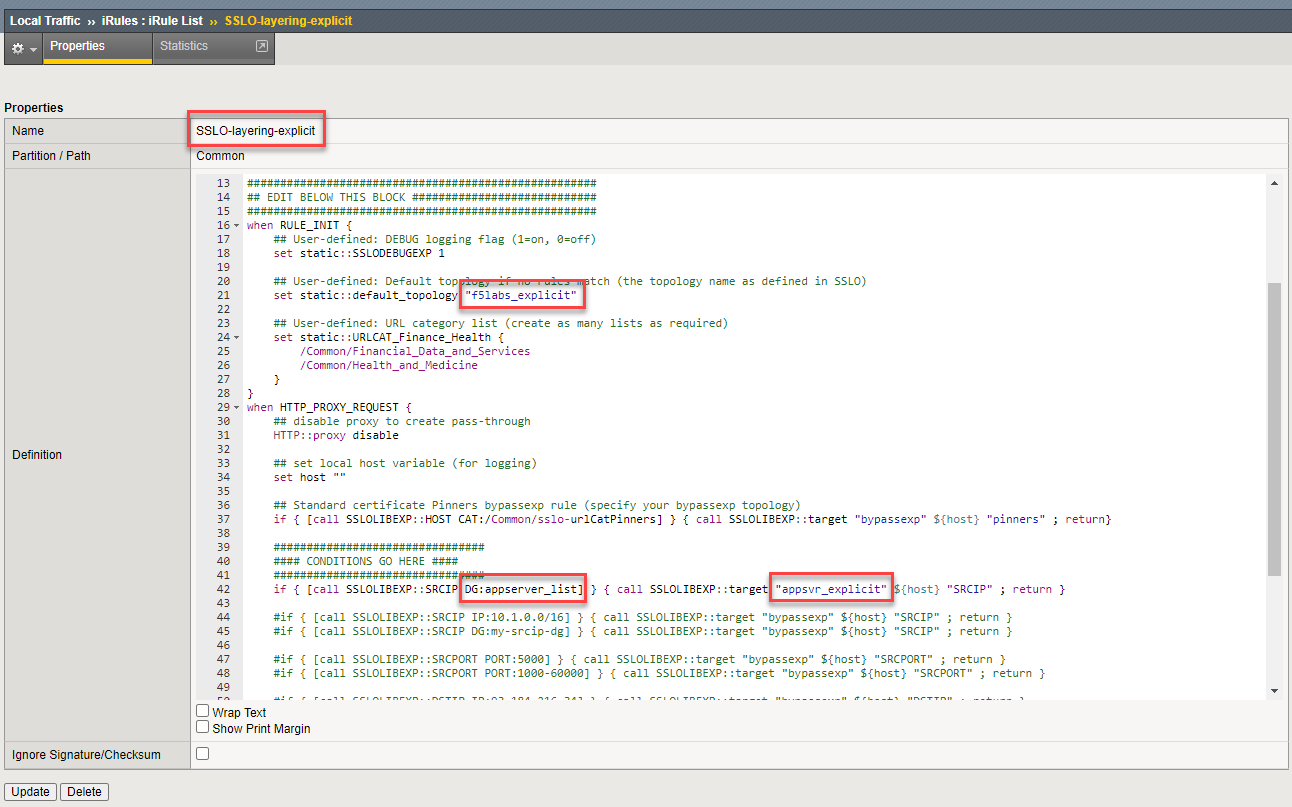
Click on the Update button to save the iRule changes.
Navigate to Local Traffic > Virtual Servers > Virtual Server List to create the topology steering virtual server.
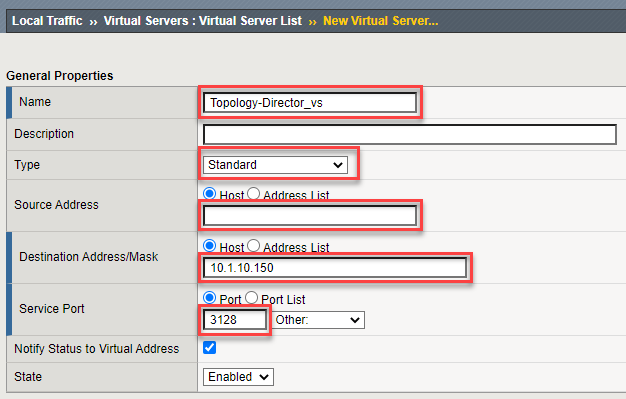
Click on the Create button to add a new Virtual Server and configure the following settings:
Name: Enter
Topology-Director_vsType: Leave the default - Standard
Source: Leave the default - empty
Destination Address: Enter
10.1.10.150Destination Port: Enter
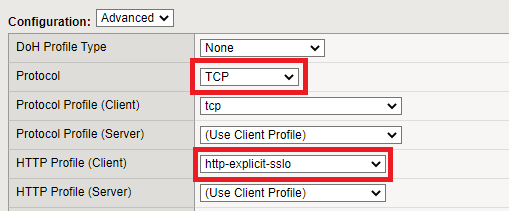
3128Protocol: Leave the default - TCP
HTTP Profile (Client): Select http-explicit-sslo
VLAN and Tunnel Traffic: Select Enabled On... and then move client-vlan to the Selected column.
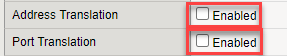
Address Translation: Uncheck to disable
Port Translation: Uncheck to disable
iRule: Move the SSLO-layering-explicit iRule to the Enabled column.
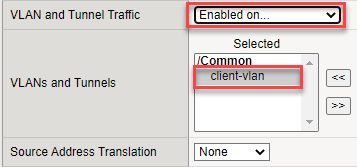
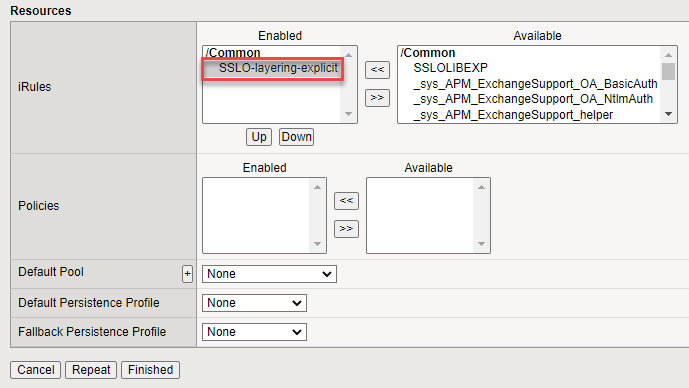
Click on Finished to create the new virtual server.