F5 BIG-IP SSL Orchestrator Training Lab > All SSL Orchestrator Lab Guides > SSLO 101: Essential SSL Visibility with SSL Orchestrator (Agility 2022 | 2 hours) > 3. Create a Transparent Forward Proxy SSLO Source | Edit on
3.15. Enable decryption and test behavior¶
This test will demonstrate that:
Traffic is now being decrypted
The "malicious" file will be detected and blocked by the network-based scanner.
3.15.1. Enable decryption within the security policy¶
Return to SSL Orchestrator Guided Configuration.
Click on the sslo_demoL3 topology.
In the configuration summary, find the row labeled Security Policy and click on the pencil at the far right.
In the security policy, find the rule All Traffic and click on the pencil at the far right.
SSL Forward Proxy Action - select the Intercept option.
Click OK.
Click Save & Next.
Pause for a few seconds and the yellow banner shown below will appear at the very top of the Interception Rule settings.
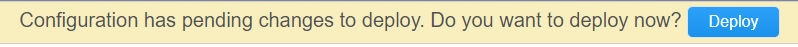
Click Deploy.
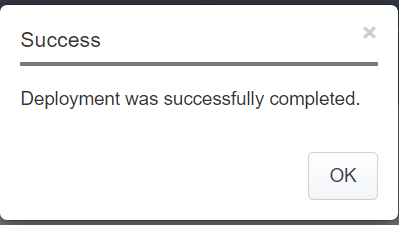
Click OK.
3.15.2. Server certificate test¶
Return to your Ubuntu client RDP session.
Open Chromium web browser on the outbound client system and open a new incognito or private browsing session. This is to ensure the browser establishes an entirely new session and does not reuse cached content.
Navigate to https://www.google.com. Once the site opens in the browser, check the server certificate of the site and verify that it is now issued by the local CA configured in SSLO. This confirms that the SSL forward proxy and certificate re-write functionality enabled by SSL Orchestrator is now working correctly.
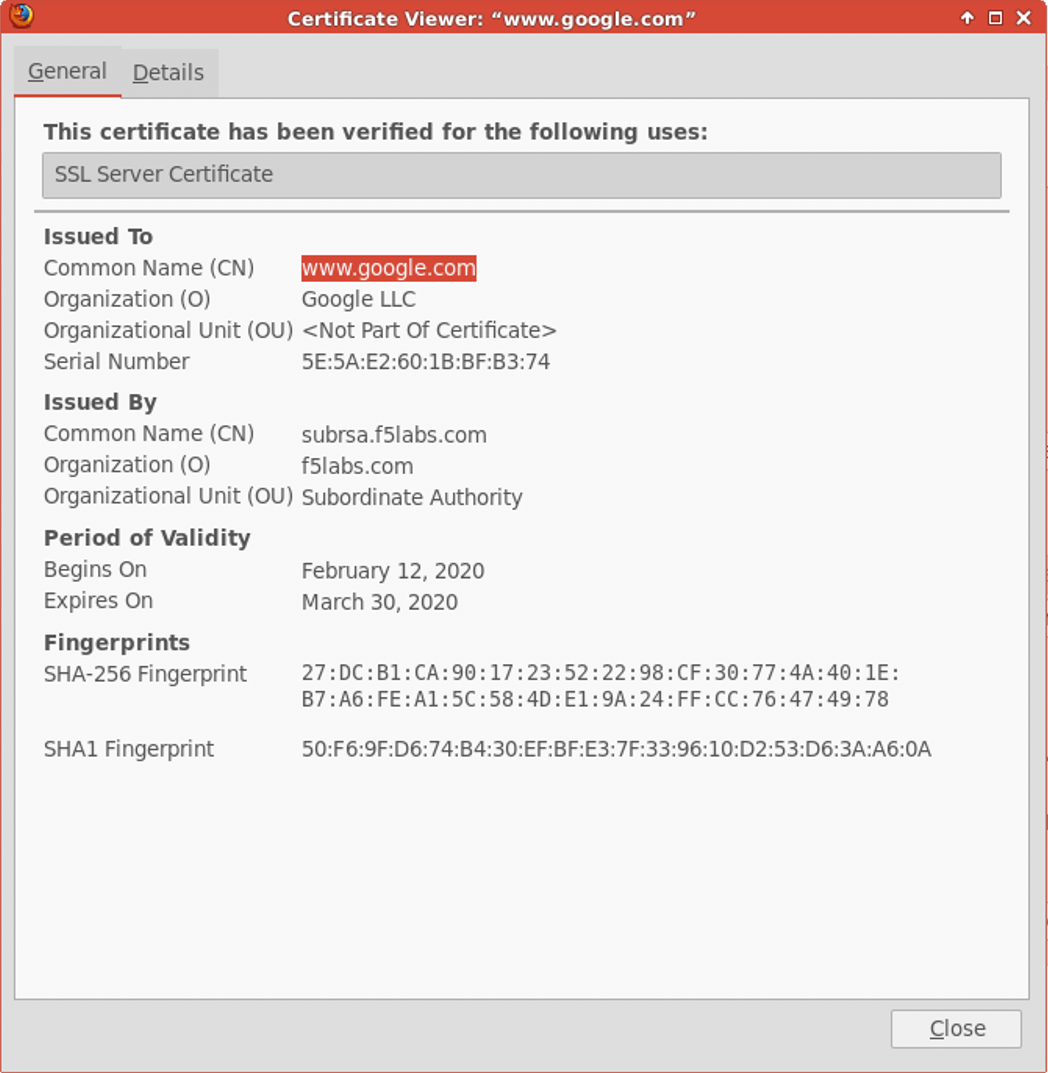
This confirms that the certificate re-write and SSL forward proxy decryption functionality provided by SSL Orchestrator has been enabled.
3.15.3. Decrypted traffic test on the security service¶
Open Chromium web browser on the outbound client system and open a new incognito or private browsing session. This is to ensure the browser establishes an entirely new session and does not reuse cached content.
Navigate once again to https://eicar.org/?page_id=3950. Scroll down to the section labeled Download area using the secure, SSL enabled protocol HTTPS and click on eicar.com.
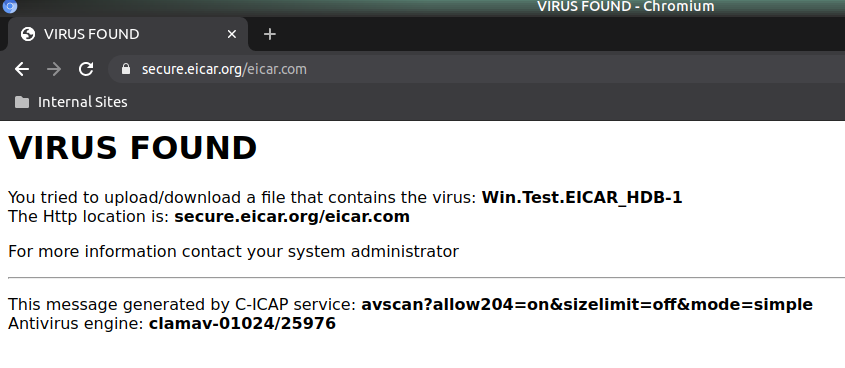
Notice that this time, the download is prevented and the user is presented a block page because the file was decrypted prior to scanning.
In the next section, you will test selective decryption based on URL category.