F5 BIG-IP SSL Orchestrator Training Lab > All SSL Orchestrator Lab Guides > SSLO 101: Essential SSL Visibility with SSL Orchestrator (Agility 2022 | 2 hours) > 3. Create a Transparent Forward Proxy SSLO Source | Edit on
3.17. View dashboard¶
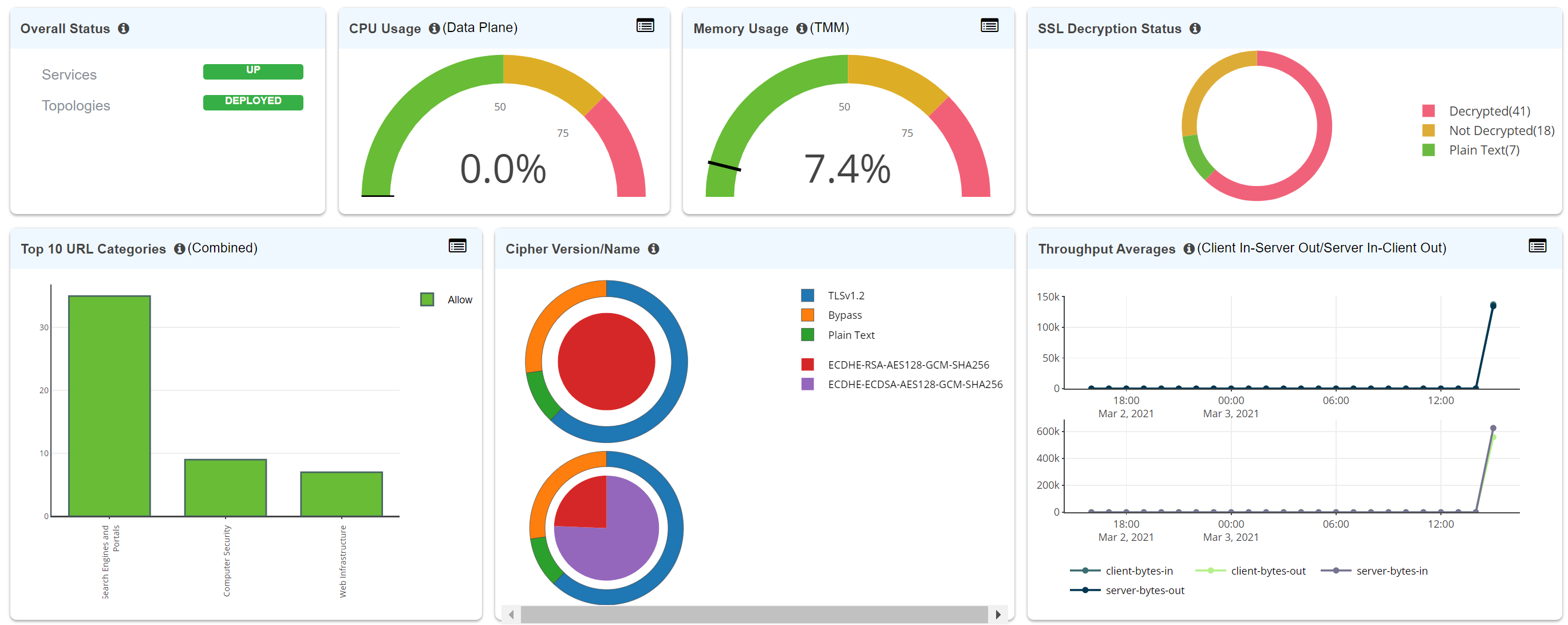
The SSL Orchestrator dashboard provides valuable at-a-glance information regarding availability, performance, TLS details, and more.
For this lab:
Navigate back to the SSL Orchestrator GUI.
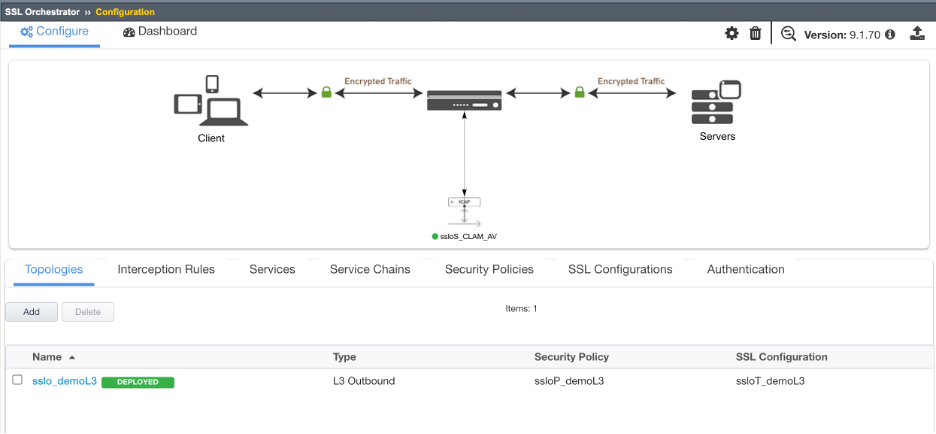
Instead of re-entering the toplogy, click on Dashboard as shown in the image below.
Review your dashboard, which should look similar to the image below.
Note
This is the end of the main section of this lab. You are welcome to proceed to the remaining optional sections if time permits.