F5 BIG-IQ Centralized Management Lab > BIG-IQ All Labs > Class 4: BIG-IQ Platform > Module 1: Banner, SNMP configuration and Automated Toolchain installation on BIG-IQ Source | Edit on
Lab 1.2: Configuring SNMP for sending traps/alerts to Splunk¶
Note
Estimated time to complete: 5 minutes
This feature provides the ability for the customer to specify a message to be displayed on the BIG-IQ login page.
Lab environment access¶
If you have not yet visited the page Getting Started, please do so.
Tasks¶
Prerequisites Splunk
- This demo is using a instance of Splunk running in a container.
- Refer Send SNMP events to your Splunk deployment and Monitor files and directories with the CLI
Connect via
SSHorWeb Shellto the system Ubuntu Lamp Server. (if you use the Web Shell, login as f5student first: su - f5student).Execute the following commands to start the SNMP trap Listener:
./splunk/startSNMPtrapListener.sh
Open BIG-IQ, go to System > This Device > SNMP Configuration > SNMP Traps. Click Create.
- Name:
snmptrad - Version:
V2C - Community:
public - Destination:
10.1.1.5 - Port:
162

- The Devices and System alerts are located under Monitoring > Alerts & Notifications. It will display all triggered alerts.
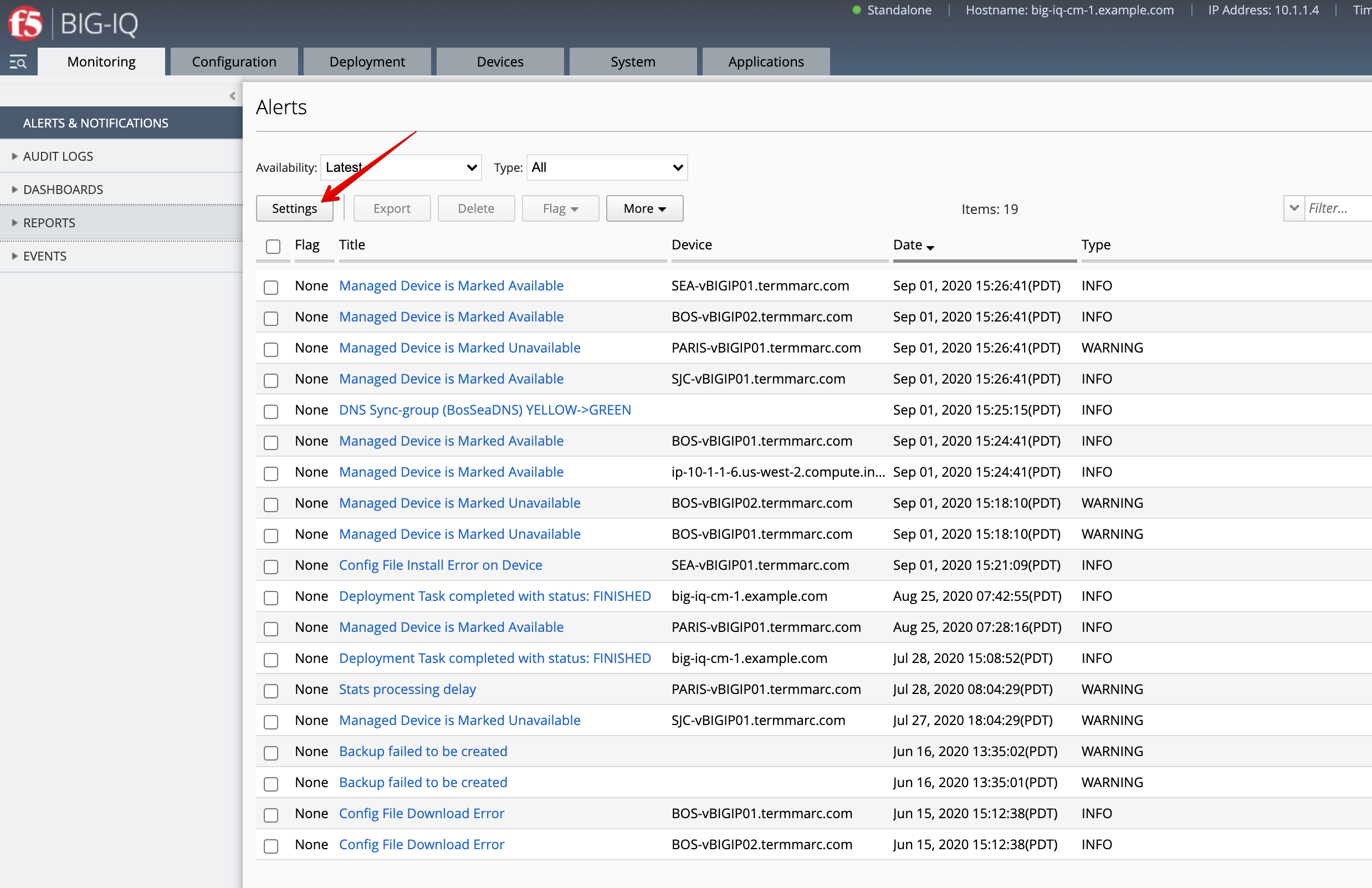
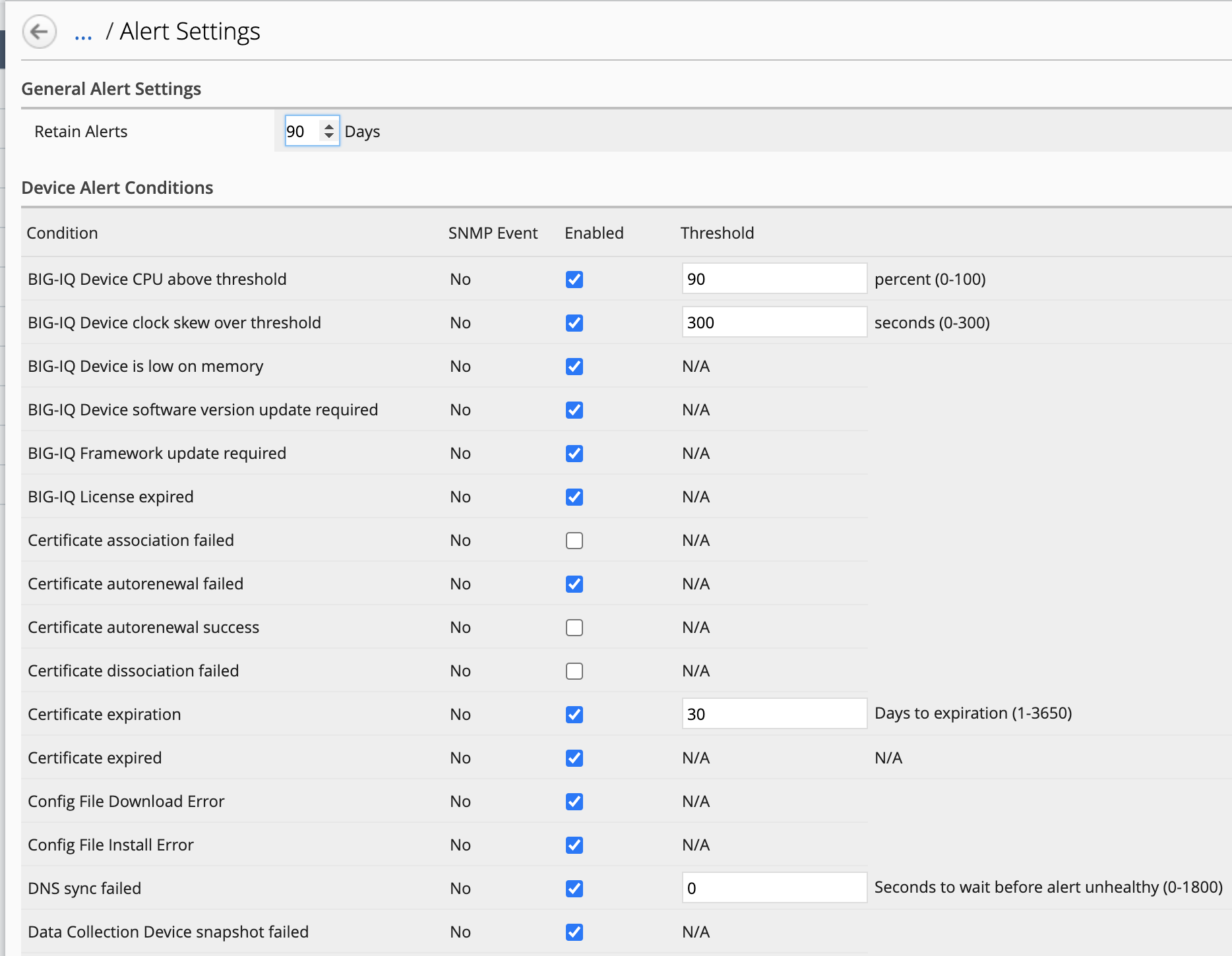
- Click on Settings to see the type of alerts available.
- From you lab deployment, look for SJC-vBIGIP01.termmarc.com device, click on Details and stop the device.
Wait for few seconds, you should coming a new alert showing the device unavailable in the Alerts list.
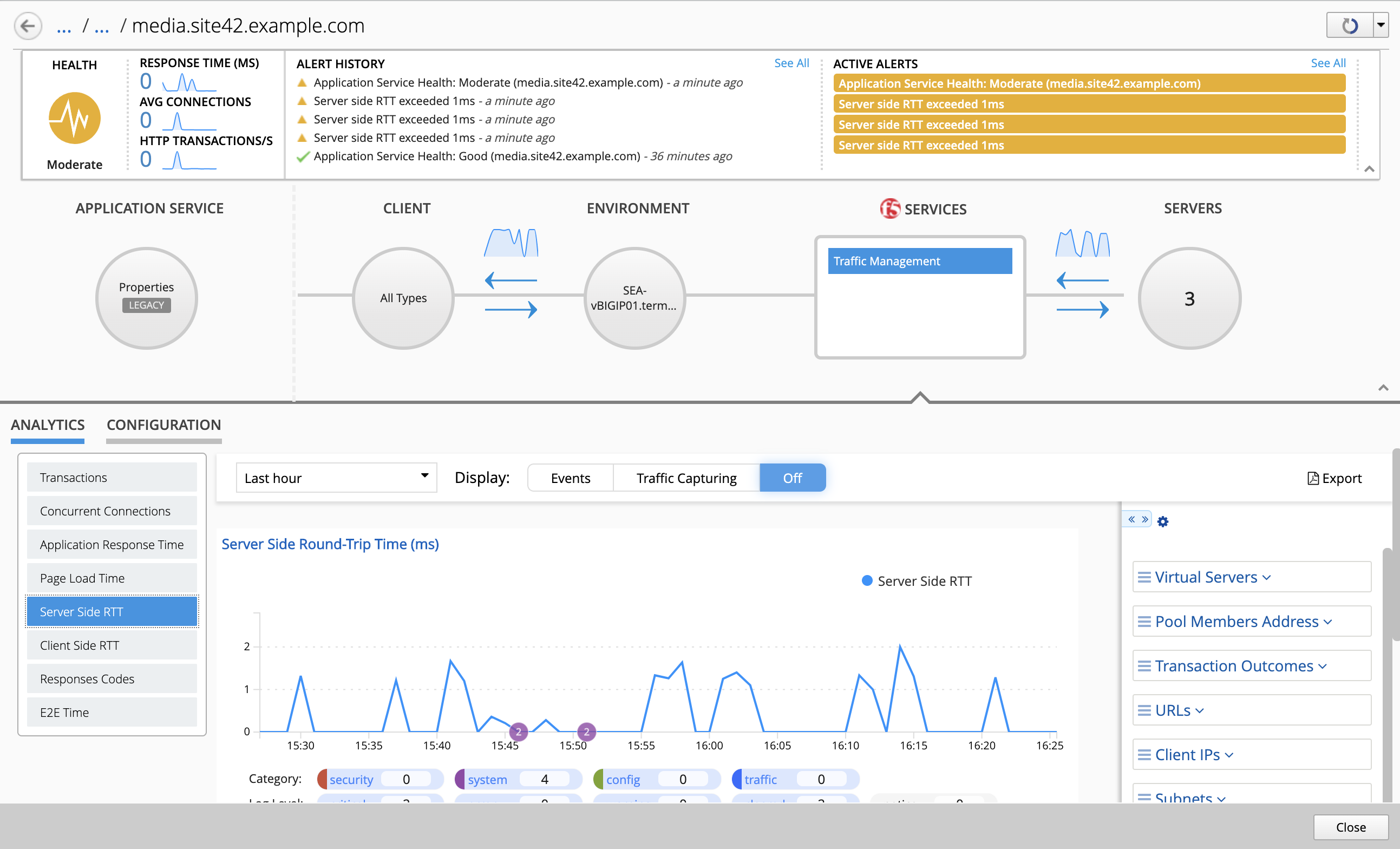
- Now, let’s have a look at the Applications Alerts. Go to Applications > Applications, click on the IT_apps Application, then on media.site42.example.com Application Service.
On the top right of the application dashboard, click on the Health button.
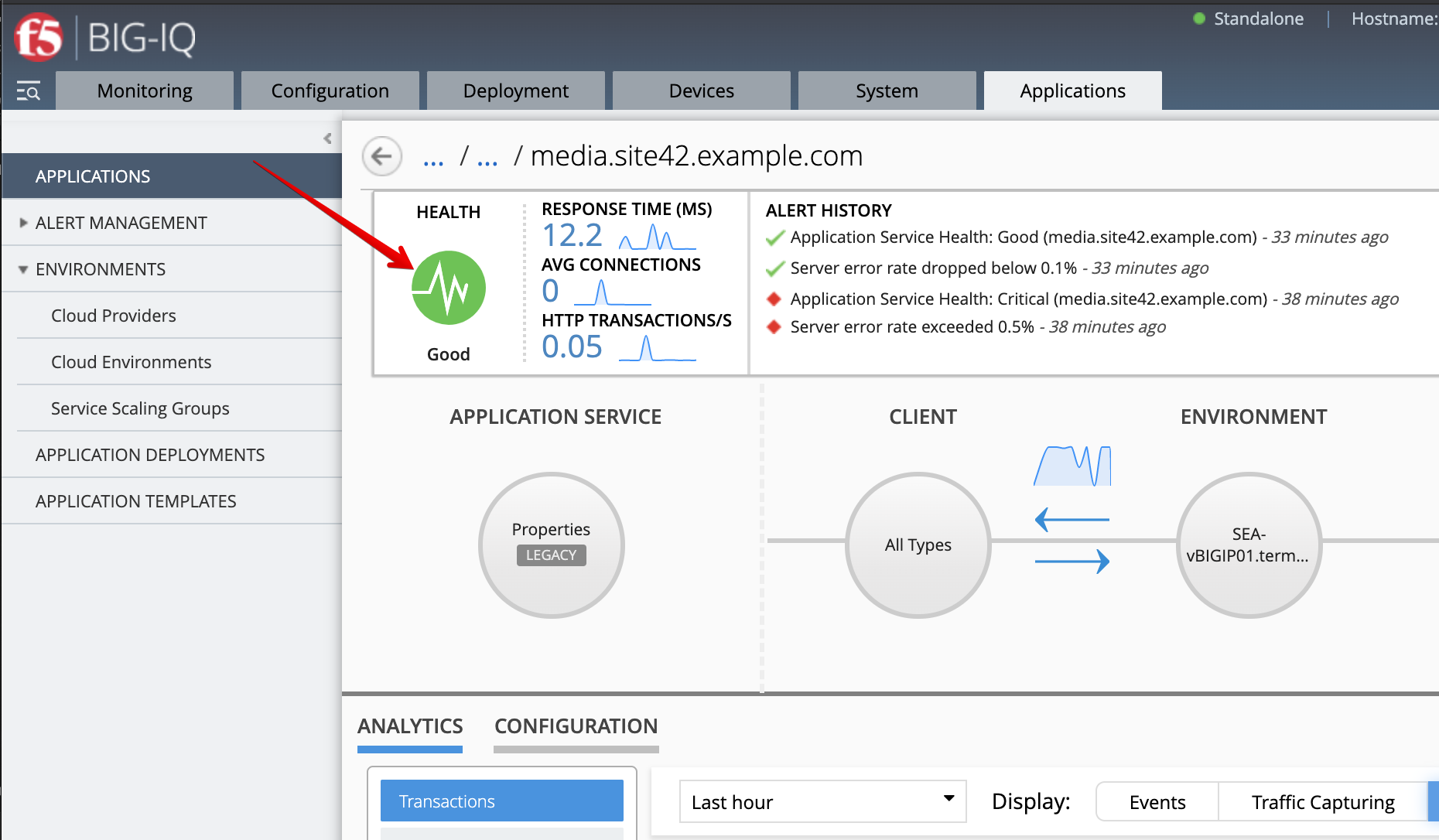
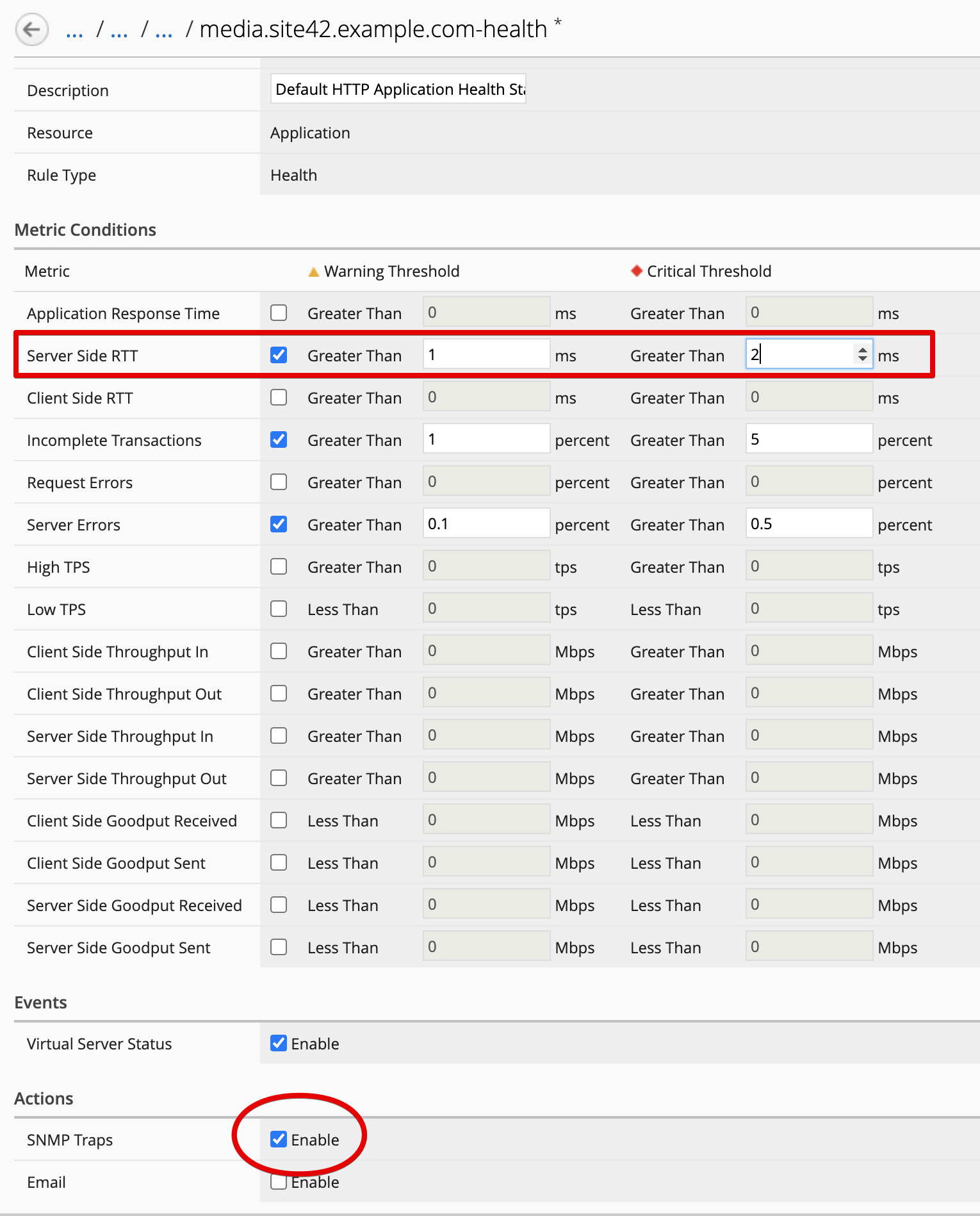
- Change the Server Site RTT warning and critical thresholds to
1msand2ms. Under Actions, enableSNMP Trap.
- Back on the Application Service dashboard, notice some new alerts are being created about Server Site RTT.
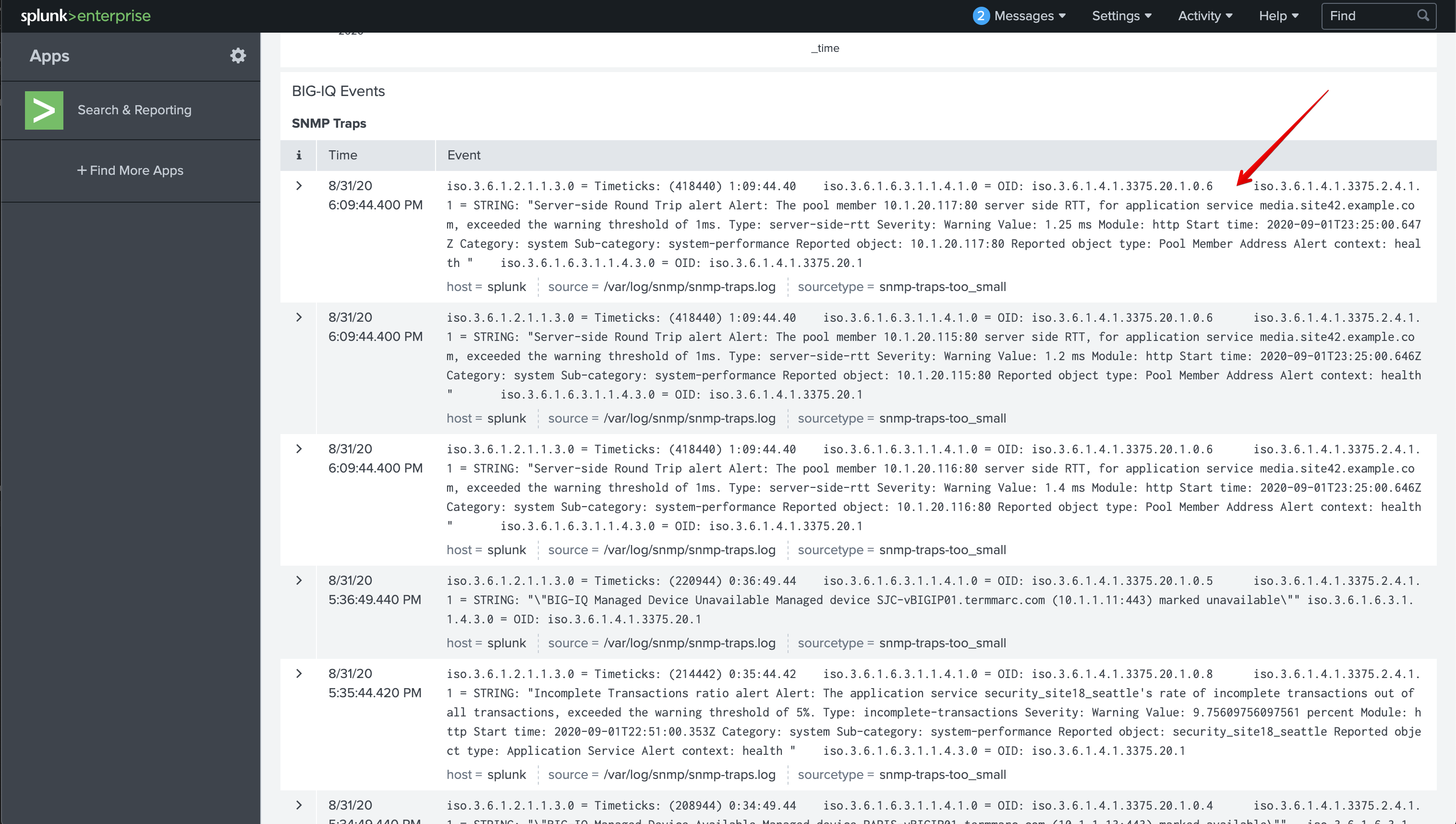
- Now, let’s open Splunk to see if any SNMP traps were received.
From you lab deployment, click on the SPLUNK button on the system Ubuntu Lamp Server.
Use
admin/purple123to authenticate.